Scientists have disclosed a new relatives of Android malware that abuses accessibility companies in the system to hijack user qualifications and history audio and movie.
Dubbed “Oscorp” by Italy’s CERT-AGID, the malware “induce(s) the person to set up an accessibility services with which [the attackers] can browse what is existing and what is typed on the screen.”
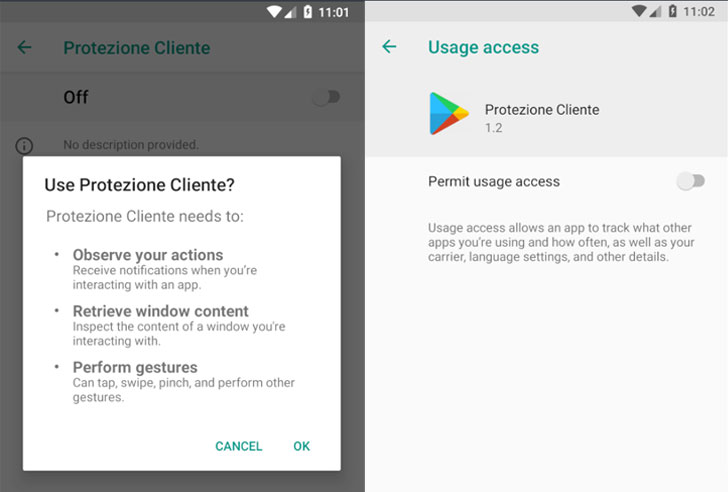
So named because of the title of the login web site of its command-and-manage (C2) server, the destructive APK (termed “Assistenzaclienti.apk” or “Consumer Protection”) is distributed through a area named “supportoapp[.]com,” which on set up, requests intrusive permissions to allow the accessibility services and establishes communications with a C2 server to retrieve further instructions.

Also, the malware frequently reopens the Settings screen just about every 8 seconds till the user turns on permissions for accessibility and device use figures, so pressurizing the consumer into granting the further privileges.
The moment the entry is provisioned, the malware exploits the permissions to log keystrokes, uninstall apps on the gadget, make phone calls, send SMS messages, steal cryptocurrency by redirecting payments made via Blockchain.com Wallet application, and obtain two-aspect authentication codes from the Google Authenticator app.
The attacker-controlled wallet experienced $584 as of January 9, the scientists mentioned.
In the ultimate move, the malware exfiltrates the captured knowledge — together with procedure info (e.g., apps mounted, phone product, provider) — to the C2 server, in addition to fetching commands from the server that will allow it to launch the Google Authenticator app, steal SMS messages, uninstall apps, launch precise URLs, and document audio and video of the display by way of WebRTC.
What’s more, people opening the apps targeted by the malware are displayed a phishing site that asks for their username and password, CERT mentioned, incorporating the design and style of this screen varies from app to app and that it really is intended with an intent to trick the victim into giving the information and facts.
The actual form of purposes singled out by this malware remains unclear, but the researchers explained it could be any app that discounts with delicate info, this sort of as those people for banking and messaging.
“Android protections stop malware from doing any type of problems till the user permits [accessibility] service,” CERT-AGID concluded. “As soon as enabled, on the other hand, a ‘dam’ opens up. In simple fact, Android has always had a very permissive coverage to application developers, leaving the ultimate determination to rely on an app or not to the close consumer.”
Identified this write-up intriguing? Abide by THN on Facebook, Twitter and LinkedIn to read additional special articles we put up.
Some parts of this article are sourced from:
thehackernews.com

 Trinity Cyber snags big-name board additions
Trinity Cyber snags big-name board additions