A computer software bug launched in Apple Safari 15’s implementation of the IndexedDB API could be abused by a destructive web site to keep track of users’ on the web action in the web browser and worse, even expose their identity.
The vulnerability, dubbed IndexedDB Leaks, was disclosed by fraud security software package firm FingerprintJS, which claimed the issue to the iPhone maker on November 28, 2021.
IndexedDB is a lower-amount JavaScript software programming interface (API) offered by web browsers for taking care of a NoSQL databases of structured data objects these kinds of as data files and blobs.

“Like most web storage solutions, IndexedDB follows a very same-origin plan,” Mozilla notes in its documentation of the API. “So whilst you can access saved facts inside of a domain, you can not obtain info throughout unique domains.”
Identical-origin is a basic security mechanism that makes certain that sources retrieved from distinct origins — i.e., a combination of the plan (protocol), host (area), and port range of a URL — are isolated from just about every other. This correctly signifies that “https://instance[.]com/” and “https://example[.]com/” are not of the exact same origin due to the fact they use distinctive strategies.
By proscribing how a script loaded by a person origin can interact with a useful resource from one more origin, the notion is to sequester perhaps destructive scripts and reduce probable attack vectors by preventing a rogue web-site from functioning arbitrary JavaScript code to read through info from one more domain, say, an email services.
But that is not the case with how Safari handles the IndexedDB API in Safari across iOS, iPadOS, and macOS.
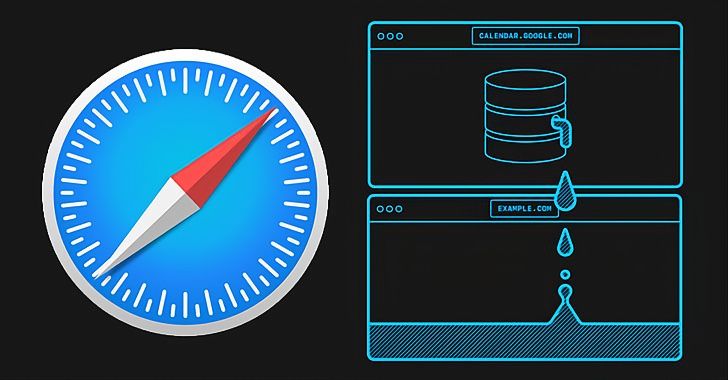
“In Safari 15 on macOS, and in all browsers on iOS and iPadOS 15, the IndexedDB API is violating the similar-origin plan,” Martin Bajanik explained in a compose-up. “Just about every time a internet site interacts with a database, a new (empty) database with the similar title is designed in all other lively frames, tabs, and windows within just the same browser session.”
A consequence of this privacy violation is that it lets internet websites to study what other sites a consumer is visiting in various tabs or windows, not to point out specifically discover buyers on Google expert services expert services like YouTube and Google Calendar as these websites generate IndexedDB databases that involve the authenticated Google Consumer IDs, which is an inner identifier that uniquely identifies a one Google account.
“Not only does this indicate that untrusted or malicious web-sites can study a user’s identification, but it also lets the linking jointly of many different accounts applied by the exact same consumer,” Bajanik explained.

To make issues even worse, the leakage also influences Non-public Browsing manner in Safari 15 ought to a user go to multiple various sites from in the identical tab in the browser window. We have attained out to Apple for further more comment, and we will update the tale if we hear back again.
“This is a massive bug,” developer advocate for Google Chrome Jake Archibald tweeted. “On OSX, Safari customers can (temporarily) change to a different browser to keep away from their knowledge leaking throughout origins. iOS consumers have no such decision, because Apple imposes a ban on other browser engines.”
Located this short article attention-grabbing? Comply with THN on Fb, Twitter and LinkedIn to examine much more exclusive articles we write-up.
Some parts of this article are sourced from:
thehackernews.com

 A New Destructive Malware Targeting Ukrainian Government and Business Entities
A New Destructive Malware Targeting Ukrainian Government and Business Entities