Unidentified menace actors are actively exploiting a not long ago patched security vulnerability in the Elementor Pro website builder plugin for WordPress.
The flaw, described as a case of broken obtain command, impacts variations 3.11.6 and before. It was addressed by the plugin maintainers in variation 3.11.7 launched on March 22.
“Enhanced code security enforcement in WooCommerce parts,” the Elementor said in its release notes. The premium plugin is believed to be used on about 12 million internet sites.
Successful exploitation of the superior-severity flaw enables an authenticated attacker to full a takeover of a WordPress site that has WooCommerce enabled.
“This would make it doable for a destructive person to flip on the registration website page (if disabled) and set the default consumer position to administrator so they can produce an account that promptly has the administrator privileges,” Patchstack said in an alert of March 30, 2023.
“Following this, they are most likely to possibly redirect the web site to another malicious domain or add a malicious plugin or backdoor to even more exploit the web site.”
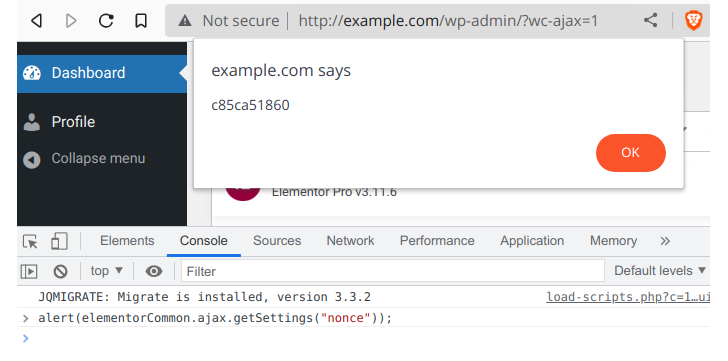
Credited with exploring and reporting the vulnerability on March 18, 2023, is NinTechNet security researcher Jerome Bruandet.
Patchstack additional pointed out that the flaw is at present staying abused in the wild from several IP addresses intending to add arbitrary PHP and ZIP archive documents.
Customers of the Elementor Pro plugin are suggested to update to 3.11.7 or 3.12., which is the newest version, as soon as doable to mitigate probable threats.
THN WEBINARBecome an Incident Response Pro!
Unlock the secrets to bulletproof incident response – Grasp the 6-Stage approach with Asaf Perlman, Cynet’s IR Leader!
Never Skip Out – Help you save Your Seat!
The advisory will come more than a 12 months immediately after the Critical Addons for Elementor plugin was located to consist of a critical vulnerability that could end result in the execution of arbitrary code on compromised internet websites.
Final 7 days, WordPress issued auto-updates to remediate a further critical bug in the WooCommerce Payments plugin that permitted unauthenticated attackers to get administrator access to susceptible web sites.
Located this report attention-grabbing? Adhere to us on Twitter and LinkedIn to study more distinctive content material we article.
Some parts of this article are sourced from:
thehackernews.com


 New Azure Flaw “Super FabriXss” Enables Remote Code Execution Attacks
New Azure Flaw “Super FabriXss” Enables Remote Code Execution Attacks