Two new phishing methods use the platform’s automatic responses to evade email filters.
Two fresh company email compromise (BEC) strategies have emerged onto the phishing scene, involving the manipulation of Microsoft 365 automatic email responses in get to evade email security filters.
In 1 situation, scammers are concentrating on victims by redirecting respectable out-of-office (OOO) replies from an employee to them and in the other, browse receipts are getting manipulated. Equally variations were being noticed staying utilized in the wild in the U.S. in December, when automobile-responders were additional widespread owing to vacation family vacation.
“These strategies indicate attackers are working with each available device and loophole to their edge in the hopes of a prosperous BEC endeavor,” claimed Roman Tobe, researcher with Abnormal Security, in a putting up this 7 days.
Return to Sender: Read through Receipts
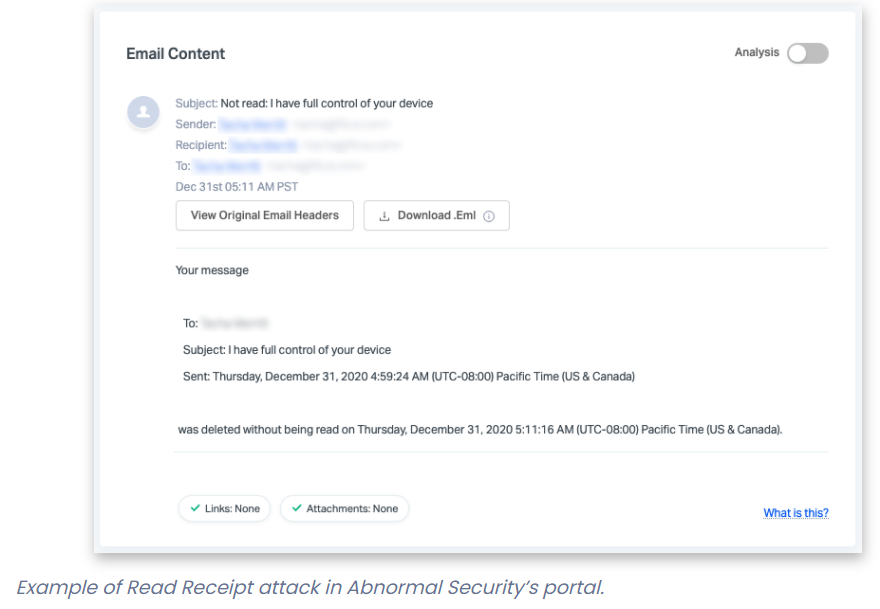
In the read through-receipts attack, a scammer creates an extortion email, and manipulates the “Disposition-Notification-To” email header to make a study-receipt notification from Microsoft 365 to the receiver.
The destructive email alone may be trapped by email security alternatives, but the read receipt is despatched to the target anyway. It incorporates the text of the unique email, and will be ready to bypass regular security answers and land in the employee’s inbox, considering the fact that it’s generated from the inside procedure.
An example:
“Fear-primarily based attacks this sort of as these are intended to elicit an urgent response from recipients to click on a malicious connection, and the attackers double down on this tactic by manipulating the email headers with panic-based mostly language,” Austin Merritt, cyber-menace intelligence analyst at Electronic Shadows, advised Threatpost. “If a user clicks on a website link, the compromise of their product could allow an attacker to escalate privileges throughout an organization’s network.”
Out-of-Business Attack
In the OOO attack, a cybercriminal makes a BEC email that impersonates anyone inside of the corporation. The attacker can manipulate the “Reply-To” email header so that if the goal has an OOO message turned on, that OOO notification (which incorporates the primary textual content) will be directed to another unique within the corporation.
“So, the email may be sent to a single staff (let’s call them John), but the “Reply-to” header contains a further employee’s email handle (let’s simply call them Tina),” spelled out Graham Cluley, researcher at BitDefender, in an investigation of the findings. “John has his out-of-business reply enabled, so when he gets the fraudulent email an automatic reply is created. Having said that, the out-of-office environment reply is not despatched back to the genuine sender, but to Tina in its place – and incorporates the extortion text.”
As with the go through-receipt gambit, the information possible won’t be caught by email-security units, due to the fact it originates from the first target’s account relatively than anyone external.
“This campaign demonstrates BEC actors’ capacity to bypass security answers and give email recipients the phony perception that their account has been compromised,” mentioned Merritt. “This is problematic for network defenders that currently have traditional security remedies applied due to the fact the phishing e-mail both result in read through receipt notifications or redirect to a different recipient’s inbox, grabbing the consideration of the intended target.”
BEC: A Still-Significant Email Menace
BEC emails are developed to fraud firms out of income. This is ordinarily carried out by impersonating an staff, supplier or purchaser in an email or mobile concept. The tactic usually entails asking for a bogus bill to be compensated or for a recurring payment or wire transfer to be despatched to a new, attacker-managed place.
The volume of BEC attacks has continued to mature, soaring by 15 p.c quarter-above-quarter in Q3 of 2020, in accordance to Irregular Security’s Quarterly BEC Report [PDF]. The normal weekly quantity of BEC assaults in the time period of time increased in six out of eight industries, with the largest increase noticed in the power/infrastructure sector, at 93 %. The industries which experienced the best variety of weekly BEC assaults were being retail/client items and manufacturing and technology.
Those campaigns geared in direction of invoice and payment fraud ended up specifically virulent, with a 155 per cent QoQ, the review identified.
The standard defense for these forms of assaults – consumer awareness and education to independently verify that a request is legit – gets to be more hard with a dispersed footprint, scientists noted.
“Remote do the job has created far more possibility to execute BEC and other phishing attacks,” Hank Schless, senior manager of security answers at Lookout, told Threatpost. “Without becoming able to walk over to another person’s desk in the place of work, staff will have a a lot tougher time validating not known texts or emails. Threat actors have taken take note of these issues and are applying distant function to their gain to execute even larger BEC assaults.”
Also, as email-security programs get smarter, so are the cybercriminals. For instance, previously in January a marketing campaign was spotted that leverages Google’s Types survey instrument to prompt an ongoing dialogue between the email receiver and the attacker – environment them up as a target for a long run BEC entice, researchers said.
And Microsoft’s Place of work 365 in particular, which is the computing giant’s cloud-based mostly Workplace suite, is an especially desirable avenue for BEC attempts, analysts have observed.
Microsoft and Office 365: A Ripe Concentrate on
“While Place of work 365 gives the dispersed workforce with a key area to carry out business, it also makes a central repository of knowledge and data which is a primary target for attackers to exploit,” Chris Morales, head of security analytics at Vectra, informed Threatpost. “Rather than leveraging malware, attackers are working with the existing resources and capabilities now present in Office environment 365, dwelling off the land to remain hidden for months.”
Immediately after attackers attain a foothold in an Office 365 atmosphere, it’s simple for BEC scammers to leverage a dependable communication channel (i.e. sending an illegitimate email from the CEO’s official account, utilised to socially engineer staff, clients or companions). But there are numerous typical undesirable outcomes, outside of mounting BEC attacks, he added.
These include things like the capacity to lookup through email messages, chat histories and files searching for passwords or other attention-grabbing data placing up forwarding regulations to obtain accessibility to a continuous stream of email with out needing to indicator in all over again planting malware or malicious backlinks in files that quite a few people have faith in and use, once again manipulating belief to circumvent avoidance controls that may possibly induce warnings and stealing or holding information and details for ransom.
“The relevance of holding a watchful eye on the misuse of consumer access are not able to be overstated supplied its prevalence in serious-planet assaults,” Morales explained. “In the existing cybersecurity landscape, security measures like multi-factor authentication (MFA) are no for a longer time plenty of to deter attackers. SaaS platforms like Business office 365 are a secure haven for attacker lateral movement, building it paramount to focus on consumer obtain to accounts and providers. When security groups have solid information and anticipations about SaaS platforms such as Workplace 365, destructive behaviors and privilege abuse are significantly less complicated to rapidly determine and mitigate.”
Download our special Free Threatpost Insider E book Health care Security Woes Balloon in a Covid-Period Environment, sponsored by ZeroNorth, to study extra about what these security dangers imply for hospitals at the day-to-working day stage and how healthcare security groups can implement most effective tactics to secure suppliers and people. Get the entire story and Download the Ebook now – on us!
Some parts of this article are sourced from:
threatpost.com


 The youngest AI programmer in the world is a 7-year-old Guinness record holder
The youngest AI programmer in the world is a 7-year-old Guinness record holder