Convincing email-qualifications phishing, emailed backdoors and cellular apps are all component of the groups newest work from armed service and government targets.
The SideWinder advanced persistent threat (APT) group has mounted a contemporary phishing and malware initiative, employing current territory disputes among China, India, Nepal and Pakistan as lures. The target is to obtain sensitive information from its targets, largely positioned in Nepal and Afghanistan.
According to an analysis, SideWinder normally targets victims in South Asia and surroundings – and this hottest marketing campaign is no exception. The targets here contain several government and military models for international locations in the area researchers explained, together with the Nepali Ministries of Defense and Foreign Affairs, the Nepali Army, the Afghanistan Nationwide Security Council, the Sri Lankan Ministry of Protection, the Presidential Palace in Afghanistan and extra.
The effort and hard work mainly helps make use of respectable-on the lookout webmail login webpages, aimed at harvesting credentials. Scientists from Pattern Micro explained that these internet pages were being copied from their victims’ precise webmail login webpages and subsequently modified for phishing. For illustration, “mail-nepalgovnp[.]duckdns[.]org” was produced to fake to be the actual Nepal government’s area, “mail[.]nepal[.]gov[.]np”.
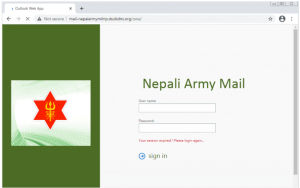
Convincing-wanting phishing web site. Resource: Development Micro.
Interestingly, just after credentials are siphoned off and the customers “log in,” they are both sent to the legitimate login web pages or, they are redirected to distinct paperwork or information webpages, similar either to COVID-19 or political fodder.
Researchers explained some of the internet pages consist of a May perhaps article entitled “India Need to Realise China Has Almost nothing to Do With Nepal’s Stand on Lipulekh” and a document referred to as “Ambassador Yanchi Dialogue with Nepali_Media.pdf,” which gives an interview with China’s ambassador to Nepal concerning Covid-19, the Belt and Highway Initiative, and territorial issues in the Humla district.
Espionage Energy
The campaign also involves a malware factor, with malicious paperwork delivered by way of email that are bent on putting in a cyberespionage-aimed backdoor. And, there was evidence that the team is setting up a mobile start to compromise wi-fi devices.
“We discovered a server made use of to supply a destructive .lnk file and host many credential-phishing webpages,” wrote researchers, in a Wednesday putting up. “We also uncovered many Android APK information on their phishing server. While some of them are benign, we also found out destructive information established with Metasploit.”
Email Infection Regimen
On the email front, scientists observed that many destructive original information are getting used in the campaign, together with a .lnk file that in change downloads an .rtf file and drops a JavaScript file on the target’s computer system and a .zip file made up of a .lnk file that in switch downloads an .hta file (with JavaScript).
“All of these situations close up with possibly the downloading or dropping of files and then the execution of JavaScript code, which is a dropper employed to put in the major backdoor moreover stealer,” scientists discussed.
The downloaded .rtf data files in the chain in the meantime exploit the CVE-2017-11882 vulnerability the exploit permits attackers to automatically operate destructive code with out requiring person interaction.
The flaw affects all unpatched versions of Microsoft Office environment, Microsoft Windows and architecture styles dating back to 2000. Whilst it was patched in November 2017, Microsoft warned as late as previous 12 months that email strategies had been spreading destructive .rtf data files boobytrapped with an exploit for it.
“The CVE-2017-11882 vulnerability was preset in 2017, but to this day, we still observe the exploit in attacks,” Microsoft Security Intelligence tweeted in 2019. “Notably, we observed amplified activity in the previous number of months. We strongly suggest implementing security updates.”
In this case, the boobytrapped .rtf drops a file named 1.a, which is a JavaScript code snippet. This spots the backdoor and stealer into a folder in ProgramData and immediately executes it, or produces a scheduled endeavor to execute the dropped information at a later time, Pattern Micro located.
“The material of the freshly produced folder contains a few data files, together with Rekeywiz, which is a genuine Windows application,” analysts described. “This software loads numerous procedure DLL libraries, including…a bogus DUser.dll [that] decrypts the primary backdoor + stealer from the .tmp file in the exact listing.”
After decryption, the payload collects method information and facts and uploads it to the command-and-manage server (C2), before location about stealing qualified file forms.
“[This] includes data this kind of as privileges, consumer accounts, computer program information, antivirus courses, functioning processes, processor information, functioning system data, time zone, mounted Windows updates, network data, list of directories in People%USERNAME%Desktop, Customers%USERNAME%Downloads, Consumers%USERNAME%Documents, Customers%USERNAME%Contacts, as well as information and facts on all drives and mounted apps,” Pattern Micro explained.
Mobile Campaign Pending?
The scientists saw numerous cellular apps that have been under advancement. Some contained no destructive code (still) for instance, a cell app named “OpinionPoll” was lurking on the server, purporting to be a study application for gathering views pertaining to the Nepal-India political map dispute.
Many others contained malicious capabilities but appeared unfinished.
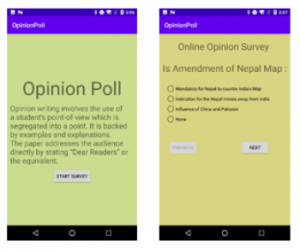
Several cell apps surface to be under progress. Resource: Trend Micro.
“While we were being not able to retrieve the payload, according to the Manifest that requests many privacy-connected permissions like place, contacts, simply call logs, and many others., we can infer that it goes following the user’s non-public knowledge,” researchers wrote.
SideWinder has utilized malicious applications as part of its procedure before, disguised as photography and file manager tools to entice people into downloading them. The moment downloaded into the user’s cell device, they exploited the CVE-2019-2215 and MediaTek-SU vulnerabilities for root privileges.
In this situation, “we think these purposes are nevertheless underneath advancement and will very likely be utilized to compromise mobile products in the long term,” scientists noted.
SideWinder has active throughout late 2019 and in 2020, in accordance to the organization, acquiring been spotted applying the Binder exploit to attack mobile devices. Trend Micro mentioned the group also released attacks before this year towards Bangladesh, China and Pakistan, working with lure documents linked to COVID-19.
“As seen with their phishing assaults and their cell machine tools’ steady development, SideWinder is very proactive in applying trending subject areas like COVID-19 or different political issues as a social-engineering system to compromise their targets,” the company concluded. “Therefore, we recommend that people and businesses be vigilant.”
Set Ransomware on the Run: Save your place for “What’s Future for Ransomware,” a FREE Threatpost webinar on Dec. 16 at 2 p.m. ET. Find out what’s coming in the ransomware globe and how to battle back.
Get the most up-to-date from John (Austin) Merritt, Cyber Danger Intelligence Analyst at Electronic Shadows Limor Kessem, Executive Security Advisor, IBM Security and Israel Barak, CISO at Cybereason, on new kinds of assaults. Subjects will include things like the most hazardous ransomware danger actors, their evolving TTPs and what your group wants to do to get forward of the upcoming, unavoidable ransomware attack. Sign-up here for the Wed., Dec. 16 for this LIVE webinar.
Some parts of this article are sourced from:
threatpost.com


 Why IBM’s AI Fact Sheets should be the industry standard
Why IBM’s AI Fact Sheets should be the industry standard