An emerging ransomware pressure in the threat landscape statements to have breached 30 organizations in just four months because it went operational, riding on the coattails of a notorious ransomware syndicate.
To start with observed in February 2021, “Prometheus” is an offshoot of another nicely-recognized ransomware variant known as Thanos, which was previously deployed towards state-run organizations in the Middle East and North Africa past 12 months.
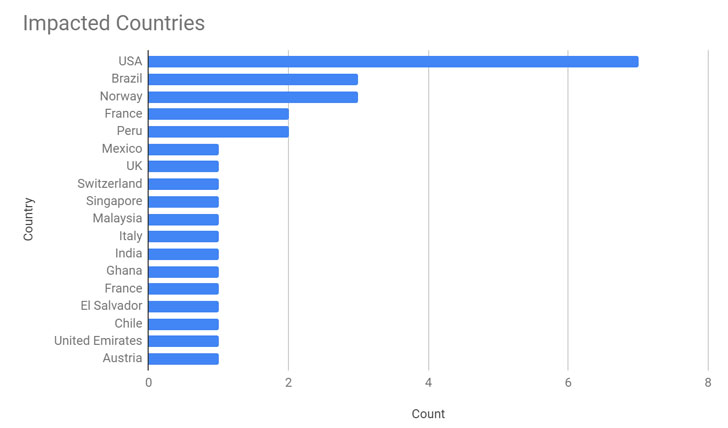
The afflicted entities are considered to be authorities, financial solutions, production, logistics, consulting, agriculture, healthcare companies, insurance policies companies, electricity and regulation firms in the U.S., U.K., and a dozen extra international locations in Asia, Europe, the Middle East, and South The us, in accordance to new investigate released by Palo Alto Networks’ Unit 42 risk intelligence workforce.

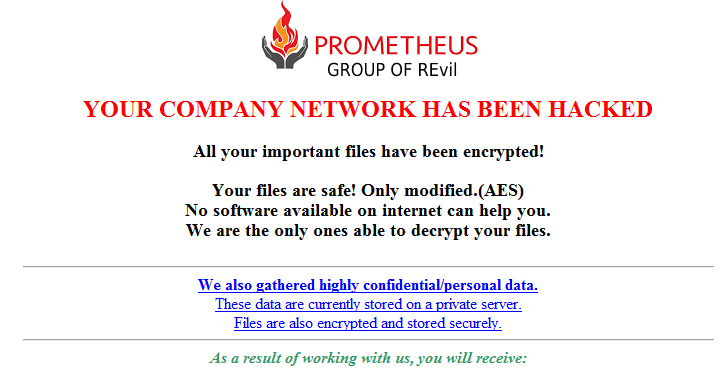
Like other ransomware gangs, Prometheus normally takes advantage of double-extortion strategies and hosts a dark web leak web-site, wherever it names and shames new victims and tends to make stolen data accessible for invest in, at the identical time taking care of to inject a veneer of professionalism into its prison actions.
“Prometheus operates like a qualified organization,” Doel Santos, Unit 42 risk intelligence analyst, mentioned. “It refers to its victims as ‘customers,’ communicates with them utilizing a buyer services ticketing program that warns them when payment deadlines are approaching and even takes advantage of a clock to count down the hrs, minutes and seconds to a payment deadline.”
On the other hand, only 4 of people 30 influenced companies opted to pay ransoms to date, the cybersecurity firm’s analysis disclosed, like a Peruvian agricultural firm, a Brazilian healthcare providers provider, and two transportation and logistics corporations in Austria and Singapore.
It truly is really worth noting that despite Prometheus’ strong backlinks to Thanos, the gang professes to be a “team of REvil,” just one of the most prolific and notorious ransomware-as-a-services (RaaS) cartels in recent many years, which the researchers speculate could be an try to deflect awareness from Thanos or a deliberate ploy to trick victims into spending up by piggybacking on an established procedure.
Even though the ransomware’s intrusion route continues to be unclear as still, it really is predicted that the team obtained accessibility to target networks or staged spear-phishing and brute-power assaults to gain initial access. Subsequent a thriving compromise, the Prometheus modus operandi consists of terminating backup and security software program-similar processes on the technique to lock the documents guiding encryption obstacles.

“The Prometheus ransomware operators create a unique payload for each target, which is applied for their negotiation web page to recuperate files,” Santos reported, introducing the ransom demand from customers ranges any place between $6,000 and $100,000 based on the sufferer business, a value that gets doubled if the target fails to pay up inside the specified time period of time.
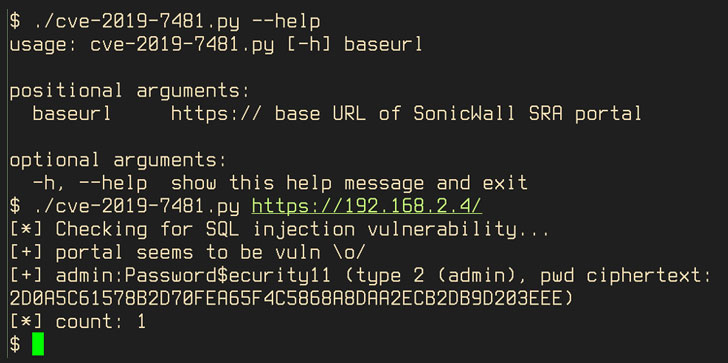
The enhancement also will come as cybercrime groups are more and more targeting SonicWall gadgets to breach company networks and deploy ransomware. A report published by CrowdStrike this week located evidence of distant entry vulnerabilities (CVE-2019-7481) in SonicWall SRA 4600 VPN appliances currently being exploited as an original access vector for ransomware assaults concentrating on companies around the globe.
Discovered this write-up exciting? Abide by THN on Fb, Twitter and LinkedIn to browse much more special written content we submit.
Some parts of this article are sourced from:
thehackernews.com

 High Street Banks Exposing Customers to Phishing Attacks
High Street Banks Exposing Customers to Phishing Attacks