Luxury lodges in the Chinese unique administrative location of Macau were being the concentrate on of a destructive spear-phishing campaign from the second half of November 2021 and through mid-January 2022.
Cybersecurity organization Trellix attributed the campaign with reasonable self confidence to a suspected South Korean state-of-the-art persistent threat (APT) tracked as DarkHotel, making on exploration formerly printed by Zscaler in December 2021.
Thought to be lively considering that 2007, DarkHotel has a background of putting “senior small business executives by uploading malicious code to their computers as a result of infiltrated resort Wi-Fi networks, as perfectly as by spear-phishing and P2P attacks,” Zscaler researchers Sahil Antil and Sudeep Singh stated. Outstanding sectors focused incorporate regulation enforcement, pharmaceuticals, and automotive companies.
The attack chains concerned distributing email messages directed to people in executive roles in the resort, this sort of as the vice president of human means, assistant supervisor, and front office supervisor, indicating that the intrusions had been aimed at employees who ended up in possession of accessibility to the hotel’s network.
In just one phishing entice sent to 17 unique hotels on December 7, the email purported to be from the Macau Governing administration Tourism Workplace and urged the victims to open up an Excel file named “信息.xls” (“info.xls”). In yet another scenario, the e-mails ended up faked to obtain details about people staying in the lodges.
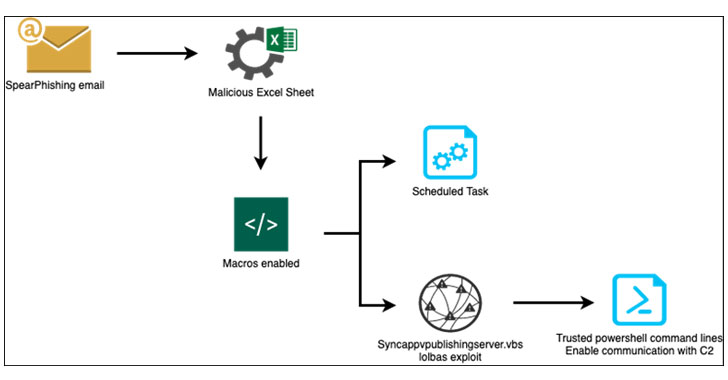
The malware-laced Microsoft Excel file, when opened, tricked the recipients into enabling macros, triggering an exploit chain to obtain and exfiltrate delicate information from the compromised devices again to a remote command-and-regulate (C2) server (“fsm-gov[.]com”) that impersonated the govt website for the Federated States of Micronesia (FSM).
“This IP was applied by the actor to drop new payloads as first levels to set up the victim natural environment for procedure details exfiltration and opportunity upcoming steps,” Trellix researchers Thibault Seret and John Fokker claimed in a report published very last week. “These payloads were being applied to concentrate on major resort chains in Macau, together with the Grand Coloane Vacation resort and Wynn Palace.”
Also noteworthy is the simple fact that the C2 server IP address has continued to continue to be lively irrespective of prior public disclosure and that it really is getting applied to provide phishing web pages for an unrelated credential harvesting attack directed at MetaMask cryptocurrency wallet people.
The campaign is said to have to fulfilled its unavoidable finish on January 18, 2022 coinciding with the rise of COVID-19 scenarios in Macau, prompting the cancelation or postponement of a variety of intercontinental trade conferences that were being set to get put in the qualified motels.
“The team was attempting to lay the basis for a foreseeable future marketing campaign involving these distinct hotels,” the scientists said. “In this marketing campaign, the COVID-19 limitations threw a wrench in the risk actor’s engine, but that doesn’t imply they have deserted this method.”
Discovered this article attention-grabbing? Adhere to THN on Facebook, Twitter and LinkedIn to browse far more special written content we article.
Some parts of this article are sourced from:
thehackernews.com




 Epic will donate two weeks of 'Fortnite' proceeds to humanitarian efforts in Ukraine
Epic will donate two weeks of 'Fortnite' proceeds to humanitarian efforts in Ukraine