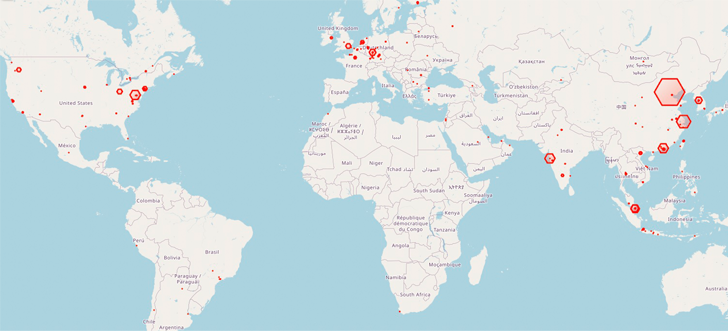
At minimum 1,200 Redis database servers around the globe have been corralled into a botnet making use of an “elusive and extreme risk” dubbed HeadCrab given that early September 2021.
“This superior danger actor utilizes a condition-of-the-artwork, personalized-manufactured malware that is undetectable by agentless and conventional anti-virus methods to compromise a large range of Redis servers,” Aqua security researcher Asaf Eitani explained in a Wednesday report.
A important concentration of infections has been recorded in China, Malaysia, India, Germany, the U.K., and the U.S. to date. The origins of the threat actor are presently mysterious.
The results occur two months just after the cloud security company lose mild on a Go-dependent malware codenamed Redigo that has been discovered compromising Redis servers.
The attack is intended to goal Redis servers that are exposed to the internet, adopted by issuing a SLAVEOF command from an additional Redis server that’s by now under the adversary’s management.
In performing so, the rogue “master” server initiates a synchronization of the freshly hacked server to obtain the destructive payload, which has the complex HeadCrab malware.
“The attacker appears to primarily goal Redis servers and has a deep knowledge and know-how in Redis modules and APIs as shown by the malware,” Eitani noted.
Although the top end target of utilizing the memory-resident malware is to hijack the procedure means for cryptocurrency mining, it also boasts of a lot of other possibilities that lets the risk actor to execute shell commands, load fileless kernel modules, and exfiltrate knowledge to a distant server.
What is more, a stick to-on analysis of the Redigo malware has uncovered it to be weaponizing the identical grasp-slave strategy for proliferation, and not the Lua sandbox escape flaw (CVE-2022-0543) as beforehand disclosed.
Customers are advised to chorus from exposing Redis servers immediately to the internet, disable the “SLAVEOF” feature in their environments if not in use, and configure the servers to only take connections from dependable hosts.
Eitani explained “HeadCrab will persist in employing slicing-edge strategies to penetrate servers, either as a result of exploiting misconfigurations or vulnerabilities.”
Located this posting attention-grabbing? Follow us on Twitter and LinkedIn to go through a lot more exceptional written content we submit.
Some parts of this article are sourced from:
thehackernews.com


 Computers that power self-driving cars could be a huge driver of global carbon emissions
Computers that power self-driving cars could be a huge driver of global carbon emissions