VMware’s container-based mostly application enhancement natural environment has develop into appealing to cyberattackers.
Companies working sophisticated virtual networks with VMware’s vSphere services are actively currently being specific by cryptojackers, who have figured out how to inject the XMRig industrial cryptominer into the ecosystem, undetected.
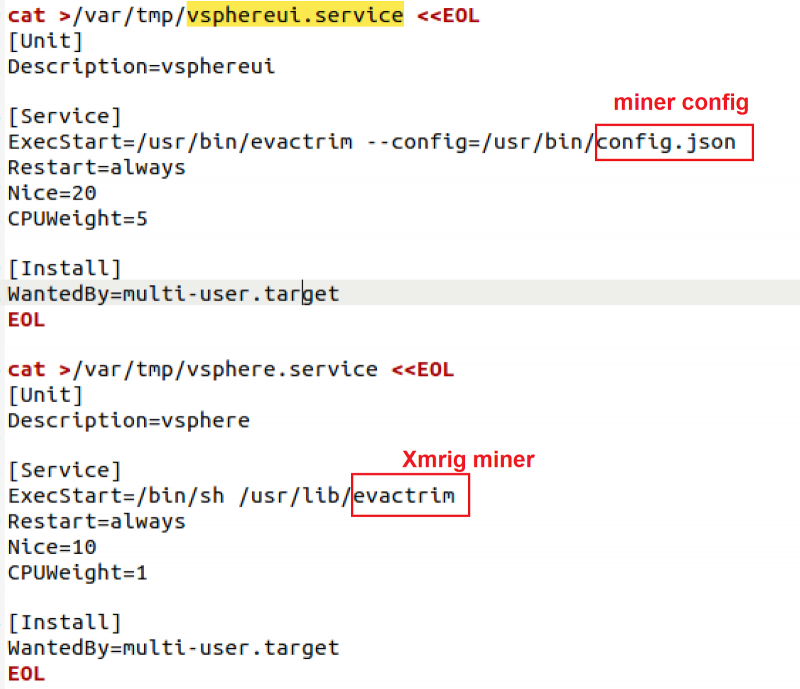
Uptycs’ Siddharth Sharma has launched exploration showing risk actors are making use of malicious shell scripts to make modifications and run the cryptominer on vSphere virtual networks.
“Cryptojacking campaigns mainly focus on the programs having higher-conclusion sources,” Sharma pointed out. “In this marketing campaign as we noticed the attackers tried to sign up the XMRig miner by itself as a support (daemon), which runs any time the procedure gets rebooted.”
To stay clear of detection, the script also downloads a person-method rootkit from the command-and-management server (C2), the report additional.
“The shell script also consists of instructions which down load the miner, the config file and the consumer mode rootkit from the attacker’s web server,” the report defined. “The attackers made use of [the] wget utility to fetch the malicious components and chmod utility to make the elements executable.”
The report mentioned the rootkit gets saved as “libload.so” and the script modifies vSphere to operate the XMRig cryptominer.
Source: Uptycs.
Following the cryptominer is dropped, the script reloads the service to get the miner began, Sharma discussed. The report also reported the attacker’s wallet has been compensated 8.942 XMR, the report said, or about $1,790 as of press time.
VMware Services Underneath Attack
VMware solutions have been beleaguered by current security issues.
The new calendar year kicked off with a substantial-severity bug discovered in VMWare’s Cloud Foundation, ESXi, Fusion and Workstation platforms, which opened the doorway for a hypervisor takeover of an organization’s entire virtualized setting.
And just days in the past VMWare’s Horizon servers with Log4Shell vulnerabilities were being noticed beneath active Cobalt Strike attack by researchers at Huntress following the U.K.’s Countrywide Well being Assistance ended up specific on Jan 5.
Sharma advises security groups jogging VMware expert services to glance for unconventional network action to detect the cryptominer, as nicely as other assaults.
“In the previous we have found extremely advanced teams focusing on susceptible VMware companies,” Sharma reported. “Hence it gets to be truly critical to watch the suspicious procedures, functions and network visitors spawned on the execution of any untrusted shell script.”
Password Reset: On-Need Function: Fortify 2022 with a password-security method built for today’s threats. This Threatpost Security Roundtable, built for infosec professionals, centers on business credential administration, the new password fundamental principles and mitigating article-credential breaches. Sign up for Darren James, with Specops Software and Roger Grimes, protection evangelist at KnowBe4 and Threatpost host Becky Bracken. Register & stream this Totally free session today – sponsored by Specops Program.
Some parts of this article are sourced from:
threatpost.com

