Cybersecurity researchers have spotted a unusual type of probably harmful malware that targets a machine’s booting course of action to drop persistent malware.
The marketing campaign involved the use of a compromised UEFI (or Unified Extensible Firmware Interface) that contains a destructive implant, building it the next recognized general public circumstance the place a UEFI rootkit has been employed in the wild.
According to Kaspersky, the rogue UEFI firmware images were modified to include a number of malicious modules, which ended up then used to fall malware on sufferer equipment in a sequence of focused cyberattacks directed in opposition to diplomats and members of an NGO from Africa, Asia, and Europe.
Calling the malware framework “MosaicRegressor,” Kaspersky researchers Mark Lechtik, Igor Kuznetsov, and Yury Parshin explained a telemetry investigation exposed various dozen victims concerning 2017 and 2019, all of whom experienced some ties to North Korea.
UEFI is a firmware interface and a replacement for BIOS that increases security, making certain that no malware has tampered with the boot system. Mainly because UEFI facilitates the loading of the running technique itself, these kinds of infections are resistant to OS reinstallation or replacement of the tough push.
“UEFI firmware makes for a excellent system of persistent malware storage,” Kaspersky said. “A advanced attacker can modify the firmware in order to have it deploy malicious code that will be run after the operating process is loaded.”
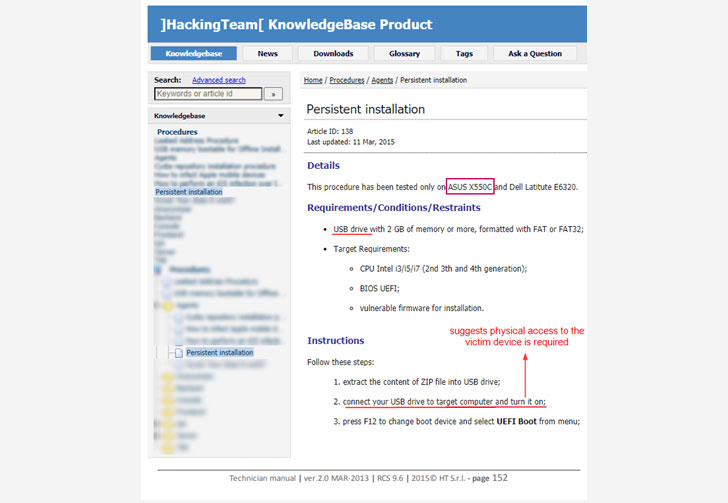
Which is accurately what this risk actor appears to have carried out. Even though the precise infection vector utilized to overwrite the unique firmware remains mysterious at this stage, a leaked handbook indicates the malware could have been deployed by way of bodily obtain to the victim’s equipment.
The new UEFI malware is a personalized variation of the Hacking Team’s VectorEDK bootkit, which was leaked in 2015 and has considering that been obtainable on the internet. It is utilised to plant a 2nd payload, known as the MosaicRegressor — “a multi-stage and modular framework aimed at espionage and knowledge gathering” that is composed of supplemental downloaders to fetch and execute secondary factors.
The downloaders, in flip, make contact with the command-and-command (C2) server to get up coming-stage DLLs in get to execute distinct commands, the results of which are exported back to the C2 server or forwarded to a “feedback” mail tackle from the place the attackers can gather the amassed knowledge.
The payloads are transferred in a selection of strategies, which include by using e-mail messages from mailboxes (“mail.ru”) challenging-coded in the malware’s binary.
In some scenarios, even so, the malware was shipped to some of the victims via spear-phishing e-mails with embedded decoy paperwork (“0612.doc”) prepared in Russian that purported to focus on gatherings related to North Korea.
With regards to the identity of the threat actor behind MosaicRegressor, Kaspersky claimed it uncovered various code-level hints that suggest they have been created in Chinese or Korean and mentioned the use of Royal Highway (8.t) RTF weaponizer, which has been tied to many Chinese threat teams in the earlier.
And finally, Kaspersky located a C2 deal with in a single of MosaicRegressor’s variants that have been observed in link with Chinese hacker teams broadly recognised as Winnti (aka APT41).
“The attacks […] exhibit the length an actor can go in purchase to attain the optimum level of persistence on a victim equipment,” Kaspersky concluded.
“It is remarkably uncommon to see compromised UEFI firmware in the wild, commonly due to the lower visibility into assaults on firmware, the innovative actions expected to deploy it on a target’s SPI flash chip, and the superior stakes of burning sensitive toolset or belongings when performing so.”
Discovered this short article appealing? Adhere to THN on Facebook, Twitter and LinkedIn to browse additional special content material we publish.
Some parts of this write-up are sourced from:
thehackernews.com

 PCI DSS Compliance Slumps 28% Since 2016
PCI DSS Compliance Slumps 28% Since 2016