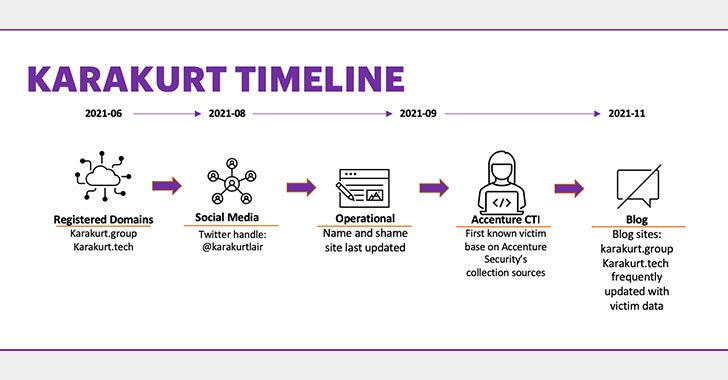
A previously undocumented, financially inspired risk team has been linked to a string of facts theft and extortion assaults on in excess of 40 entities involving September and November 2021.
The hacker collective, which goes by the self-proclaimed identify Karakurt and was initial recognized in June 2021, is able of modifying its tactics and procedures to adapt to the qualified environment, Accenture’s Cyber Investigations, Forensics and Response (CIFR) staff reported in a report revealed on December 10.
“The threat team is financially motivated, opportunistic in mother nature, and so much, seems to target smaller sized companies or company subsidiaries compared to the option significant game searching method,” the CIFR team said. “Primarily based on intrusion examination to day, the danger group focuses only on data exfiltration and subsequent extortion, somewhat than the much more damaging ransomware deployment.”
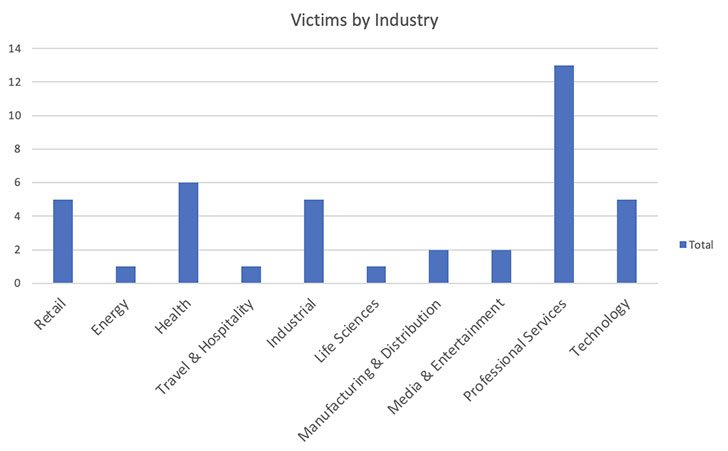
95% of the acknowledged victims are dependent in North The usa, when the remaining 5% are in Europe. Qualified products and services, healthcare, industrial, retail, technology, and entertainment verticals have been the most qualified.
The objective, the researchers observed, is to prevent drawing notice to its malicious activities as a great deal as probable by relying on residing off the land (LotL) strategies, whereby the attackers abuse reputable software and features available in a method these types of as working process elements or set up application to shift laterally and exfiltrate information, as opposed to deploying submit-exploitation equipment like Cobalt Strike.
With ransomware assaults gaining around the globe attention in the wake of incidents aimed at Colonial Pipeline, JBS, and Kaseya as nicely as the subsequent law enforcement actions that have triggered actors like DarkSide, BlackMatter, and REvil to shutter their operations, Karakurt seems to be striving a unique tack.

Fairly than deploy ransomware soon after attaining preliminary obtain to victims’ internet-struggling with methods through legit VPN credentials, the actors focuses nearly completely on info exfiltration and extortion, a transfer that’s significantly less very likely to bring the targets’ organization activities to a standstill and however empower Karakurt to need a “ransom” in return for the stolen information.
Other than encryption knowledge at relaxation anywhere applicable, businesses are advised to turn on a number of-variable authentication (MFA) to authenticate accounts, disable RDP on exterior-experiencing devices, and update the infrastructure to the hottest versions to reduce adversaries from exploiting unpatched devices with publicly-regarded vulnerabilities.
Located this short article interesting? Comply with THN on Fb, Twitter and LinkedIn to examine more special information we post.
Some parts of this article are sourced from:
thehackernews.com

 Top 3 SaaS Security Threats for 2022
Top 3 SaaS Security Threats for 2022