A threat actor with affiliations to the cyber warfare division of Hamas has been connected to an “elaborate marketing campaign” targeting higher-profile Israeli people employed in sensitive protection, law enforcement, and crisis services companies.
“The campaign operators use sophisticated social engineering approaches, eventually aimed to produce formerly undocumented backdoors for Windows and Android units,” cybersecurity business Cybereason explained in a Wednesday report.
“The aim driving the attack was to extract delicate information from the victims’ equipment for espionage purposes.”
The monthslong intrusions, codenamed “Operation Bearded Barbie,” have been attributed to an Arabic-speaking and politically-enthusiastic team named Arid Viper, which operates out of the Center East and is also regarded by the monikers APT-C-23 and Desert Falcon.
Most lately, the menace actor was held responsible for assaults aimed at Palestinian activists and entities beginning all over October 2021 working with politically-themed phishing emails and decoy paperwork.
The hottest infiltrations are noteworthy for their unique target on plundering information and facts from computers and cell devices belonging to Israeli people by luring them into downloading trojanized messaging apps, granting the actors unfettered entry.
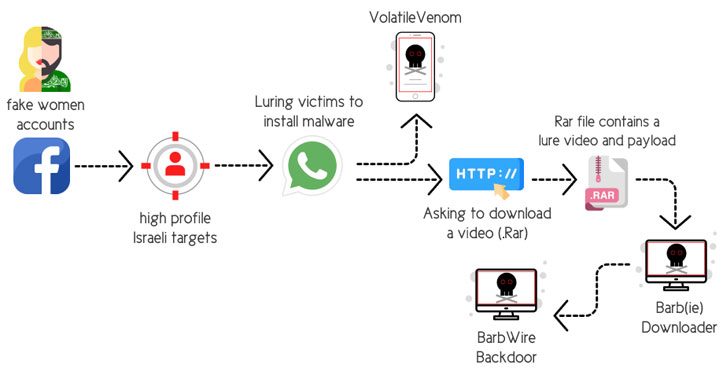
The social engineering attacks involved the use of fake personas on Facebook, relying on the tactic of catfishing to set up fictitious profiles of desirable young girls to get the trust of the qualified men and women and befriend them on the system.
“Soon after gaining the victim’s believe in, the operator of the bogus account implies migrating the discussion from Facebook around to WhatsApp,” the scientists elaborated. “By carrying out so, the operator promptly obtains the target’s mobile quantity.”
After the chat shifts from Facebook to WhatsApp, the attackers propose the victims that they set up a protected messaging application for Android (dubbed “VolatileVenom”) as very well as open a RAR archive file containing express sexual information that potential customers to the deployment of a malware downloader referred to as Barb(ie).
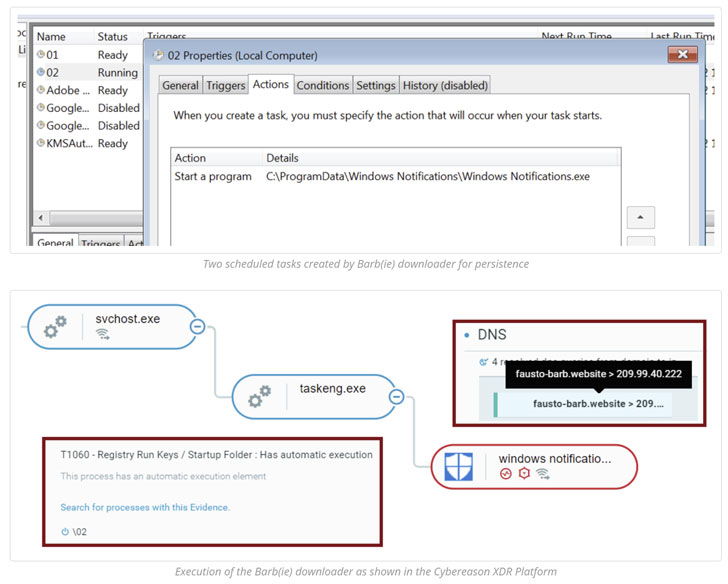
Other hallmarks of the campaign have included the group leveraging an upgraded arsenal of malware instruments, which includes the BarbWire Backdoor, which is installed by the downloader module.
The malware serves as a device to absolutely compromise the sufferer equipment, enabling it to establish persistence, harvest saved information, report audio, capture screenshots, and obtain added payloads, all of which is transmitted back to a distant server.

VolatileVenom, on the other hand, is Android spy ware that is acknowledged to spoof genuine messaging apps and masquerade as process updates and which has been put to use in different strategies by Arid Viper since at the very least 2017.
A single this sort of case in point of a rogue Android app is known as “Wink Chat,” where by victims trying to indication up to use the application are presented an error message that “it will be uninstalled,” only for it to stealthily operate in the background and extract a large range of data from the cell devices.
“The attackers use a fully new infrastructure that is distinctive from the recognised infrastructure used to concentrate on Palestinians and other Arabic-speakers,” the researchers mentioned.
“This marketing campaign displays a substantial move-up in APT-C-23 capabilities, with upgraded stealth, a lot more advanced malware, and perfection of their social engineering tactics which require offensive HUMINT capabilities making use of a incredibly lively and effectively-groomed network of bogus Facebook accounts that have been established fairly effective for the team.”
Identified this short article intriguing? Stick to THN on Fb, Twitter and LinkedIn to go through much more unique information we post.
Some parts of this article are sourced from:
thehackernews.com