Cybersecurity groups from Microsoft on Saturday disclosed they determined proof of a new damaging malware procedure concentrating on govt, non-financial gain, and information technology entities in Ukraine amid brewing geopolitical tensions between the nation and Russia.
“The malware is disguised as ransomware but, if activated by the attacker, would render the contaminated personal computer method inoperable,” Tom Burt, company vice president of buyer security and have faith in at Microsoft, stated, including the intrusions were being aimed at federal government businesses that provide critical govt branch or emergency reaction features.
Also focused is an IT firm that “manages internet websites for public and private sector shoppers, like government organizations whose websites were being recently defaced,” Burt observed.
The computing huge, which very first detected the malware on January 13, attributed the assaults to an emerging threat cluster codenamed “DEV-0586,” with no noticed overlaps in methods and procedures to other previously documented groups. It further more stated the malware was observed on dozens of impacted units, a range it expects to increase as the investigation proceeds.
In accordance to Microsoft Menace Intelligence Middle (MSTIC) and Microsoft Electronic Security Device (DSU), the attack chain is a two-phase method that involves —
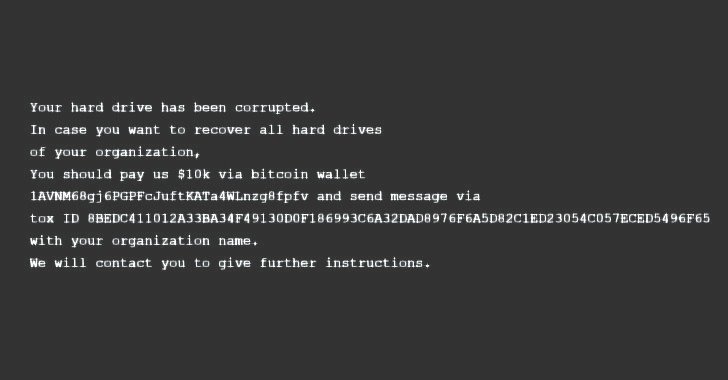
- Overwriting the Grasp Boot Report (MBR), the initially sector of any tough disk that identifies in which the operating technique is positioned in the disk so that it can be loaded into a computer’s RAM, on a victim’s procedure to display screen a bogus ransom notice urging the goal to pay back an amount of $10,000 to a bitcoin wallet
- A second-stage executable that retrieves a file corrupter malware hosted on a Discord channel that is created to search for data files with 189 different extensions, then irrevocably overwrite their contents with a set quantity of 0xCC bytes and rename each individual file with a seemingly random four-byte extension.
The malicious action is “inconsistent” with cybercriminal ransomware activity for reasons that “specific payment quantities and cryptocurrency wallet addresses are hardly ever specified in contemporary prison ransom notes” and “the ransom note in this circumstance does not involve a personalized ID,” Microsoft mentioned.
The progress comes as a lot of authorities web sites in the Eastern European state were defaced on Friday with a information warning Ukrainians that their personalized details was remaining uploaded to the Internet. The Security Support of Ukraine (SSU) reported it identified “symptoms” of involvement of hacking teams affiliated with the Russian intelligence expert services.
“Presented the scale of the noticed intrusions, MSTIC is not equipped to evaluate intent of the discovered damaging actions but does believe that these steps signify an elevated risk to any authorities agency, non-income or enterprise located or with units in Ukraine,” the scientists cautioned.
Nevertheless, Reuters previously today elevated the risk that the attacks may have been the do the job of an espionage group joined to Belarusian intelligence that is tracked as UNC1151 and Ghostwriter. “Many significant intrusions into Ukrainian federal government entities have been carried out by UNC1151,” cybersecurity organization Mandiant disclosed in a report in November 2021, pointing out the group’s operations as all those aligned with Belarusian governing administration passions.
Identified this posting intriguing? Stick to THN on Fb, Twitter and LinkedIn to read through much more distinctive articles we post.
Some parts of this article are sourced from:
thehackernews.com

 New crystal structure for hydrogen compounds for high-temperature superconductivity
New crystal structure for hydrogen compounds for high-temperature superconductivity