In a new joint cybersecurity advisory, U.S. cybersecurity and intelligence agencies have warned about the use of Maui ransomware by North Korean governing administration-backed hackers to goal the health care sector considering the fact that at the very least May well 2021.
“North Korean point out-sponsored cyber actors employed Maui ransomware in these incidents to encrypt servers responsible for healthcare services—including digital wellness records services, diagnostics companies, imaging companies, and intranet solutions,” the authorities noted.
The notify arrives courtesy of the U.S. Cybersecurity and Infrastructure Security Company (CISA), the Federal Bureau of Investigation (FBI), and the Section of the Treasury.
Cybersecurity organization Stairwell, whose conclusions fashioned the basis of the advisory, said the lesser-recognised ransomware loved ones stands out because of a lack of various critical capabilities generally associated with ransomware-as-a-provider (RaaS) teams.
This contains the absence of “embedded ransom observe to supply recovery guidance or automatic signifies of transmitting encryption keys to attackers,” security researcher Silas Cutler said in a complex overview of the ransomware.
Alternatively, assessment of Maui samples implies that the malware is created for guide execution by a remote actor via a command-line interface, employing it to concentrate on distinct files on the infected machine for encryption.
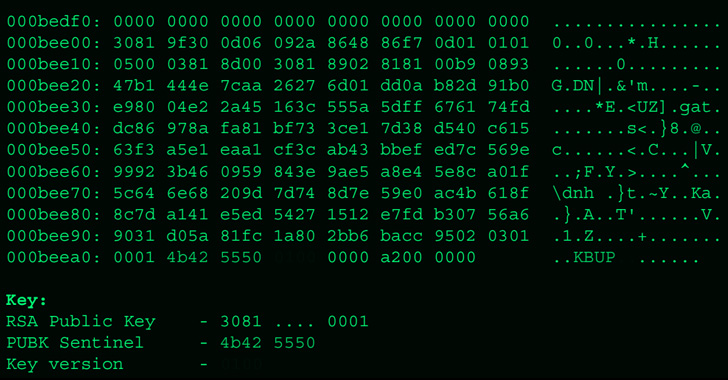
Moreover encrypting concentrate on data files with AES 128-little bit encryption with a special key, each individual of these keys is, in flip, encrypted with RSA applying a key pair created the initially time when Maui is executed. As a third layer of security, the RSA keys are encrypted working with a difficult-coded RSA general public important that is one of a kind to each marketing campaign.
What sets Maui aside from other regular ransomware choices is also the actuality that it is not presented as a service to other affiliates for use in return for a share of financial profits.
In some instances, the ransomware incidents are stated to have disrupted overall health services for prolonged periods of time. The preliminary an infection vector utilised to conduct the intrusions is not known as still.
It can be really worth noting that the marketing campaign is predicated on the willingness of healthcare entities to shell out ransoms to rapidly get better from an attack and make certain uninterrupted obtain to critical companies. It’s the newest indicator of how North Korean adversaries are adapting their techniques to illegally produce a continual stream of profits for the hard cash-strapped country.

According to the Sophos’ Condition of Ransomware in Health care 2022 report, 61% of health care companies surveyed opted to settle in contrast with the world-wide regular of 46%, with only 2% of individuals that paid out the ransom in 2021 getting their finish information back.
That said, the use of a manually operated ransomware spouse and children by an APT team also raises the likelihood that the procedure could be a diversionary tactic built to act as a go over for other malicious motives, as a short while ago noticed in the circumstance of Bronze Starlight.
“Nation point out-sponsored ransomware attacks have become usual intercontinental functions of aggression,” Peter Martini, co-founder of iboss, reported in a statement. “Regretably, North Korea precisely has proven it is very willing to indiscriminately focus on a variety of industries, which include healthcare, to safe untraceable cryptocurrency that is funding its nuclear weapons software.”
Found this short article fascinating? Stick to THN on Facebook, Twitter and LinkedIn to examine extra exclusive content material we submit.
Some parts of this article are sourced from:
thehackernews.com

 Samsung’s Galaxy Watch5 leaks in full ahead of expected August launch
Samsung’s Galaxy Watch5 leaks in full ahead of expected August launch