The analyst from FireEye that discovered the SolarWinds attack and the co-founder of Tenable will be part of the advisory board of Trinity Cyber – contributing expertise to the enterprise that counts former homeland security adviser Tom Bossert between its leading executives.
Information of the superior-profile new additions – Michael Sikorski, the head of FireEye’s FLARE reverse engineering and menace examination staff and Ron Gula – arrives with an announcement of and undisclosed quantity of funding from the latter’s enterprise money firm, Gula Tech Adventures.
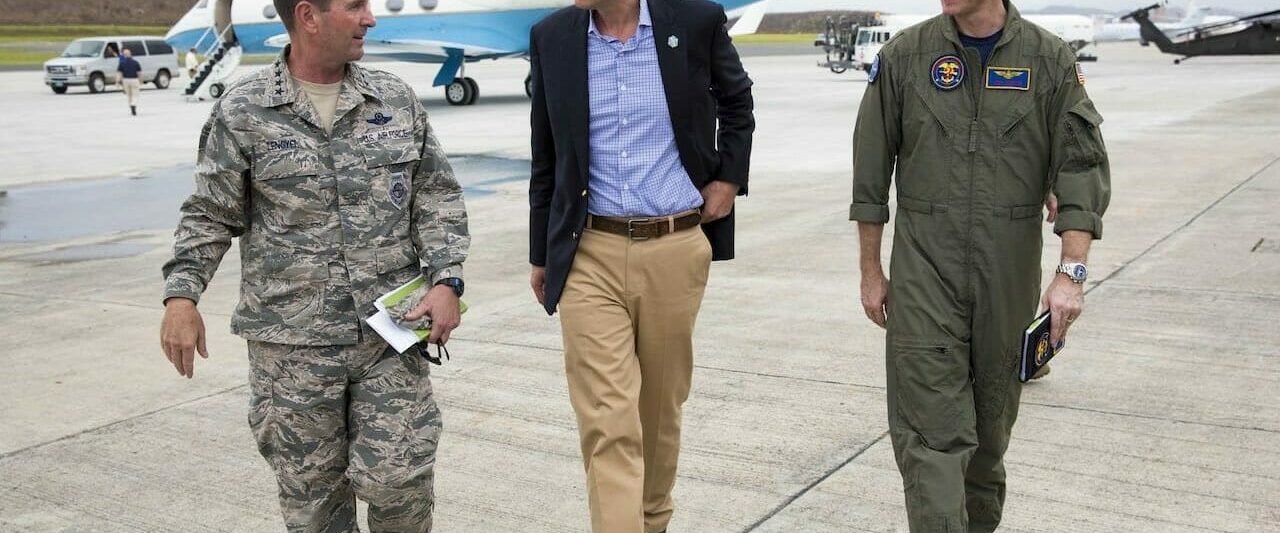
“Don’t just take Tom Bossert’s phrase on Trinity Cyber. He was just the previous homeland security advisor. He operates the company, so probably he’s self-intrigued,” mentioned Bossert, Trinity Cyber’s president and previous formal with the two the Trump and George W. Bush administrations. “Maybe it’s just the plan guy who doesn’t understand the tech. But you cannot ignore Ron Gula and Mike Sikorski.”
Trinity Cyber describes its alternative as a vintage guy-in-the center-attack, reconfigured for protection. It advertises a low-latency means to scan and modify site visitors going in and out of the network, detect exploits in files without demanding signatures, change compromised files currently being downloaded or information as it’s exfiltrated, even mimic a process beaconing that malware experienced been installed right after blocking it from becoming downloaded.
This form of ability, stated Sikorski, would be especially profound in scenarios related to the SolarWinds attack, the place hackers have been capable to confound conventional indicators of compromise. He discovered several points in the cycle of infection in which Trinity Cyber would be in a position to detect the intruder: the HTTP command and command assistance hiding in intrusion telemetry, the Cobolt Strike communications, DNS CNAME patterned visitors, and communications to and from web shells. But, he claimed, it’s the product’s capability to be ready to react to assaults even though detecting them that drew him to the business.
“Something we have always required to have is the means to mess with the thieves, live, as they are attacking,” Sikorski stated. “If somebody is scanning you for a vulnerability, Trinity can occur back again and say, ‘Oh, basically, we’re patched. So now, instead of rushing all around to patch just about every solitary process, there’s a technology that will notify the attacker it’s excellent, even if it’s not.”
The lively protection functionality can keep an attacker hectic whilst defenders investigate the scope of the intrusion, he continued. That can lessen a key friction position through the incident reaction approach, exactly where victims are inclined to desire not making it possible for an attacker to get authentic data files.
“For incident responders, it’s actually tough to tell a customer, ‘please really don’t switch these points off till I determine out what is going on,’ when you see what’s getting stolen off the network. You require to get the customer snug with factors receiving robbed from them,” Sikorski reported.
In that perception, Trinity Cyber can buy time to determine out what the attacker is performing just before tipping your hand. As Sikorski place it, “if an attacker pulls back a corrupted zip file, they are going to think they created the mistake.”
Maryland-dependent Trinity Cyber was founded in 2016. Its most latest spherical of funding netted $23 million in 2019 and was led by Intel Cash. Bossert arrived on board all around the very same time, his first non-public-sector stint immediately after serving as homeland security advisor for the Trump administration, throughout the NotPetya and WannaCry assaults. Bossert continues to be enthusiastic about the solution.
“This is the technology that Einstein really should have been,” claimed Bossert, referring to the sensors employed to protect federal networks.
Some parts of this article are sourced from:
www.scmagazine.com

 TikTok rivals Instagram Reels and YouTube Shorts: How the two compare on features front
TikTok rivals Instagram Reels and YouTube Shorts: How the two compare on features front