As a CISO, one of the most demanding questions to solution is “How nicely are we guarded right now?” In between the acceleration of hackers’ offensive abilities and the dynamic mother nature of facts networks, a drift in the security posture is unavoidable and desires to be continually compensated. Hence, answering that question implies constantly validating the security posture and staying in a place to check it together with, against the hottest rising threats.
However, the bulk of cybersecurity is concentrated on defensive applications. The mixture of the fast evolution of technology and the multiplication of technology layers, mixed with the professionalization of the menace landscape, has led to a profusion of cybersecurity applications tackling distinctive security facets.
Checking the cybersecurity resolution stack efficiency is commonly carried out by pen-testing or, much more not too long ago, by purple teaming – an training aimed to map probable loopholes that would direct to a data breach. When carried out as soon as or twice a calendar year only, these tests may fulfill the compliance regulators. Still, as new threats emerge day-to-day, they are unsuccessful to advise about the environment’s latest security posture successfully.
In addition, these infrequent exams fall short to inform about opportunity device overlaps and are not built to stop instrument sprawl, a recurrent prevalence in a area in which more than 50 % of SOC centers are overrun with redundant security resources and are swamped by also quite a few alerts.
Unrationalized security stacks are not only unnecessarily high priced, but they also deliver additional false-beneficial phone calls, needlessly taxing security employees endurance and increasing the risk of missing a critical inform.
The capacity to measure every tool’s efficacy, remove overlap and manage continuous handle more than security baseline variability depends on continuous accessibility to quantified details. This is at the core of what Prolonged Security Posture Administration (XPSM) delivers to the table.
Knowing Prolonged Security Posture Administration
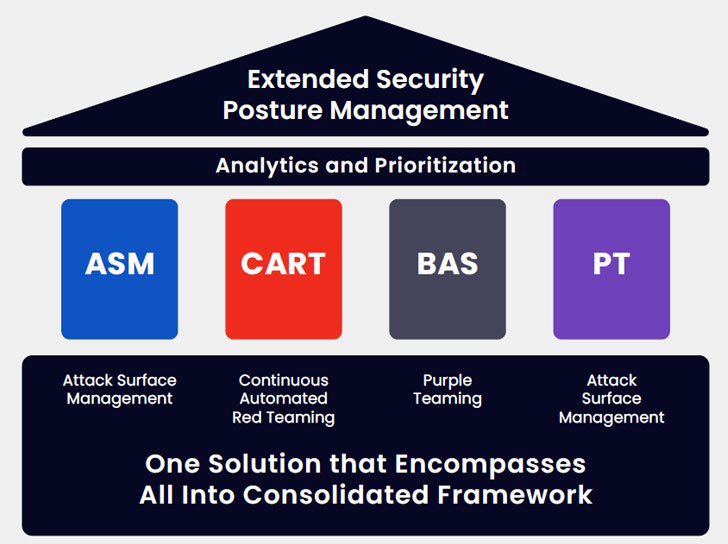
Extended Security Posture Administration (XSPM) is a multilayered system combining the abilities of Attack Surface Administration (ASM), Breach and Attack Simulation (BAS), Continual Automated Red Teaming (CART), and Purple Teaming to repeatedly assess and score the infrastructure’s over-all cyber resiliency.
This up-to-date thorough snapshot of the energetic security posture, combined with in-depth remediation course of action suggestions, is conducive to generating rational enterprise conclusions based mostly on really hard facts.
Employing the granular analysis of every particular person device and of the security control configuration, an XSPM solution gives granular info about each and every answer utilised, the eventual overlap between two or more options and the remaining security gaps. It then presents in-depth tips about the remediation procedure for each individual gap and optimization possibilities for determined overlaps.
The Edge of a Consolidated, Intensive Baseline
Security groups are systematically impressed by the big difference in acquiring actionable details created, the two in improving upon the security posture and in rationalizing cybersecurity paying out.
XSPM allows the security workforce to deal with the frequent content configuration churn and leverages telemetry to aid discover the gaps in security by making up-to-date rising threats feeds and giving more take a look at conditions emulating TTPs that attackers would use, preserving DevSocOps the time necessary to establish those people check conditions. When operating XSPM validation modules, being aware of that the exams are well timed, latest, and applicable enables reflecting on the efficacy of security controls and understanding wherever to make investments to ensure that the configuration, cleanliness and posture are preserved through the consistent variations in the setting.
By supplying visibility and maximizing relevancy, XSPM can help verify that every single greenback invested benefits risk reduction and software efficacy by way of baselining and trending and mechanically making studies containing thorough tips covering security hardening and software stack optimization it radically facilitates conversations with the board.
The change from rare to common tests, produced feasible by automation, enables both the steady baseline variability checking and the quantified calculation of ROI accomplished via resource stack rationalization.
In addition, it enables developing attack-centered vulnerability administration by leveraging the benefits to prioritize patching.
As a bonus, checking an environment’s capability to stand up to the most current assaults can be accomplished virtually at a click on, and, if wanted, advised mitigation processes can be pushed ahead in the prioritized patching routine.
George Washington’s adage “The ideal defense is a fantastic offense” definitely applies to cybersecurity, and the steady offense is the only way to keep forward of the attackers’ development constantly.
Note: This article was written by Arien Seghetti, Alternative Architect at Cymulate. For far more information and facts, visit www.cymulate.com and sign up for a Cost-free Trial.
Observed this posting attention-grabbing? Adhere to THN on Fb, Twitter and LinkedIn to examine far more exclusive content material we submit.
Some parts of this article are sourced from:
thehackernews.com

