Numerous security weaknesses have been disclosed in MediaTek process-on-chips (SoCs) that could have enabled a menace actor to elevate privileges and execute arbitrary code in the firmware of the audio processor, properly allowing for the attackers to have out a “significant eavesdrop marketing campaign” without the need of the users’ knowledge.
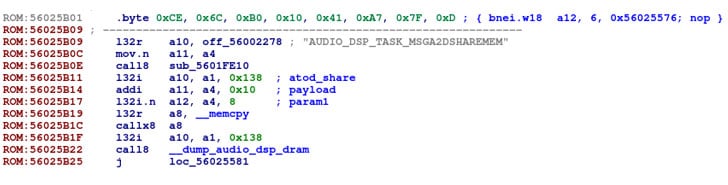
The discovery of the flaws is the end result of reverse-engineering the Taiwanese company’s audio electronic signal processor (DSP) device by Israeli cybersecurity business Look at Position Investigation, finally locating that by stringing them together with other flaws current in a smartphone manufacturer’s libraries, the issues uncovered in the chip could direct to local privilege escalation from an Android application.

“A malformed inter-processor message could perhaps be utilized by an attacker to execute and hide destructive code inside of the DSP firmware,” Check Stage security researcher Slava Makkaveev explained in a report. “Given that the DSP firmware has entry to the audio facts move, an attack on the DSP could potentially be utilized to eavesdrop on the consumer.”
Tracked as CVE-2021-0661, CVE-2021-0662, and CVE-2021-0663, the three security issues issue a heap-based mostly buffer overflow in the audio DSP element that could be exploited to reach elevated privileges. The flaws effects chipsets MT6779, MT6781, MT6785, MT6853, MT6853T, MT6873, MT6875, MT6877, MT6883, MT6885, MT6889, MT6891, MT6893, and MT8797 spanning throughout versions 9., 10., and 11. of Android.
“In audio DSP, there is a achievable out of bounds create owing to an incorrect bounds look at. This could direct to area escalation of privilege with Procedure execution privileges required. User conversation is not wanted for exploitation,” the chipmaker reported in an advisory posted past month.
A fourth issue uncovered in the MediaTek audio hardware abstraction layer aka HAL (CVE-2021-0673) has been set as of Oct and is anticipated to be printed in the December 2021 MediaTek Security Bulletin.

In a hypothetical attack scenario, a rogue app set up via social engineering means could leverage its entry to Android’s AudioManager API to concentrate on a specialized library — named Android Aurisys HAL — that is provisioned to communicate with the audio drivers on the system and ship specifically crafted messages, which could end result in the execution of attack code and theft of audio-relevant facts.
MediaTek, adhering to disclosure, said it has produced appropriate mitigations accessible to all primary devices companies, including it observed no evidence that the flaws are presently being exploited. Additionally, the business has proposed end users to update their devices as and when patches turn out to be available and to only put in programs from reliable marketplaces these as the Google Play Retail outlet.
Discovered this write-up exciting? Abide by THN on Fb, Twitter and LinkedIn to read through more exclusive content material we publish.
Some parts of this article are sourced from:
thehackernews.com


 Samsung's Galaxy Watch 4 hits an all-time low of $180
Samsung's Galaxy Watch 4 hits an all-time low of $180