Attackers are increasingly building use of “networkless” attack procedures focusing on cloud applications and identities. Here’s how attackers can (and are) compromising businesses – with no at any time needing to contact the endpoint or conventional networked methods and expert services.
Right before acquiring into the particulars of the attack procedures remaining utilised, let us explore why these attacks are getting much more prevalent.
SaaS adoption is altering the make-up of corporation IT
The SaaS revolution and merchandise-led progress have experienced a huge influence on the structure of company networks, and in which main business methods and data reside.
Most corporations currently are making use of tens to hundreds of SaaS purposes across small business capabilities. Some are fully SaaS-indigenous, with no traditional network to converse of, but most have adopted a hybrid product with a combination of on-premise, cloud, and SaaS solutions forming the spine of enterprise programs becoming used.
The bulk of SaaS adoption is user-driven, as opposed to centrally managed by IT, as base-up adoption is inherent to solution-led advancement. The newest knowledge from Drive Security implies that only 1 in 5 SaaS applications have been sanctioned by the enterprise. The vast majority is simply just not known and, consequently, has not been reviewed at all.
Cloud and SaaS applications are developed to be interconnected, working like the shut networks of inner company applications you may possibly have made use of in the earlier. The auto for this interconnectedness is identification.
Digital identities are more and more intricate and really hard to secure
The most fundamental sort of identity is a person account created for services you indicator up to with a username/email and password. To reduce the risk of account takeover and complexity of controlling an at any time-raising quantity of accounts, businesses are using the products and services of id companies (IdPs) to centralize obtain to apps within just a one platform and identification, using protocols like one indication on (SSO) and OAuth to manage authentication and authorization respectively.
The certain make-up of an id can fluctuate a large amount. Based on the app, it is really doable to have multiple authentication mechanisms for the exact same account – for example, through SAML, social logins (OIDC), and username and password. Even though SAML involves that admins established it up in advance for a provided app tenant, users can sign up for an app utilizing OIDC simply by making use of the “indicator in with Google” element.
In outcome this results in multiple identities tied to a single account, which can introduce a lot of confusion and complexity – for case in point, just simply because an IdP admin deletes that account, won’t suggest the app/account can’t then be accessed by applying one of the other login solutions which is been designed. This can make it hard to know what applications are in use, and what identities exist in the firm.
So, in exercise, it is really attainable to end up with a mix of the next:
- Identification providers (normally 3 for each organization on average) (e.g., Okta, Entra/Microsoft, Google)
- Applications acting as an SSO system for connected apps (e.g., Atlassian Access, Adobe Artistic Cloud)
- SaaS apps working with distinctive authentication (SAML, OIDC) and authorization (OAuth) protocols
- SaaS apps with a community username and password
- Credentials and secrets and techniques stored in password supervisor and authenticator applications (which can be in browsers, on nearby OS, and in 3rd party apps)
It can get very challenging – with most organizations acquiring 100+ apps in their inventory, resulting in hundreds of sprawled identities.
Then, relying on the OAuth scopes accepted for a provided app, permissions and workflows in just one app can influence other apps the place acceptance is granted for them to talk to a single an additional.
Identification is the glue that retains this ecosystem with each other. Nevertheless, the controls that exist to protected identification have really serious limitations. Providers generally think that all their apps and identities have MFA rolled out or all apps are driving SSO. But the truth is that only 1/3 of applications really aid SSO (and lots of of these only at the top quality tier, with a hefty price enhance). Even further, all-around 60% of unique identities (i.e., not using SSO) do not have MFA registered.
So in fact, there are significant gaps in the security controls protecting cloud identities, even though identities and cloud applications are turning into additional prevalent.
Attackers are targeting cloud id vulnerabilities
Attackers are getting note of this. According to Verizon’s 2024 DBIR, 74% of all breaches involved the human ingredient, focusing on compromised consumer accounts via human mistake, privilege misuse, use of compromised qualifications, or social engineering.
Whilst this is practically nothing new (some description of id/phishing assaults have been the best attack vector due to the fact at the very least 2013), Crowdstrike’s latest international danger report goes even further, noting that 75% of assaults to acquire entry were being malware-absolutely free, and that “cloud-mindful” assaults (deliberate rather than opportunistic focusing on of cloud expert services to compromise precise performance) increased 110%. Microsoft also notes around 4,000 password attacks for each second specifically concentrating on cloud identities, though there are tips from Google workforce that assaults on the lookout to steal session cookies (and therefore bypass MFA) happen at around the same buy of magnitude as password-centered assaults.
Hunting beyond the quantities, evidence from breaches in the community eye tells the exact tale. Risk teams like APT29/Cozy Bear/The Dukes and Scattered Spider/0ktapus show how attackers are actively focusing on IdP providers, SaaS apps, and SSO/OAuth to have out significant-profile assaults versus providers like Microsoft and Okta.
If you want to study much more about this, you can verify out this web site article tracking identification assaults seen in the wild.
Cloud apps and identities are the new land of option for attackers. Because of the shift to cloud providers, they present the exact benefit as a traditional attack designed to breach a network perimeter by using the endpoint. In a lot of methods, id alone is the new attack floor. Opposite to other security boundaries like the network or endpoint, it also presents significantly a lot less of an impediment in phrases of the controls that now exist to defend this new perimeter.
Id-based mostly assaults used to be localized to the endpoint or adjacent “identification units” like Active Directory. The target for the attacker was to breach this perimeter and go in just the organization. Now, identification is substantially additional dispersed – the gateway to an ecosystem of interconnected cloud applications and products and services, all accessed about the internet. This has noticeably shifted the magnitude of the obstacle struggling with security groups. Soon after all, it truly is considerably more difficult to quit credential-stuffing attacks towards 100 SaaS applications than the one centralized exterior VPN/webmail endpoint of yesteryear.
Cloud identities are the new perimeter
It appears to be fairly apparent that cloud identities are the new digital perimeter. This is not the future, it can be now. The only piece that is continue to to be established is what offensive approaches and tradecraft will emerge, and what the sector reaction will be in order to prevent them.
Security period Approaches of the working day Industry reaction 2000s Standard perimeter hacking Port scanners, vuln scanners, buffer overflows, web application attacks, WiFi hacking, customer/server backdoors Firewalls, DMZs, patch management, protected coding, WPA, penetration tests 2010s Endpoint is the new perimeter Phishing, office environment macros, file structure bugs, browser exploits, memory resident implants, C2 frameworks Endpoint hardening, EDR, SIEMS, red teaming, menace hunting 2020s Cloud identities are the new perimeter ??? ???
Very last calendar year, Drive Security unveiled a matrix of SaaS attack tactics on GitHub (motivated by the much more endpoint-concentrated MITRE ATT&CK Framework) that demonstrates how attackers can goal a enterprise without touching common surfaces such as the network or endpoints.
When chained collectively, these approaches help an attacker to finish an stop-to-end attack in the cloud.
Thrust has also launched a selection of weblog posts covering how these strategies can be used – the most well-liked approaches are summarized under:
TechniqueOverviewAiTM phishingAiTM phishing uses devoted tooling to act as a web proxy in between the sufferer and a reputable login portal for an application the target has obtain to, principally to make it less difficult to defeat MFA safety. By proxying in authentic-time to the focus on login portal, the adversary is provided obtain to equally a legitimate password and valid session cookies they can steal and use to hijack the session. As soon as logged-in, a target consumer will see all the real details they would be expecting to see ordinarily (e.g. their personal e-mails/files and many others) as it is a proxy of the actual application. This minimizes their prospects of realizing they have been compromised thanks to the genuine doing the job nature of the proxied software.IM phishingIM apps like Groups and Slack are a great way for attackers to evade far more stringent email-centered phishing protections all over destructive inbound links and attachments. The immediacy and authentic-time mother nature of IM can make it a handy vector for phishing assaults as buyers are much less common with these apps as shipping vectors for phishing attacks. Employing IM, it is attainable to spoof/impersonate people, use bot accounts to develop believable dialogue, abuse website link preview functionality, and retrospectively edit messages and accounts to clear up your tracks.SAMLjackingSAMLjacking is where an attacker can make use of SAML SSO configuration options for a SaaS tenant they regulate in get to redirect buyers to a destructive url of their selecting throughout the authentication procedure. This can be hugely successful for phishing as the first URL will be a reputable SaaS URL and consumers are expecting to present credentials. It can also be made use of for lateral motion if an admin account for a SaaS app is compromised, by modifying or enabling SAML, pointing the URL to a credential phishing webpage that seems like or proxies a legit authentication assistance (e.g. Google or Microsoft). The adversary can then concentrate on buyers by sending seemingly authentic backlinks to the app login website page to the tenant, which then functions in the fashion of a watering hole attack.OktajackingAn attacker can established-up their personal Okta tenant to be utilized in really convincing phishing attacks. This attack works since Okta forwards qualifications from logins for accounts tied to Advert to its personal Ad agent that operates on the goal network. Then, Okta permits the agent to report again to them about regardless of whether the login should be successful or not. This enables an attacker who has compromised an Ad agent, or is equipped to emulate a single, to both equally check login qualifications for Okta users and provide skeleton critical-like features to authenticate to Okta as any person they like. It can also be utilized likewise to SAMLjacking for lateral movement – other than you never have to have to redirect to a different malicious area.Shadow workflowsA shadow workflow is a technique for applying SaaS automation applications to offer a code execution-like process for conducting destructive steps from a genuine source working with OAuth integrations. This could be a every day export of information from shared cloud drives, automatic forwarding and deleting of emails, cloning instantaneous messages, exporting person directories — essentially just about anything that is achievable using the focus on app’s API.
Networkless attack methods in motion
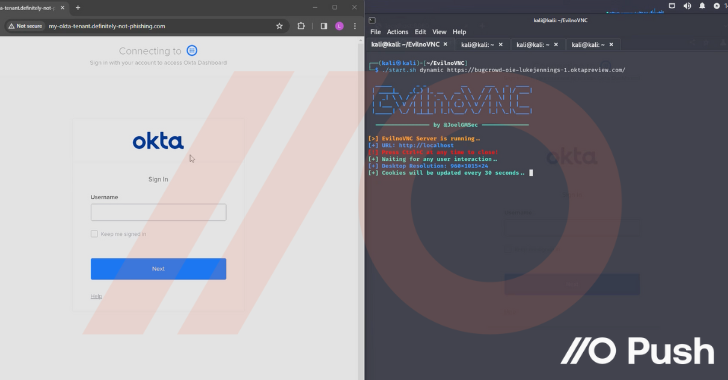
But you can find practically nothing pretty like observing them in action to have an understanding of just how impactful these techniques can be. So examine out the clip underneath from Luke Jennings, VP of R&D at Press. In this online video, he addresses:
- Initial access via AiTM phishing employing EvilNoVNC, a Browser in the Browser (BitB) phishing framework, to hijack a person Okta session
- Thieving credentials from the browser session and accessing even further applications by way of Okta SSO, configuring individuals apps to generate persistent accessibility and backdoor the apps
- Performing further more credential theft for other consumers of those apps within just the corporate tenant by abusing SAML and SWA logins
- Instantly accessing delicate data and operation in just compromised applications
Could you detect and react to this attack?
Soon after viewing what is actually attainable, it’s critical to talk to – could you detect and react to this attack state of affairs?
- Would you detect the first AiTM phish?
- How lots of people would be compromised by means of the SAMLjacking attack?
- Would you obtain all the different backdoors in various SaaS apps?
- …or just reset the password and MFA tokens for the Okta account?
- …and what about the passwords for all the non-SAML applications?
Most businesses have a security gap when it comes to id-centered assaults. This is in large portion for the reason that the controls all-around identity security are normally targeted on securing central identification methods (imagine Energetic Listing/Entra ID) as opposed to the larger sized id infrastructure as it relates to cloud apps and expert services.
Equally, the controls that businesses have invested in are mostly bypassed by these assaults. EDR applications used to safe underlying running devices have minimum presence right here for the reason that these applications are accessed in the browser – progressively touted as the new functioning system. As discussed right here, securing the id is totally important to safeguarding expert services in the cloud. And a major portion of the attack chain – for case in point, phishing tries in standard, like AiTM and BitB methods developed to bypass MFA, or password sharing throughout applications and expert services, are merely not included by endpoint security instruments, IdP logs, or SaaS logs from particular person applications and companies.
These sorts of assaults are a actual problem for several organizations suitable now mainly because they slide by way of the cracks of present security applications and services.
Intrigued in finding out a lot more?
If you want to obtain out more about identity attacks in the cloud and how to cease them, check out out Thrust Security – you can try out out their browser-dependent agent for no cost!
Observed this write-up attention-grabbing? This posting is a contributed piece from a person of our valued partners. Comply with us on Twitter and LinkedIn to go through more exceptional information we write-up.
Some parts of this article are sourced from:
thehackernews.com

 Akira Ransomware Gang Extorts $42 Million; Now Targets Linux Servers
Akira Ransomware Gang Extorts $42 Million; Now Targets Linux Servers