A earlier undocumented risk actor of unknown origin has been linked to assaults focusing on telecom, internet support providers, and universities throughout various countries in the Center East and Africa.
“The operators are extremely knowledgeable of operations security, taking care of thoroughly segmented infrastructure per target, and quickly deploying intricate countermeasures in the presence of security options,” scientists from SentinelOne claimed in a new report.

The cybersecurity agency codenamed the team Metador in reference to a string “I am meta” in a person of their malware samples and simply because of Spanish-language responses from the command-and-handle (C2) servers.
The risk actor is stated to have generally targeted on the enhancement of cross-platform malware in its pursuit of espionage aims. Other hallmarks of the marketing campaign are the constrained amount of intrusions and extended-time period entry to targets.
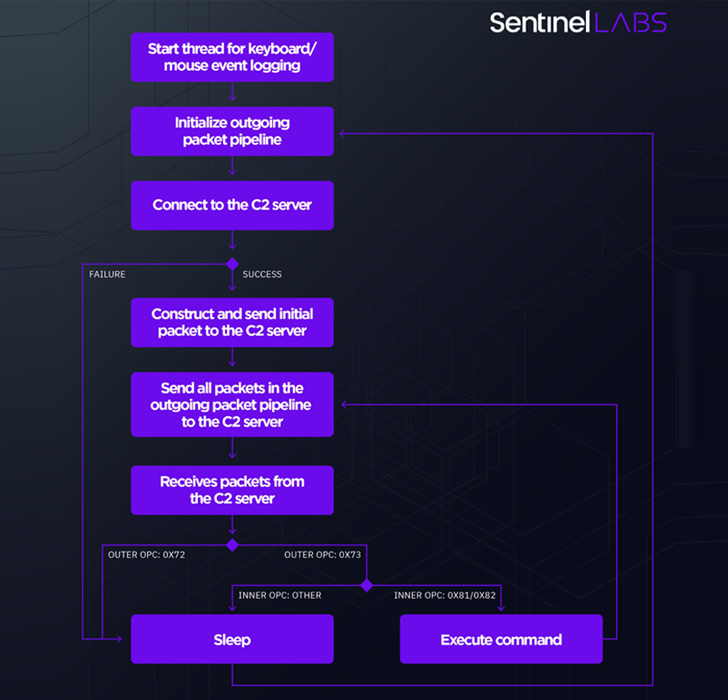
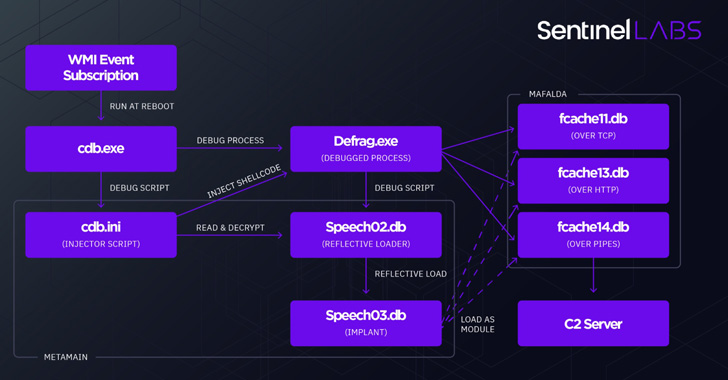
This consists of two different Windows malware platforms termed metaMain and Mafalda that are expressly engineered to run in-memory and elude detection. metaMain also functions as a conduit to deploy Mafalda, a versatile interactive implant supporting 67 instructions.
metaMain, for its aspect, is feature-rich on its have, enabling the adversary to sustain lengthy-expression accessibility, log keystrokes, down load and upload arbitrary data files, and execute shellcode.
In a signal that Mafalda is currently being actively managed by its builders, the malware gained help for 13 new instructions involving two variants compiled in April and December 2021, incorporating choices for credential theft, network reconnaissance, and file system manipulation.
Attack chains have more involved an unidentified Linux malware which is used to obtain details from the compromised ecosystem and funnel it back again to Mafalda. The entry vector made use of to aid the intrusions is unidentified as nonetheless.
What is actually more, references in the internal command’s documentation for Mafalda propose a clear separation of duties amongst the builders and operators. Ultimately even though, Metador’s attribution continues to be a “garbled thriller.”
“Additionally, the specialized complexity of the malware and its energetic growth propose a well-resourced team equipped to purchase, keep and lengthen several frameworks,” scientists Juan Andres Guerrero-Saade, Amitai Ben Shushan Ehrlich, and Aleksandar Milenkoski noted.
Discovered this posting exciting? Stick to THN on Facebook, Twitter and LinkedIn to read more exceptional written content we submit.
Some parts of this article are sourced from:
thehackernews.com

 Affirm's pay-over-time option comes to Canada through Amazon
Affirm's pay-over-time option comes to Canada through Amazon