A financially motivated menace actor has been noticed deploying a formerly unidentified rootkit concentrating on Oracle Solaris devices with the goal of compromising Automatic Teller Machine (ATM) switching networks and carrying out unauthorized funds withdrawals at unique banks working with fraudulent cards.
Danger intelligence and incident reaction firm Mandiant is monitoring the cluster less than the moniker UNC2891, with some of the group’s strategies, procedures, and procedures sharing overlaps with that of an additional cluster dubbed UNC1945.
The intrusions staged by the actor require “a high diploma of OPSEC and leverage both equally community and non-public malware, utilities, and scripts to get rid of evidence and hinder response efforts,” Mandiant researchers stated in a new report posted this 7 days.

Even a lot more concerningly, the assaults spanned numerous a long time in some scenarios, during the entirety of which the actor remained undetected by leveraging a rootkit known as CAKETAP, which is built to conceal network connections, processes, and files.
Mandiant, which was in a position to get well memory forensic details from just one of the victimized ATM switch servers, mentioned that 1 variant of the kernel rootkit came with specialised functions that enabled it to intercept card and PIN verification messages and use the stolen facts to complete fraudulent hard cash withdrawals from ATM terminals.
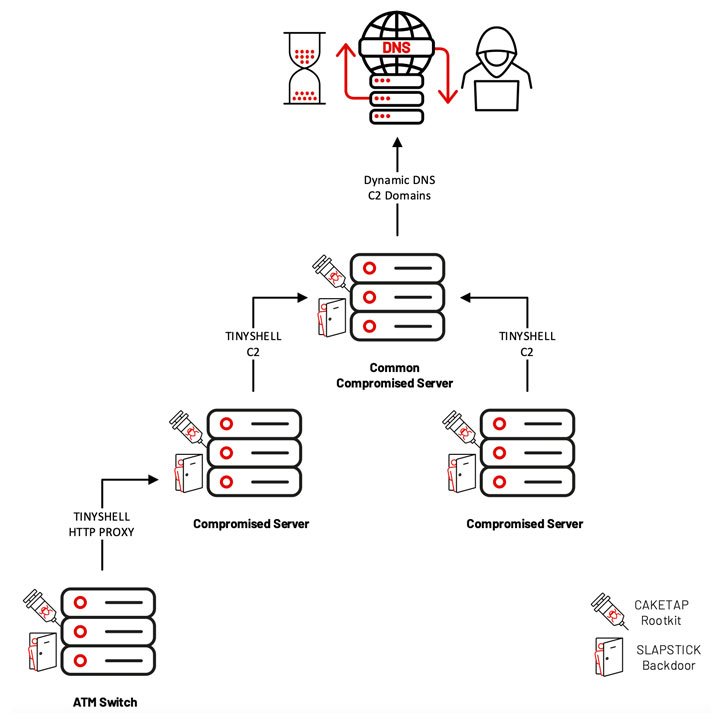
Also place to use are two backdoors identified as SLAPSTICK and TINYSHELL, both equally attributed to UNC1945 and are used to get persistent distant obtain to mission-critical units as very well as shell execution and file transfers by means of rlogin, telnet, or SSH.
“In line with the group’s familiarity with Unix and Linux dependent units, UNC2891 typically named and configured their TINYSHELL backdoors with values that masqueraded as legit services that could be disregarded by investigators, this kind of as systemd (SYSTEMD), title assistance cache daemon (NCSD), and the Linux at daemon (ATD),” the scientists pointed out.

Additionally, the attack chains have utilized a assortment of malware and publicly-accessible utilities, which include –
- STEELHOUND – A variant of the STEELCORGI in-memory dropper which is applied to decrypt an embedded payload and encrypt new binaries
- WINGHOOK – A keylogger for Linux and Unix centered functioning methods that captures the data in an encoded format
- WINGCRACK – A utility that is applied to parse the encoded written content created by WINGHOOK
- WIPERIGHT – An ELF utility that erases log entries pertaining to a particular person on Linux and Unix centered programs
- MIGLOGCLEANER – An ELF utility that wipes logs or take away certain strings from logs on Linux and Unix based mostly devices
“[UNC2891] makes use of their ability and experience to take complete gain of the lowered visibility and security measures that are generally existing in Unix and Linux environments,” the scientists reported. “Although some of the overlaps amongst UNC2891 and UNC1945 are notable, it is not conclusive ample to attribute the intrusions to a single menace group.”
Found this posting interesting? Stick to THN on Fb, Twitter and LinkedIn to browse a lot more exclusive material we put up.
Some parts of this article are sourced from:
thehackernews.com


 Facebook's Ray-Ban Stories can now record up to 60 seconds of video
Facebook's Ray-Ban Stories can now record up to 60 seconds of video