An unknown menace actor has been exploiting a now-patched zero-working day flaw in Internet Explorer browser to supply a thoroughly-highlighted VBA-based mostly remote access trojan (RAT) able of accessing files stored in compromised Windows devices, and downloading and executing destructive payloads as part of an “uncommon” campaign.
The backdoor is dispersed via a decoy document named “Manifest.docx” that hundreds the exploit code for the vulnerability from an embedded template, which, in change, executes shellcode to deploy the RAT, according to cybersecurity organization Malwarebytes, which spotted the suspicious Term file on July 21, 2021.
The malware-laced document statements to be a “Manifesto of the inhabitants of Crimea” calling on the citizens to oppose Russian President Vladimir Putin and “make a unified platform called ‘People’s Resistance.'”

The Internet Explorer flaw, tracked as CVE-2021-26411, is notable for the fact that it was abused by the North Korea-backed Lazarus Group to concentrate on security researchers performing on vulnerability investigation and enhancement.
Before this February, South Korean cybersecurity agency ENKI revealed the condition-aligned hacking collective experienced designed an unsuccessful endeavor at targeting its security scientists with malicious MHTML documents that, when opened, downloaded two payloads from a remote server, one of which contained a zero-day against Internet Explorer. Microsoft addressed the issue as portion of its Patch Tuesday updates for March.
The Internet Explorer exploit is a single of the two strategies which is applied to deploy the RAT, with the other approach relying on a social engineering ingredient that involves downloading and executing a distant macro-weaponized template that contains the implant. Irrespective of the infection chain, the use of double attack vectors is most likely an endeavor to boost the likelihood of obtaining a route into the targeted devices.
“Although the two techniques depend on template injection to fall a entire-featured remote access trojan, the IE exploit (CVE-2021-26411) formerly employed by the Lazarus APT is an unconventional discovery,” Malwarebytes researcher Hossein Jazi stated in a report shared with The Hacker News. “The attackers might have wanted to incorporate social engineering and exploit to improve their possibilities of infecting targets.”

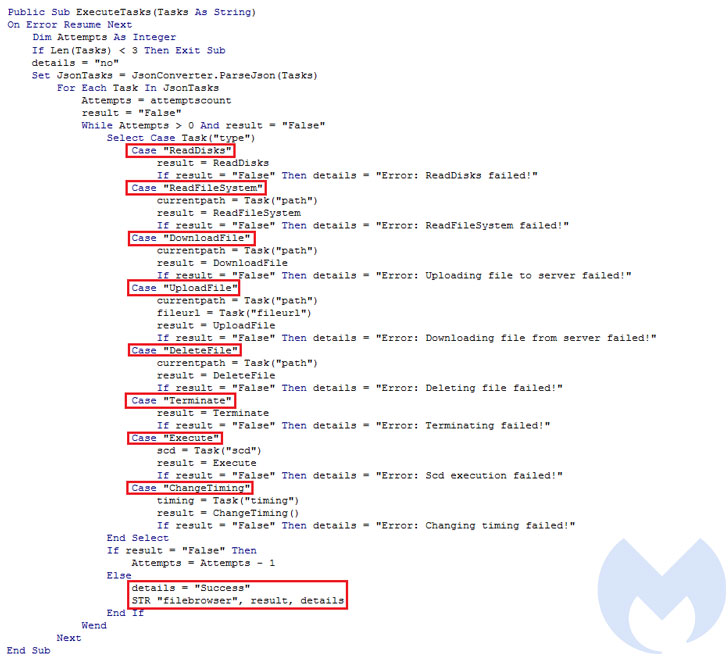
Apart from collecting system metadata, the VBA RAT is orchestrated to establish antivirus products and solutions managing on the contaminated host and execute commands it receives from an attacker-controlled server, which includes reading, deleting, and downloading arbitrary information, and exfiltrate the results of all those commands back again to the server.
Also discovered by Malwarebytes is a PHP-based panel nicknamed “Ekipa” which is used by the adversary to observe victims and see information and facts about the modus operandi that led to the effective breach, highlighting successful exploitation working with the IE zero-working day and the execution of the RAT.
“As the conflict concerning Russia and Ukraine around Crimea carries on, cyber assaults have been rising as very well,” Jazi stated. “The decoy doc includes a manifesto that demonstrates a achievable motive (Crimea) and focus on (Russian and pro-Russian people) driving this attack. On the other hand, it could also have been utilised as a untrue flag.”
Found this write-up fascinating? Observe THN on Facebook, Twitter and LinkedIn to read far more special articles we post.
Some parts of this article are sourced from:
thehackernews.com


 Old Amazon Kindle devices will soon lose 3G access
Old Amazon Kindle devices will soon lose 3G access