The infamous Emotet malware, in its return soon after a limited hiatus, is now being dispersed via Microsoft OneNote email attachments in an endeavor to bypass macro-dependent security limitations and compromise programs.
Emotet, connected to a risk actor tracked as Gold Crestwood, Mummy Spider, or TA542, carries on to be a potent and resilient threat despite attempts by legislation enforcement to just take it down.
A spinoff of the Cridex banking worm – which was subsequently replaced by Dridex about the similar time GameOver Zeus was disrupted in 2014 – Emotet has evolved into a “monetized system for other danger actors to run malicious strategies on a spend-for each-put in (PPI) design, allowing for theft of sensitive details and ransom extortion.”
Even though Emotet infections have acted as a conduit to produce Cobalt Strike, IcedID, Qakbot, Quantum ransomware, and TrickBot, its return in late 2021 was facilitated by signifies of TrickBot.
“Emotet is known for prolonged intervals of inactivity, frequently taking place multiple times for each year, where by the botnet maintains a continual-state but does not supply spam or malware,” Secureworks notes in its profile of the actor.
The dropper malware is typically dispersed by spam email messages that contains destructive attachments. But with Microsoft getting measures to block macros in downloaded Workplace files, OneNote attachments have emerged as an desirable alternate pathway.
“The OneNote file is very simple but still successful at social engineering consumers with a pretend notification stating that the document is secured,” Malwarebytes disclosed in a new alert. “When instructed to double-click on the Look at button, victims will inadvertently double-click on an embedded script file in its place.”
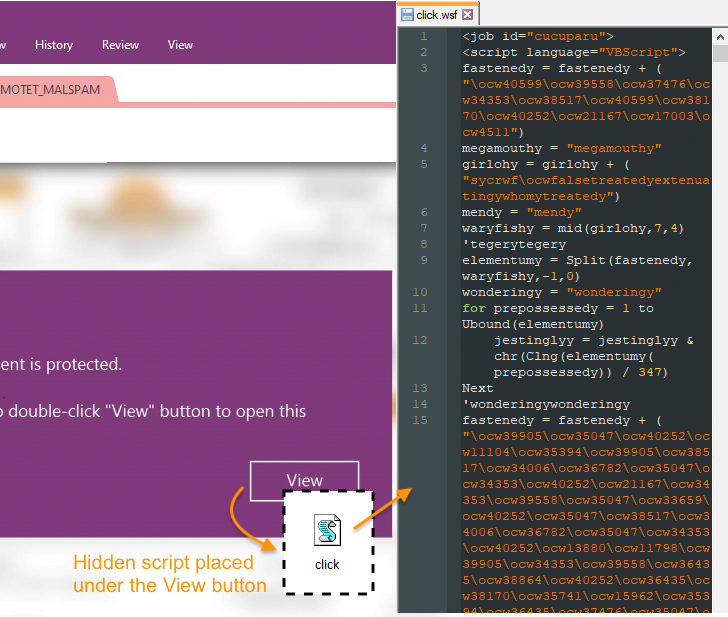
The Windows Script File (WSF) is engineered to retrieve and execute the Emotet binary payload from a remote server. Identical findings have been echoed by Cyble, IBM X-Drive, and Palo Alto Networks Unit 42.
That said, Emotet nevertheless carries on to use booby-trapped files that contains macros to produce the malicious payload, utilizing social engineering lures to entice end users into enabling macros to activate the attack chain.
WEBINARDiscover the Hidden Risks of 3rd-Celebration SaaS Apps
Are you mindful of the challenges related with 3rd-celebration application access to your firm’s SaaS applications? Be a part of our webinar to learn about the varieties of permissions becoming granted and how to limit risk.
RESERVE YOUR SEAT
These kinds of documents have been noticed to leverage a system known as decompression bomb to conceal a very significant file (about 550 MB) inside of ZIP archive attachments to fly less than the radar, in accordance to multiple experiences from Cyble, Deep Intuition, Hornetsecurity, and Development Micro.
This is attained by padding 00-byte at the close of the document to artificially inflate the file size so as to exceed the limits imposed by anti-malware solutions.
The hottest development is a indication of the operators’ adaptability and agility in switching attachment forms for preliminary shipping to evade detection signatures. It also arrives amid a spike in menace actors utilizing OneNote paperwork to distribute a large variety of malware this kind of as AsyncRAT, Icedid, RedLine Stealer, Qakbot, and XWorm.
In accordance to Trellix, a bulk of the destructive OneNote detections in 2023 have been reported in the U.S., South Korea, Germany, Saudi Arabia, Poland, India, the U.K., Italy, Japan, and Croatia, with manufacturing, substantial-tech, telecom, finance, and power rising as the major specific sectors.
Discovered this short article interesting? Abide by us on Twitter and LinkedIn to browse more unique articles we write-up.
Some parts of this article are sourced from:
thehackernews.com


 New technology turns smartphones into RFID readers, saving costs and reducing waste
New technology turns smartphones into RFID readers, saving costs and reducing waste