Elementor, a WordPress web site builder plugin with over 5 million lively installations, has been observed to be vulnerable to an authenticated remote code execution flaw that could be abused to just take over impacted web-sites.
Plugin Vulnerabilities, which disclosed the flaw last 7 days, stated the bug was introduced in edition 3.6. that was produced on March 22, 2022. About 37% of buyers of the plugin are on model 3.6.x.

“That signifies that malicious code provided by the attacker can be run by the website,” the researchers stated. “In this occasion, it is feasible that the vulnerability may possibly be exploitable by someone not logged in to WordPress, but it can quickly be exploited by anyone logged in to WordPress who has access to the WordPress admin dashboard.”
In a nutshell, the issue relates to a circumstance of arbitrary file add to affected web-sites, most likely foremost to code execution.
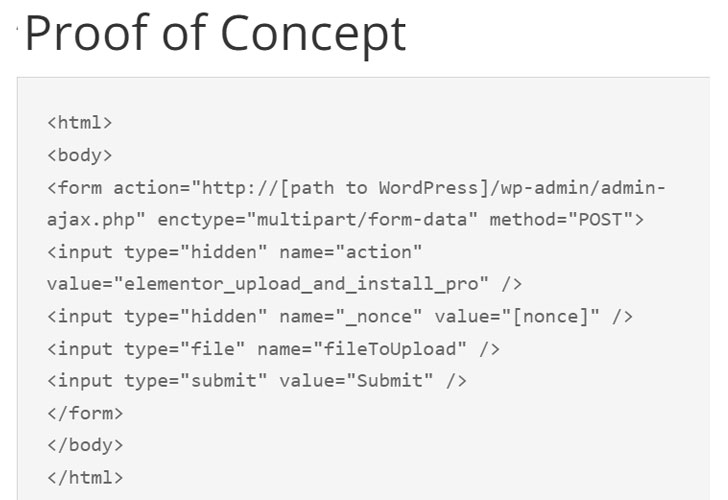
The bug has been tackled in the most recent version of Elementor, with Patchstack noting that “this vulnerability could allow for any authenticated user, no matter of their authorization, to adjust the web page title, internet site logo, alter the concept to Elementor’s theme, and worst of all, add arbitrary files to the web site.”
The disclosure comes far more than two months after Necessary Addons for Elementor was found to incorporate a critical vulnerability that could final result in the execution of arbitrary code on compromised web-sites.
Observed this report intriguing? Adhere to THN on Facebook, Twitter and LinkedIn to read through much more unique content we publish.
Some parts of this article are sourced from:
thehackernews.com


 Tesla investors say a judge found Elon Musk’s ‘funding secured’ tweet was misleading
Tesla investors say a judge found Elon Musk’s ‘funding secured’ tweet was misleading