
Russia’s cyber assaults against Ukraine surged by 250% in 2022 when when compared to two many years ago, Google’s Menace Investigation Team (TAG) and Mandiant disclosed in a new joint report.
The focusing on, which coincided and has since persisted subsequent the country’s navy invasion of Ukraine in February 2022, focused intensely on the Ukrainian govt and armed service entities, alongside critical infrastructure, utilities, general public solutions, and media sectors.
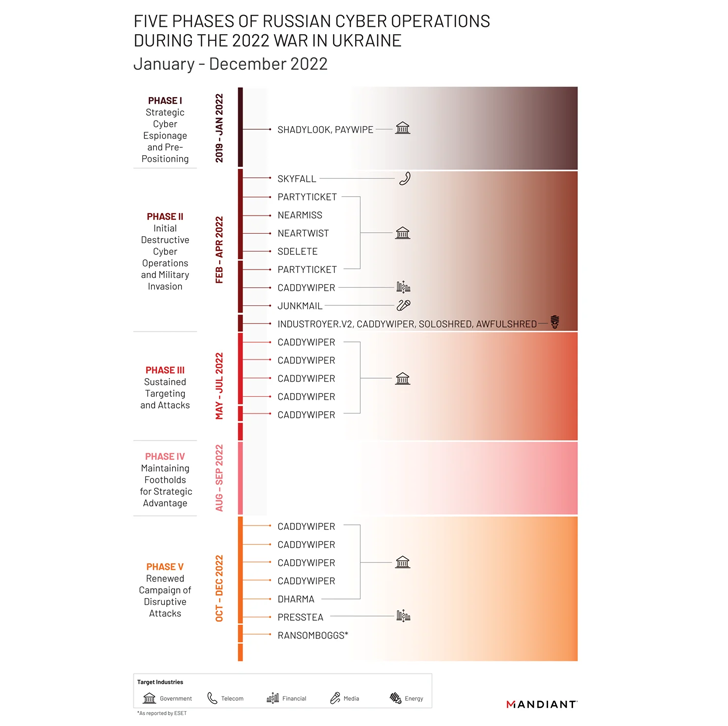
Mandiant claimed it noticed, “far more damaging cyber attacks in Ukraine throughout the very first 4 months of 2022 than in the previous 8 many years with assaults peaking all-around the get started of the invasion.”
As numerous as 6 one of a kind wiper strains – which includes WhisperGate, HermeticWiper, IsaacWiper, CaddyWiper, Industroyer2, and SDelete – have been deployed towards Ukrainian networks, suggesting a willingness on the portion of Russian risk actors to forgo persistent entry.
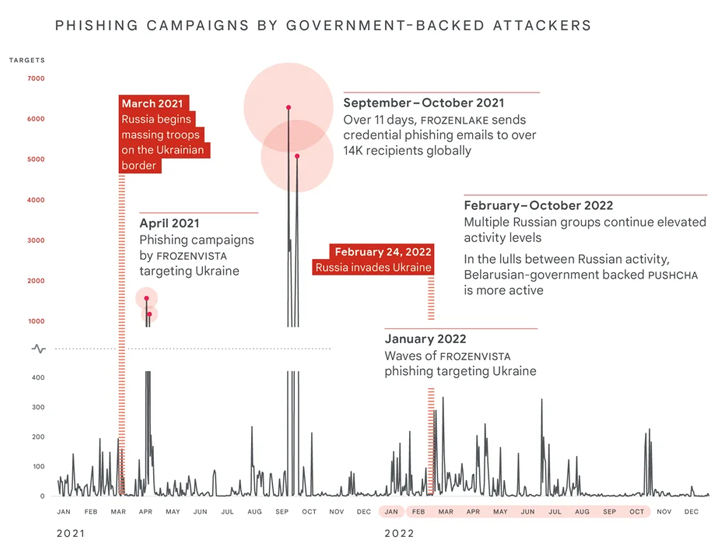
Phishing attacks aimed at NATO international locations witnessed a 300% spike in excess of the class of the very same period of time. These initiatives had been pushed by a Belarusian government-backed team dubbed PUSHCHA (aka Ghostwriter or UNC1151) that’s aligned with Russia.
“Russian federal government-backed attackers have engaged in an aggressive, multi-pronged effort to obtain a decisive wartime gain in cyberspace, frequently with mixed benefits,” TAG’s Shane Huntley noted.
Some of the critical actors involved in the attempts include FROZENBARENTS (aka Sandworm or Voodoo Bear), FROZENLAKE (aka APT28 or Fancy Bear), COLDRIVER (aka Callisto Group), FROZENVISTA (aka DEV-0586 or UNC2589), and SUMMIT (aka Turla or Venomous Bear).
The uptick in the intensity and frequency of the operations aside, the invasion has also been accompanied by the Kremlin engaging in covert and overt facts functions made to condition community notion with the goal of undermining the Ukrainian government, fracturing intercontinental assist for Ukraine, and manage domestic assistance for Russia.
“GRU-sponsored actors have made use of their entry to steal delicate information and facts and release it to the general public to further a narrative, or use that exact same access to carry out destructive cyber attacks or data operations strategies,” the tech large mentioned.
With the war splintering hacking teams above political allegiances, and in some situations, even triggering them to shut store, the advancement even more points to a “noteworthy shift in the Japanese European cybercriminal ecosystem” in a method that blurs the strains between economically enthusiastic actors and condition-sponsored attackers.
This is evidenced by the truth that UAC-0098, a risk actor that has traditionally delivered the IcedID malware, was observed repurposing its approaches to assault Ukraine as aspect of a set of ransomware assaults.
Some associates of UAC-0098 are assessed to be former members of the now-defunct Conti cybercrime group. TrickBot, which was absorbed into the Conti operation last yr prior to the latter’s shutdown, has also resorted to systematically concentrating on Ukraine.
It can be not just Russia, as the ongoing conflict has led Chinese federal government-backed attackers these as CURIOUS GORGE (aka UNC3742) and BASIN (aka Mustang Panda) to shift their emphasis in direction of Ukrainian and Western European targets for intelligence collecting.
“It is crystal clear cyber will continue to engage in an integral position in potential armed conflict, supplementing regular varieties of warfare,” Huntley said.
The disclosure arrives as the Pc Emergency Reaction Group of Ukraine (CERT-UA) warned of phishing email messages targeting organizations and institutions that purport to be critical security updates but in fact contain executables that direct to the deployment of remote desktop control application on the infected methods.
CERT-UA attributed the operation to a menace actor it tracks less than the moniker UAC-0096, which was earlier detected adopting the very same modus operandi again in late January 2022 in the months major to the war.
“A yr right after Russia released its comprehensive-scale invasion of Ukraine, Russia remains unsuccessful in bringing Ukraine less than its management as it struggles to conquer months of compounding strategic and tactical failures,” cybersecurity business Recorded Long term mentioned in a report published this thirty day period.
“Inspite of Russia’s regular military services setbacks and its failure to substantively advance its agenda by cyber operations, Russia maintains its intent to carry Ukraine beneath Russian control,” it extra, when also highlighting its “burgeoning navy cooperation with Iran and North Korea.”
Discovered this post attention-grabbing? Adhere to us on Twitter and LinkedIn to study extra exclusive content material we submit.
Some parts of this article are sourced from:
thehackernews.com


 Police Bust $41m Email Scam Gang
Police Bust $41m Email Scam Gang