A new exploit has been devised to “unenroll” enterprise- or faculty-managed Chromebooks from administrative management.
Enrolling ChromeOS products helps make it possible to enforce gadget guidelines as established by the corporation by means of the Google Admin console, which includes the capabilities that are readily available to end users.
“Each and every enrolled machine complies with the policies you set right until you wipe or deprovision it,” Google states in its documentation.
That’s in which the exploit – dubbed Shady Hacking 1nstrument Tends to make Equipment Enrollment Retreat aka SH1MMER – comes in, enabling consumers to bypass these admin constraints.
The strategy is also a reference to shim, a Return Products Authorization (RMA) disk image employed by provider center technicians to reinstall the working process and operate diagnosis and repair service applications.
The Google-signed shim picture is a “mixture of existing Chrome OS manufacturing facility bundle components” – particularly a release image, a toolkit, and the firmware, between other people – that can be flashed to a USB travel.
A Chromebook can then be booted in developer method with the push graphic to invoke the restoration selections. A shim graphic can either be common or specific to a Chromebook board.
SH1MMER will take benefit of a modified RMA shim image to generate a restoration media for the Chromebook and writes it to a USB adhere. Performing so demands an on the net builder to down load the patched version of the RMA shim with the exploit.
The following stage involves launching the restoration method on the Chromebook and plugging the USB stick containing the image into the gadget to screen an altered recovery menu that enables users to fully unenroll the device.
“It will now behave completely as if it is a personal computer system and no for a longer time incorporate spy ware or blocker extensions,” the Mercury Workshop crew, which arrived up with the exploit, claimed.
“RMA shims are a manufacturing unit tool allowing sure authorization features to be signed, but only the KERNEL partitions are checked for signatures by the firmware,” the crew more elaborated. “We can edit the other partitions to our will as lengthy as we eliminate the pressured readonly little bit on them.”
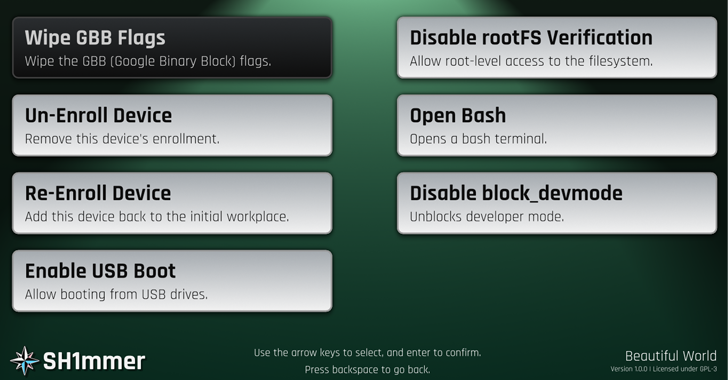
Furthermore, the SH1MMER menu can be utilised to re-enroll the system, enable USB boot, open a bash shell, and even permit root-degree entry to the ChromeOS working procedure.
The Hacker News has reached out to Google for comment, and we will update the tale if we hear back again.
Observed this report interesting? Abide by us on Twitter and LinkedIn to go through extra unique articles we write-up.
Some parts of this article are sourced from:
thehackernews.com

 Prilex PoS Malware Evolves to Block Contactless Payments to Steal from NFC Cards
Prilex PoS Malware Evolves to Block Contactless Payments to Steal from NFC Cards