An emerging Python-centered credential harvester and a hacking device named Legion is becoming marketed by way of Telegram as a way for danger actors to break into many on the web providers for additional exploitation.
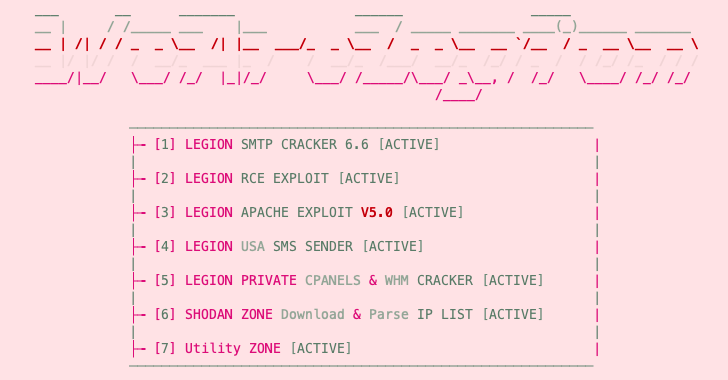
Legion, according to Cado Labs, incorporates modules to enumerate susceptible SMTP servers, carry out distant code execution (RCE) attacks, exploit unpatched variations of Apache, and brute-force cPanel and WebHost Supervisor (WHM) accounts.
The malware is suspected to be linked to a different malware household called AndroxGh0st that was 1st documented by cloud security services providerLacework in December 2022.
Cybersecurity business SentinelOne, in an assessment revealed late very last month, disclosed that AndroxGh0st is portion of a thorough toolset named AlienFox that is presented to menace actors to steal API keys and secrets and techniques from cloud expert services.
“Legion seems to be aspect of an emerging generation of cloud-targeted credential harvester/spam utilities,” security researcher Matt Muir explained to The Hacker News. “Builders of these applications frequently steal each individual other’s code, creating attribution to a specific group challenging.”
Moreover utilizing Telegram as a details exfiltration stage, Legion is developed to exploit web servers functioning material management units (CMS), PHP, or PHP-centered frameworks like Laravel.
“It can retrieve qualifications for a huge assortment of web products and services, these as email companies, cloud services suppliers, server administration methods, databases, and payment platforms like Stripe and PayPal,” Cado Labs claimed.
Some of the other specific solutions contain SendGrid, Twilio, Nexmo, AWS, Mailgun, Plivo, ClickSend, Mandrill, Mailjet, MessageBird, Vonage, Exotel, OneSignal, Clickatell, and TokBox.
The main intention of the malware is to help danger actors to hijack the providers and weaponize the infrastructure for adhere to-on assaults, together with mounting opportunistic phishing strategies.
The most important purpose of the malware is to enable threat actors to hijack the providers and weaponize the infrastructure for adhere to-on assaults, which include mounting mass spam and opportunistic phishing campaigns.
The cybersecurity business mentioned it also identified a YouTube channel made up of tutorial videos on how to use Legion, suggesting that the “software is widely distributed and is most likely compensated malware.” The YouTube channel, which was made on June 15, 2021, stays energetic as of composing.
Moreover, Legion retrieves AWS qualifications from insecure or misconfigured web servers and provide SMS spam messages to end users of U.S. mobile networks these kinds of as AT&T, Dash, T-Cellular, Verizon, and Virgin.
Future WEBINARMaster the Artwork of Dark Web Intelligence Collecting
Study the art of extracting threat intelligence from the dark web – Be a part of this qualified-led webinar!
Save My Seat!
“To do this, the malware retrieves the area code for a U.S. state of the user’s selecting from the site www.randomphonenumbers.com,” security researcher Matt Muir stated. “A rudimentary selection generator functionality is then used to create up a checklist of phone quantities to goal.”
In addition, Legion can retrieve AWS qualifications from insecure or misconfigured web servers and produce SMS spam messages to users of U.S. mobile networks this kind of as AT&T, Dash, T-Cell, Verizon, and Virgin by leveraging the stolen SMTP credentials.
“To do this, the malware retrieves the region code for a U.S. state of the user’s selecting from the website www.randomphonenumbers[.]com,” Muir said. “A rudimentary number generator operate is then utilized to establish up a record of phone numbers to focus on.”
Yet another noteworthy aspect of Legion is its means to exploit well-recognised PHP vulnerabilities to register a web shell for persistent distant entry or execute malicious code.
The origins of the threat actor driving the device, who goes by the alias “forzatools” on Telegram, continue being unfamiliar, while the presence of Indonesian-language feedback in the resource code implies that the developer may well be Indonesian or primarily based in the nation.
“Given that this malware depends seriously on misconfigurations in web server systems and frameworks these kinds of as Laravel, it is really encouraged that users of these systems assessment their current security processes and assure that insider secrets are appropriately saved,” Muir claimed.
Found this posting exciting? Abide by us on Twitter and LinkedIn to examine more special articles we write-up.
Some parts of this article are sourced from:
thehackernews.com

 Superyacht-Maker Hit by Easter Ransomware Attack
Superyacht-Maker Hit by Easter Ransomware Attack