A 1st-of-its-kind malware targeting Amazon Web Services’ (AWS) Lambda serverless computing system has been learned in the wild.
Dubbed “Denonia” immediately after the identify of the area it communicates with, “the malware makes use of newer tackle resolution strategies for command and handle targeted visitors to evade regular detection measures and virtual network access controls,” Cado Labs researcher Matt Muir said.

The artifact analyzed by the cybersecurity organization was uploaded to the VirusTotal database on February 25, 2022, sporting the name “python” and packaged as a 64-bit ELF executable.
On the other hand, the filename is a misnomer, as Denonia is programmed in Go and harbors a custom made variant of the XMRig cryptocurrency mining program. That claimed, the method of original accessibility is unknown, though it truly is suspected it could have included the compromise of AWS Accessibility and Solution Keys.
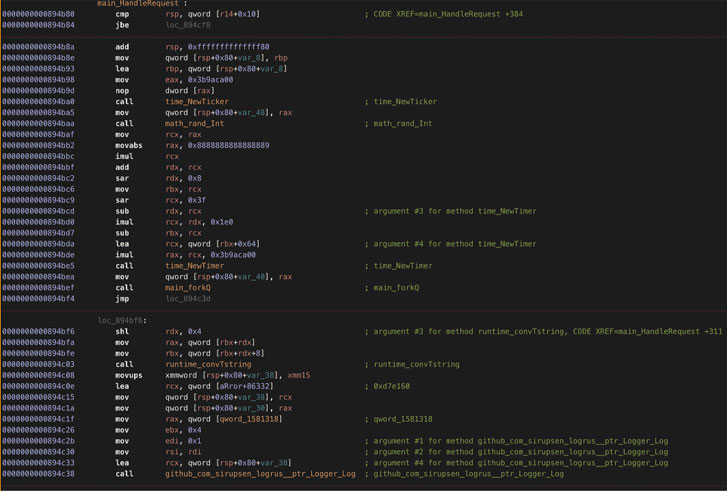
Yet another noteworthy attribute of the malware is its use of DNS around HTTPS (DoH) for speaking with its command-and-regulate server (“gw.denonia[.]xyz”) by concealing the traffic inside encrypted DNS queries.

Nonetheless, “python” isn’t really the only sample of Denonia unearthed so much, what with Cado Labs obtaining a 2nd sample (named “bc50541af8fe6239f0faa7c57a44d119.virus”) that was uploaded to VirusTotal on January 3, 2022.
“Although this first sample is quite innocuous in that it only operates crypto-mining software program, it demonstrates how attackers are using advanced cloud-certain know-how to exploit advanced cloud infrastructure, and is indicative of probable foreseeable future, extra nefarious assaults,” Muir said.
Uncovered this posting interesting? Follow THN on Fb, Twitter and LinkedIn to read through a lot more unique articles we article.
Some parts of this article are sourced from:
thehackernews.com


 OpenAI's DALL-E 2 produces fantastical images of most anything you can imagine
OpenAI's DALL-E 2 produces fantastical images of most anything you can imagine