An investigation of two ransomware assaults has recognized overlaps in the practices, procedures, and techniques (TTPs) amongst BlackCat and BlackMatter, indicating a powerful connection between the two groups.
Although it is usual of ransomware teams to rebrand their functions in response to increased visibility into their attacks, BlackCat (aka Alphv) marks a new frontier in that the cyber criminal offense cartel is created out of affiliates of other ransomware-as-a-provider (RaaS) functions.
BlackCat 1st emerged in November 2021 and has since targeted many businesses throughout the world over the earlier handful of months. It has been referred to as out for staying equivalent to BlackMatter, a small-lived ransomware spouse and children that originated from DarkSide, which attracted notoriety for its substantial-profile attack on Colonial Pipeline in May possibly 2021.

In an interview with Recorded Future’s The Record last month, a BlackCat consultant dismissed rumors that it is really a rebranding of BlackMatter, when noting that it truly is built up of affiliates linked with other RaaS teams.
“In part, we are all connected to gandrevil [GandCrab / REvil], blackside [BlackMatter / DarkSide], mazegreggor [Maze / Egregor], lockbit, etcetera., mainly because we are adverts (aka affiliates),” the unnamed agent was quoted as stating. “We borrowed their pros and removed their drawbacks.”

“BlackCat appears to be to be a circumstance of vertical business enterprise expansion,” Cisco Talos researchers Tiago Pereira and Caitlin Huey explained. “In essence, it really is a way to management the upstream supply chain by creating a provider that is key to their business enterprise (the RaaS operator) improved suited for their needs and introducing yet another source of revenue.”
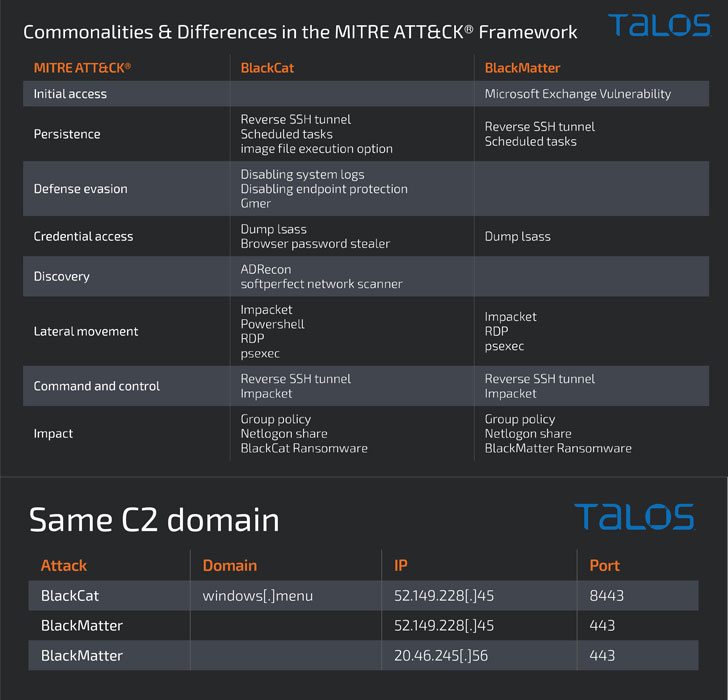
What is actually much more, the cybersecurity firm reported it noticed a variety of commonalities involving a BlackMatter attack in September 2021 and that of a BlackCat attack from December 2021, such as the tools and the file names made use of as very well as a domain employed to preserve persistent access to the focus on network.
This overlapping use of the identical command-and-command address has raised the risk that the affiliate that used BlackMatter was probably 1 of the early adopters of BlackCat, with both equally the attacks taking a lot more than 15 days to get to the encryption stage.
“As we have seen a number of periods before, RaaS services appear and go. Their affiliates, nonetheless, are possible to just move on to a new company. And with them, lots of of the TTPs are very likely to persist,” the researchers stated.
The conclusions come as BlackBerry comprehensive a new .NET-based ransomware spouse and children identified as LokiLocker that not only encrypts the data files but also incorporates an optional wiper features that is developed to erase all non-procedure information and overwrite the learn boot file (MBR) must a sufferer refuse to pay up inside of a specified timeframe.
“LokiLocker will work as a constrained-access ransomware-as-a-support scheme that seems to be marketed to a relatively small selection of diligently vetted affiliates powering closed doorways,” the scientists claimed. Energetic considering that at minimum August 2021, a the greater part of victims detected so far are concentrated in Jap Europe and Asia.
Located this post attention-grabbing? Stick to THN on Fb, Twitter and LinkedIn to read through much more exceptional content material we write-up.
Some parts of this article are sourced from:
thehackernews.com



