Twin cyber operations conducted by state-sponsored Iranian threat actors demonstrate their ongoing focus on compiling specific dossiers on Iranian citizens that could threaten the security of the Islamic Republic, together with dissidents, opposition forces, and ISIS supporters, and Kurdish natives.
Tracing the intensive espionage functions to two superior Iranian cyber-groups Domestic Kitten (or APT-C-50) and Infy, cybersecurity agency Check out Point disclosed new and recent proof of their ongoing things to do that contain the use of a revamped malware toolset as effectively as tricking unwitting users into downloading destructive software below the guise of well known applications.
“The two groups have performed extensive-jogging cyberattacks and intrusive surveillance campaigns which goal both equally individuals’ cellular products and private desktops,” Check out Stage researchers claimed in a new investigation. “The operators of these strategies are clearly energetic, responsive and consistently trying to find new attack vectors and strategies to ensure the longevity of their functions.”

Regardless of overlaps in the victims and the variety of facts amassed, the two menace actors are viewed as to be independently running from 1 a different. But the “synergistic outcome” designed by applying two different sets of attack vectors to strike the very same targets simply cannot be missed, the researchers claimed.
Domestic Kitten Mimics a Tehran Cafe App
Domestic Kitten, which has been lively because 2016, has been regarded to focus on precise groups of individuals with destructive Android apps that gather delicate details these types of as SMS messages, get in touch with logs, photographs, films, and spot info on the device along with their voice recordings.
Spotting 4 active campaigns, the most the latest of which commenced in November 2020 according to Check Issue, the APT-C-50 actor has been located to leverage a large selection of include apps, counting VIPRE Mobile Security (a phony cell security application), Unique Bouquets (a repackaged variant of a match accessible on Google Engage in), and Iranian Female Ninja (a wallpaper app), to distribute a piece of malware termed FurBall.
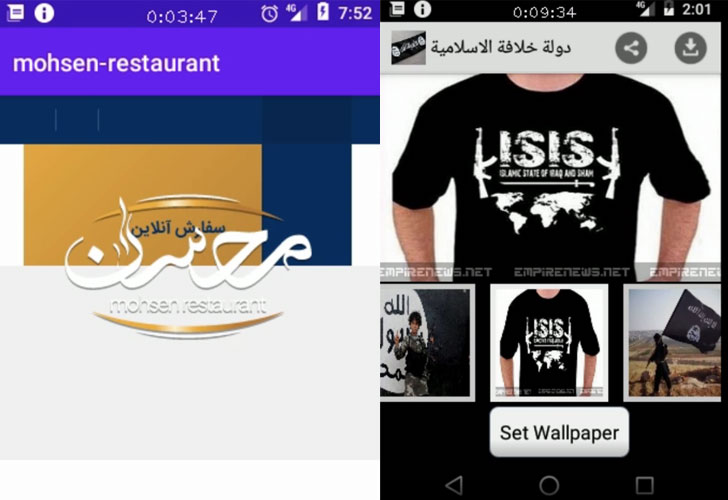
The most current November procedure is no various, which usually takes advantage of a faux app for Mohsen Cafe located in Tehran to accomplish the identical aim by luring victims into setting up the application by a number of vectors — SMS messages with a link to down load the malware, an Iranian blog that hosts the payload, and even shared by using Telegram channels.
Well known targets of the attack incorporated 1,200 persons located in Iran, the US, Wonderful Britain, Pakistan, Afghanistan, Turkey, and Uzbekistan, the researchers stated, with about 600 successful infections noted.
After installed, FurBall grants alone broad permissions to execute the app every time instantly on device startup and proceeds to obtain browser history, components data, data files on the external SD card, and periodically exfiltrate films, images, and contact records just about every 20 seconds.
It also displays clipboard information, gains entry to all notifications received by the machine, and arrives with capabilities to remotely execute instructions issued from a command-and-control (C2) server to history audio, video, and phone phone calls.
Interestingly, FurBall appears to be based on a commercially readily available Adware known as KidLogger, implying the actors “either obtained the KidLogger source-code, or reverse-engineered a sample and stripped all extraneous components, then extra extra capabilities.”
Infy Returns With New, Previously Mysterious, 2nd-Stage Malware
Very first discovered in May perhaps 2016 by Palo Alto Networks, Infy’s (also referred to as Prince of Persia) renewed exercise in April 2020 marks a continuation of the group’s cyber operations that have qualified Iranian dissidents and diplomatic companies across Europe for around a 10 years.
Whilst their surveillance endeavours took a beating in June 2016 next a takedown procedure by Palo Alto Networks to sinkhole the group’s C2 infrastructure, Infy resurfaced in August 2017 with anti-takeover approaches together with a new Windows info-stealer referred to as Foudre.
The group is also recommended to have ties to the Telecommunication Corporation of Iran following researchers Claudio Guarnieri and Collin Anderson disclosed evidence in July 2016 that a subset of the C2 domains redirecting to the sinkhole was blocked by DNS tampering and HTTP filtering, hence stopping accessibility to the sinkhole.
Then in 2018, Intezer Labs observed a new variation of the Foudre malware, identified as model 8, that also contained an “unidentified binary” — now named Tonnerre by Check Place that is utilised to broaden on the capabilities of the previous.
“It looks that subsequent a extended downtime, the Iranian cyber attackers were in a position to regroup, resolve former issues and substantially fortify their OPSEC activities as effectively as the technical proficiency and skills of their equipment,” the scientists claimed.
As many as three variations of Foudre (20-22) have been uncovered considering that April 2020, with the new variants downloading Tonnerre 11 as the next-stage payload.
The attack chain commences by sending phishing emails that contains lure paperwork published in Persian, that when closed, runs a malicious macro that drops and executes the Foudre backdoor, which then connects to the C2 server to obtain the Tonnerre implant.
In addition to executing commands from the C2 server, recording sounds, and capturing screenshots, what will make Tonnerre stand out is its use of two sets of C2 servers — just one to receive commands and download updates making use of HTTP and a 2nd server to which the stolen information is exfiltrated through FTP.
At 56MB, Tonnerre’s unconventional dimension is also probable to perform in its favor and evade detection as lots of suppliers dismiss large files in the course of malware scans, the researchers observed.
On the other hand, unlike Domestic Kitten, only a couple of dozen victims were being located to be qualified in this attack, such as those from Iraq, Azerbaijan, the U.K., Russia, Romania, Germany, Canada, Turkey, the U.S., Netherlands, and Sweden.
“The operators of these Iranian cyber espionage strategies seem to be to be absolutely unaffected by any counter-actions finished by some others, even even though they were being disclosed and even stopped in the earlier — they simply just will not stop,” said Yaniv Balmas, head of cyber study at Check out Level.
“These campaign operators only learn from the earlier, modify their techniques, and go on to hold out for a although for the storm to go to only go at it again. Additionally, it truly is deserving to be aware the sheer amount of methods the Iranian regime is prepared to invest on exerting their regulate.”
Uncovered this article attention-grabbing? Comply with THN on Fb, Twitter and LinkedIn to browse additional unique content we submit.
Some parts of this article are sourced from:
thehackernews.com


 Xiaomi Mi 11 launch event live updates
Xiaomi Mi 11 launch event live updates