Cybersecurity scientists have disclosed a new edition of the SolarMarker malware that packs in new advancements with the goal of updating its protection evasion qualities and being less than the radar.
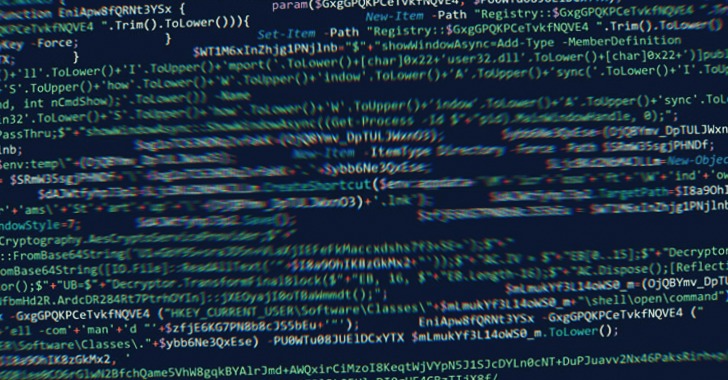
“The recent variation shown an evolution from Windows Portable Executables (EXE files) to doing the job with Windows installer offer information (MSI data files),” Palo Alto Networks Device 42 researchers stated in a report released this thirty day period. “This campaign is nonetheless in improvement and going back again to working with executables information (EXE) as it did in its before variations.”
SolarMarker, also termed Jupyter, leverages manipulated search engine optimization (Website positioning) practices as its most important infection vector. It can be acknowledged for its information and facts stealing and backdoor features, enabling the attackers to steal facts stored in web browsers and execute arbitrary commands retrieved from a distant server.
In February 2022, the operators of SolarMarker were observed working with stealthy Windows Registry methods to establish lengthy-phrase persistence on compromised methods.
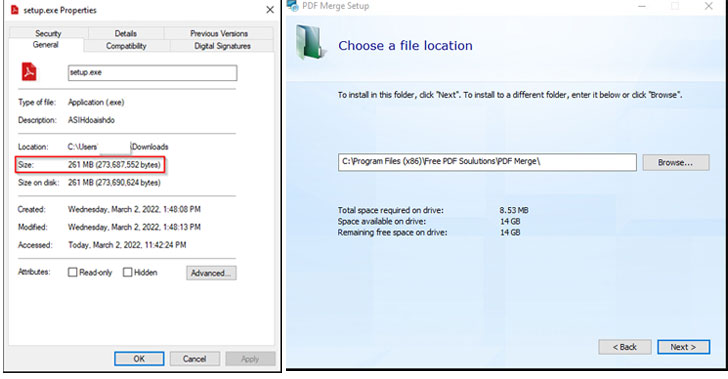
The evolving attack designs spotted by Device 42 are a continuation of this conduct, what with the infection chains using the sort of 250MB executables for PDF visitors and utilities that are hosted on fraudulent sites packed with keyword phrases and use Web optimization methods to rank them higher in the look for effects.
The large file sizing not only permits the initial stage dropper to prevent automatic analysis by antivirus engines, it is really also intended to obtain and set up the legit program though, in the track record, it activates the execution of a PowerShell installer that deploys the SolarMarker malware.
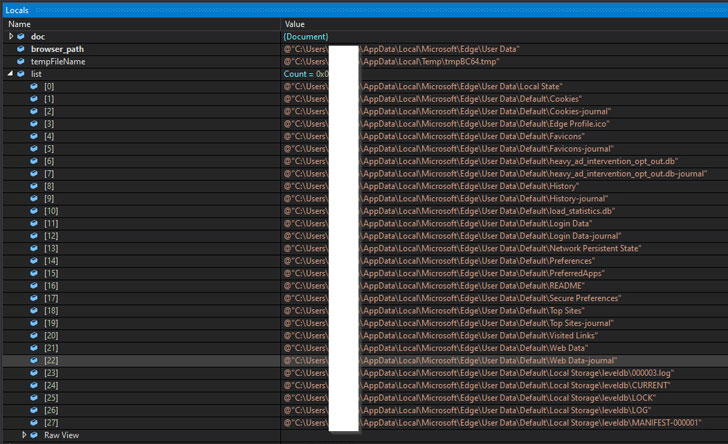
A .NET-based payload, the SolarMarker backdoor is outfitted with capabilities to perform interior reconnaissance and vacuum process metadata, all of which is exfiltrated to the remote server over an encrypted channel.

The implant also functions as a conduit to deploy the SolarMarker’s facts-stealing module on the sufferer machine. The stealer, for its aspect, can siphon autofill knowledge, cookies, passwords, and credit history card information and facts from web browsers.
“The malware invests sizeable effort into protection evasion, which is composed of techniques like signed files, massive documents, impersonation of reputable application installations and obfuscated PowerShell scripts,” the researchers stated.
Uncovered this posting exciting? Follow THN on Facebook, Twitter and LinkedIn to read through a lot more distinctive written content we put up.
Some parts of this article are sourced from:
thehackernews.com

 New Hacking Campaign Targeting Ukrainian Government with IcedID Malware
New Hacking Campaign Targeting Ukrainian Government with IcedID Malware