A new wave of a cell surveillance campaign has been observed concentrating on the Uyghur local community as component of a extensive-standing spy ware operation active considering that at minimum 2015, cybersecurity researchers disclosed Thursday.
The intrusions, initially attributed to a risk actor named Scarlet Mimic back again in January 2016, is reported to have encompassed 20 distinct variants of the Android malware, which had been disguised as e-book, photos, and an audio version of the Quran.
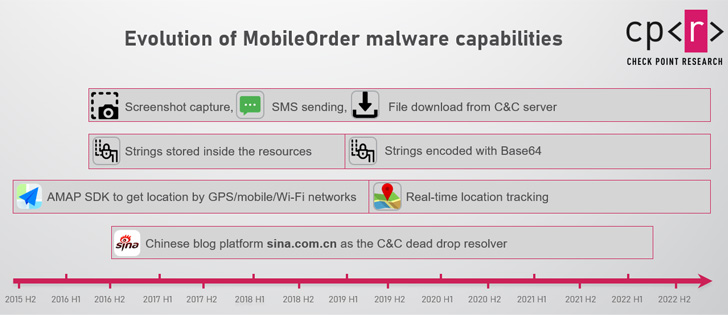
The malware, whilst relatively unsophisticated from a specialized standpoint, comes with extensive capabilities to steal sensitive data from an infected gadget, mail SMS messages on the victim’s behalf, make phone calls, and track their areas.

Also, it permits the recording of incoming and outgoing phone calls as effectively as bordering audio.
“All this would make it a impressive and hazardous surveillance device,” Israeli cybersecurity organization Test Place said in a technological deepdive, calling the spyware MobileOrder.
It is really value noting that a aspect of the marketing campaign was not long ago disclosed by scientists from the MalwareHunterTeam and Cyble, in which a ebook written by the exiled Uyghur leader Dolkun Isa was used as a entice to supply the malware.
Check out Position explained it observed MobileOrder artifacts in the wild ideal from 2015 to mid-August 2022, with the exception of 2021, when none were being detected.
Attack campaigns likely entail the use of social engineering techniques to trick unsuspecting victims into launching malicious applications that reference seemingly innocuous files, shots, and audio information.
These applications include a wide range of baits, including a PDF about guerrilla warfare and images similar to the deployment of paramilitary forces in Ürümqi, the money of the Xinjiang Uyghur Autonomous Region, in the aftermath of the deadly April 2014 attack.
Opening the rogue app, in flip, launches a decoy doc built to distract the goal from noticing the destructive actions in the history.
“Some of the variations also talk to for System Admin and root entry, which not only gives the malware entire entry to the unit, but also stops the victim from quickly uninstalling the software,” the researchers claimed.

Other capabilities supported by MobileOrder include things like executing a distant shell and even dropping more Android Offer (APK) data files.
The campaign’s attribution to Scarlet Mimic, for every Look at Issue, stems from crystal clear code overlaps, shared infrastructure, and the identical victimology designs.
On top of that, the ongoing use of MobileOrder signals a change in attack vector from desktop to cell surveillance, what with the actor formerly joined to a Windows malware named Psylo Trojan.
When it can be not very clear which of these attacks throughout the earlier seven many years have been productive, the really actuality that the malware authors are continuing to deploy the adware is an indication that some of these efforts have paid out off.
“The persistence of the campaign, the evolution of the malware and the persistent emphasis on targeting certain populations reveal that the group’s operations above the decades are prosperous to some extent,” Verify Position claimed.
Identified this article exciting? Abide by THN on Fb, Twitter and LinkedIn to examine much more distinctive articles we article.
Some parts of this article are sourced from:
thehackernews.com


 Morgan Stanley Fined $35m By SEC For Data Security Lapse
Morgan Stanley Fined $35m By SEC For Data Security Lapse