Microsoft has patched a misconfiguration issue impacting the Azure Lively Directory (AAD) identification and accessibility administration provider that uncovered various “large-impression” applications to unauthorized accessibility.
“A single of these applications is a written content administration process (CMS) that powers Bing.com and permitted us to not only modify look for effects, but also launch substantial-impression XSS attacks on Bing consumers,” cloud security organization Wiz reported in a report. “Those people assaults could compromise users’ particular data, including Outlook e-mails and SharePoint documents.”
The issues ended up described to Microsoft in January and February 2022, next which the tech huge used fixes and awarded Wiz a $40,000 bug bounty. Redmond reported it observed no evidence that the misconfigurations ended up exploited in the wild.
The crux of the vulnerability stems from what’s called “Shared Accountability confusion,” whereby an Azure application can be improperly configured to allow for users from any Microsoft tenant, major to a likely scenario of unintended entry.
Curiously, a amount of Microsoft’s have inside apps had been discovered to show this habits, thus permitting exterior events to get browse and generate to the influenced apps.
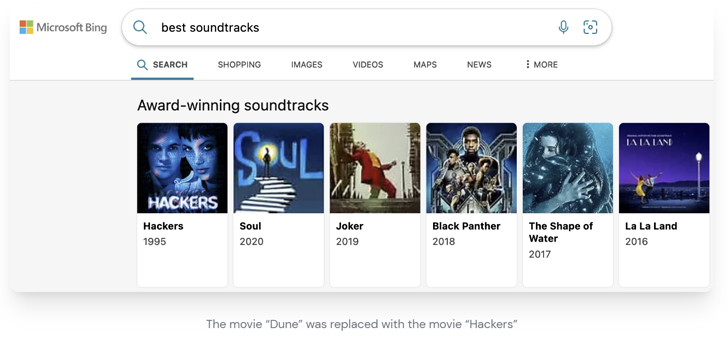
This features the Bing Trivia application, which the cybersecurity firm exploited to change research effects in Bing and even manipulate information on the homepage as portion of an attack chain dubbed BingBang.

To make matters worse, the exploit could be weaponized to induce a cross-web-site scripting (XSS) attack on Bing.com and extract a victim’s Outlook e-mail, calendars, Groups messages, SharePoint documents, and OneDrive information.
“A destructive actor with the same entry could’ve hijacked the most preferred look for effects with the similar payload and leak sensitive knowledge from thousands and thousands of end users,” Wiz researcher Hillai Ben-Sasson pointed out.
Other applications that ended up found prone to the misconfiguration issue include things like Mag Information, Central Notification Company (CNS), Get hold of Heart, PoliCheck, Energy Automate Weblog, and COSMOS.
THN WEBINARBecome an Incident Reaction Pro!
Unlock the strategies to bulletproof incident reaction – Grasp the 6-Section approach with Asaf Perlman, Cynet’s IR Chief!
You should not Miss Out – Conserve Your Seat!
The development arrives as company penetration testing company NetSPI exposed specifics of a cross-tenant vulnerability in Electricity Platform connectors that could be abused to obtain entry to delicate information.
Following responsible disclosure in September 2022, the deserialization vulnerability was resolved by Microsoft in December 2022.
The analysis also follows the launch of patches to remediate Tremendous FabriXss (CVE-2023-23383, CVSS score: 8.2), a reflected XSS vulnerability in Azure Support Cloth Explorer (SFX) that could direct to unauthenticated distant code execution.
Located this post interesting? Adhere to us on Twitter and LinkedIn to examine much more special content we submit.
Some parts of this article are sourced from:
thehackernews.com


 Cacti, Realtek, and IBM Aspera Faspex Vulnerabilities Under Active Exploitation
Cacti, Realtek, and IBM Aspera Faspex Vulnerabilities Under Active Exploitation