The Iranian danger actor known as MuddyWater is continuing its time-analyzed custom of relying on authentic distant administration tools to commandeer qualified systems.
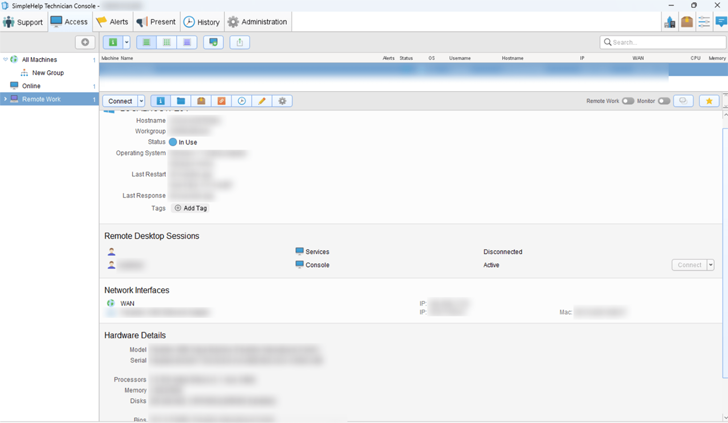
Although the nation-condition team has beforehand utilized ScreenConnect, RemoteUtilities, and Syncro, a new assessment from Group-IB has exposed the adversary’s use of the SimpleHelp remote assist application in June 2022.
MuddyWater, energetic given that at minimum 2017, is assessed to be a subordinate factor within just Iran’s Ministry of Intelligence and Security (MOIS). Some of the prime targets consist of Turkey, Pakistan, the U.A.E., Iraq, Israel, Saudi Arabia, Jordan, the U.S., Azerbaijan, and Afghanistan.
“MuddyWater uses SimpleHelp, a legitimate distant device handle and administration software, to assure persistence on victim units,” Nikita Rostovtsev, senior menace analyst at Team-IB, mentioned.
“SimpleHelp is not compromised and is made use of as intended. The threat actors observed a way to obtain the tool from the formal internet site and use it in their assaults.”
The actual distribution process used to fall the SimpleHelp samples is now unclear, though the group is recognised to deliver spear-phishing messages bearing malicious backlinks from by now compromised corporate mailboxes.
Group-IB’s findings had been corroborated by Slovak cybersecurity company ESET earlier this January, detailing MuddyWater’s attacks in Egypt and Saudi Arabia that entailed the use of SimpleHelp to deploy its Ligolo reverse tunneling device and a credential harvester dubbed MKL64.
Future WEBINARMaster the Art of Dark Web Intelligence Gathering
Find out the artwork of extracting threat intelligence from the dark web – Sign up for this specialist-led webinar!
Preserve My Seat!
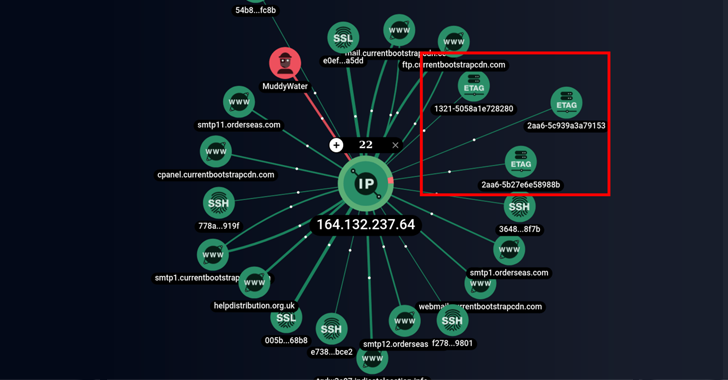
The Singapore-headquartered enterprise additional reported it was ready to identify hitherto not known infrastructure operated by the group as effectively as a PowerShell script that is able of obtaining instructions from a distant server, the results of which are despatched back to the server.
The disclosure will come weeks soon after Microsoft thorough the group’s modus operandi of carrying out damaging assaults on hybrid environments less than the guise of a ransomware procedure.
Uncovered this report appealing? Abide by us on Twitter and LinkedIn to go through additional exclusive content material we article.
Some parts of this article are sourced from:
thehackernews.com

 Phishing Attacks Surge as Threat Actors Leverage New AI Tools
Phishing Attacks Surge as Threat Actors Leverage New AI Tools