In 2022, Russia-backed cyber-attacks targeting Ukraine rose 250% in comparison to 2020 and those concentrating on NATO nations around the world, 300%.
This staggering surge is a person of the conclusions from Google Threat Analysis Group (TAG) in a February 16 report, Fog of War: How the Ukraine Conflict Transformed the Cyber Menace Landscape, revealed in collaboration with Google Have faith in & Basic safety and danger intelligence agency Mandiant, now aspect of Google Cloud.
In the report, Google uncovered that Russia’s intense, multi-faceted method to “gain a decisive wartime gain in cyberspace” could really day again to 2019.
Five Phases of Cyber Functions
In the course of the first section highlighted by Google, which spanned in between 2019 and early 2022, Russia ran cyber espionage strategies from Ukraine and NATO member-states, as perfectly as what the American tech large calls “pre-positioning” operations.
From April 2021, one month just after Russian troops started out to mass on the Ukraine border, the Russian Advanced Persistent Menace (APT) group UNC2589 (aka Frozenvista), “a new, possible GRU actor,” started out deploying phishing assaults versus Ukrainian businesses, the report statements. The GRU is the frequent acronym offered to the Russian Armed Forces’ Primary Directorate of the Common Workers, a armed forces intelligence agency.
Quite a few other Russian-sponsored followed fit in the course of 2021, which include Extravagant Bear (APT28, aka Frozenlake).
In mid-January 2022, a wave of disruptive and damaging cyber-assaults started off, with wiper assaults this kind of as WhisperGate (aka PayWipe) and its affiliate, WhisperKill (aka ShadyLook).
These were a taste of what was to arrive in the 2nd phase when Russian troops began their kinetic invasion of Ukraine. The land-progress in February was accompanied by lots of more disruptive and harmful wiper assaults. This section lasted right until April, with the emergence of numerous new malware family members, like the PartyTicket ransomware, the wiper CaddyWiper and Industroyer 2, an up-to-date version of Industroyer, a harmful malware targeting industrial command systems (ICS), which is deemed to have been utilised in the cyber-attack on Ukraine’s energy grid in December 2016.
In Might, Russian-backed danger actors entered a 3rd stage in which they commenced to reuse the exact malware, primarily CaddyWiper, to attack entities in Ukraine and NATO nations.
In accordance to the report, this period lasted right until July, followed by a lull in activity during August and September. Cyber-attacks resumed in Oct, in a fifth period that noticed Russian menace actors use CaddyWiper together with other new malware.
Supply: Google
“From its incident reaction operate, Mandiant noticed far more harmful cyberattacks in Ukraine throughout the initially four months of 2022 than in the earlier 8 several years, with attacks peaking about the commence of the invasion. […] Many functions indicated an attempt by the GRU to harmony competing priorities of entry, selection, and disruption during every stage of exercise,” the report reads.
A Multi-Faceted Strategy
In summary, Russia’s multi-pronged offensive tactic in cyberspace integrated the adhering to:
- A extraordinary enhance in the use of harmful attacks on the Ukrainian govt, armed service and civilian infrastructure
- A spike in spear-phishing exercise targeting NATO nations around the world
- An uptick in cyber functions designed to additional multiple Russian aims, these kinds of as hack-and-leak attacks concentrating on sensitive information
The report confirmed that some actors targeted on unique varieties of assaults, these kinds of as Frozenlake/Fancy Bear, Frozenvista and Belarusian actor Puschcha (UNC1151) with phishing campaigns towards Ukraine and NATO nations around the world, and Coldriver (aka Gossamer Bear) with hack-and-leak campaigns from Ukraine and the United kingdom.
One team, nevertheless, Frozenbarents (aka Sandworm, Voodoo Bear), dubbed “the GRU’s most functional operator” by Google, ran all sorts of cyber-attacks in opposition to Ukraine and NATO nations around the world.
“While we see these attackers aim heavily on the Ukrainian federal government and military entities, the campaigns we disrupted also demonstrate a strong concentrate on critical infrastructure, utilities and community solutions, and the media and data place,” the report reads.
However, the report also famous that quite a few of these functions led to “mixed outcomes.”
A very good case in point is the Industroyer 2 attempted attack on the Ukrainian energy sector, which appeared to have unsuccessful.
Overt and Covert Disinformation Strategies
Together with these uncomplicated cyber-attacks, the report confirmed that Russia has been functioning all forms of data functions (IO) strategies, from the most overt state-sponsored disinformation campaigns operate by the infamous St-Petersburg-based ‘troll farm,’ the Internet Investigate Agency (IRA), to more covert strategies run by affiliates like the Russian consulting company Krymskybridge or groups connected with Russian intelligence.
Google claimed it “disrupted in excess of 1950 circumstances of Russian IO exercise in 2022,” concentrating on the two Russian and overseas audiences.
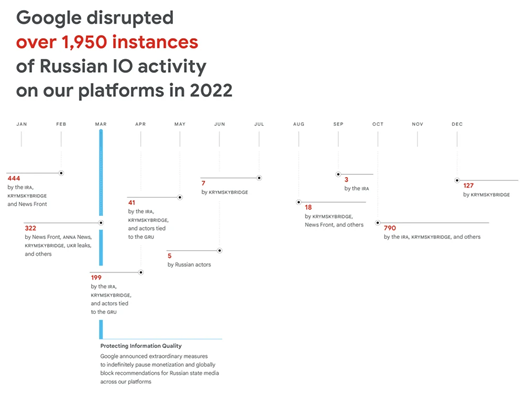 Source: Google
Source: Google
The report also showed that “the war has break up the loyalties of economically inspired attackers, [which has increased] the overlap amongst [them] and governing administration-backed menace actors.”
This phenomenon is most effective represented by the fate of the Conti gang, which counted the two Russian and Ukrainian users and exploded immediately after some of its alleged leaders publicly supported the invasion.
“This change in the Jap European cyber-legal ecosystem will possible have lengthy-expression implications for coordination in between prison teams and the scale of cybercrime around the globe,” notes the report.
Wanting forward, Google believes “with significant self-assurance that Russian govt-backed attackers will proceed to perform cyber-attacks versus Ukraine and NATO partners, increase disruptive and harmful attacks in reaction to developments on the battlefield [and] more and more expand to incorporate NATO associates.
The scientists also assume “with moderate self esteem, that Russia will carry on to raise the rate and scope of IO, significantly as we technique critical moments like international funding, navy support, domestic referendums, and far more.
Some parts of this article are sourced from:
www.infosecurity-journal.com


 COVID calculations spur solution to old problem in computer science
COVID calculations spur solution to old problem in computer science