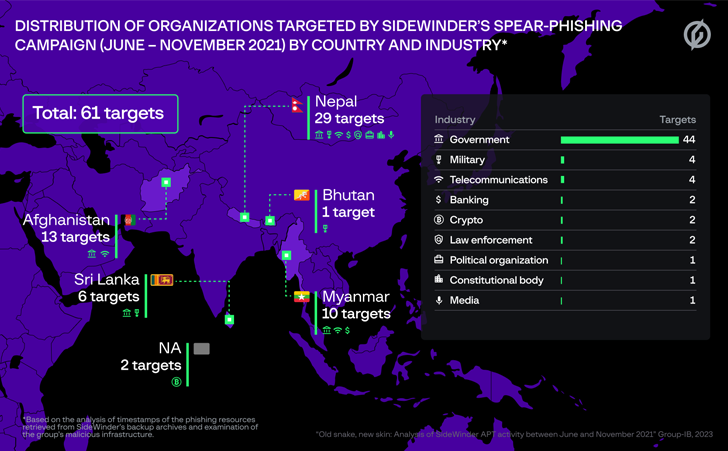
The prolific SideWinder group has been attributed as the nation-state actor guiding attempted attacks towards 61 entities in Afghanistan, Bhutan, Myanmar, Nepal, and Sri Lanka amongst June and November 2021.
Targets included federal government, armed service, legislation enforcement, banks, and other corporations, in accordance to an exhaustive report revealed by Group-IB, which also identified hyperlinks concerning the adversary and two other intrusion sets tracked as Toddler Elephant and DoNot Crew.
SideWinder is also referred to as APT-C-17, Hardcore Nationalist (HN2), Rattlesnake, Razor Tiger, and T-APT4. It really is suspected to be of Indian origin, while Kaspersky in 2022 noted that the attribution is no more time deterministic.
The group has been linked to no considerably less than 1,000 attacks from federal government organizations in the Asia-Pacific location due to the fact April 2020, in accordance to a report from the Russian cybersecurity company early past calendar year.
Of the 61 probable targets compiled by Team-IB, 29 of them are located in Nepal, 13 in Afghanistan, 10 in Myanmar, 6 in Sri Lanka, and one is based out of Bhutan.
Regular attack chains mounted by the adversary start out with spear-phishing email messages made up of an attachment or a booby-trapped URL that directs the victims to an middleman payload that is made use of to fall the ultimate-stage malware.
SideWinder is also stated to have additional a slate of new tools to its procedure, which includes a remote accessibility trojan and an info stealer written in Python that’s capable of exfiltrating delicate data stored in a victim’s laptop or computer by way of Telegram.
“Highly developed attackers have started preferring Telegram around traditional command and management servers owing to its ease,” Team-IB reported.
The Singapore-headquartered corporation further claimed it uncovered evidence tying the actor to a 2020 attack aimed at the Maldivian governing administration, in addition to developing infrastructure and tactical overlaps in between SideWinder, Infant Elephant, and DoNot Staff.
Although DoNot Team is recognised to have an desire in Bangladesh, India, Nepal, Pakistan, and Sri Lanka, Baby Elephant was initial documented by Chinese cybersecurity company Antiy Labs in 2021 as an superior persistent risk from India concentrating on government and defense agencies in China and Pakistan.
“Given that 2017, the quantity of ‘Baby Elephant’ assaults has doubled each 12 months, and the attack solutions and means have progressively turn into richer, and the focus on has started off to protect a lot more areas in South Asia,” the organization was quoted as stating to Chinese state media outlet World wide Occasions at the time.
Additionally, source code similarities have been unearthed involving the malware deployed by SideWinder as very well as those employed by other groups with a South Asian focus, this sort of as Clear Tribe, Patchwork (aka Hangover), and DoNot Group.
“This facts suggests that state-sponsored threat actors are joyful to borrow resources from a single a different and adjust them for their desires,” Team-IB claimed.
The capacity of the danger actor to repeatedly refine its toolset based on its evolving priorities can make it a specially dangerous actor functioning in the espionage region.
“The team naturally has substantial fiscal resources and is most likely condition-sponsored, presented the truth that SideWinder has been able to be energetic for so extended, build new resources, and retain a relatively large network infrastructure.”
Found this posting intriguing? Follow us on Twitter and LinkedIn to browse much more exceptional written content we submit.
Some parts of this article are sourced from:
thehackernews.com


 Hackers Using Google Ads to Spread FatalRAT Malware Disguised as Popular Apps
Hackers Using Google Ads to Spread FatalRAT Malware Disguised as Popular Apps