A well known npm bundle with more than 3.5 million weekly downloads has been identified susceptible to an account takeover attack.
“The bundle can be taken over by recovering an expired area title for a person of its maintainers and resetting the password,” software package source chain security business Illustria explained in a report.
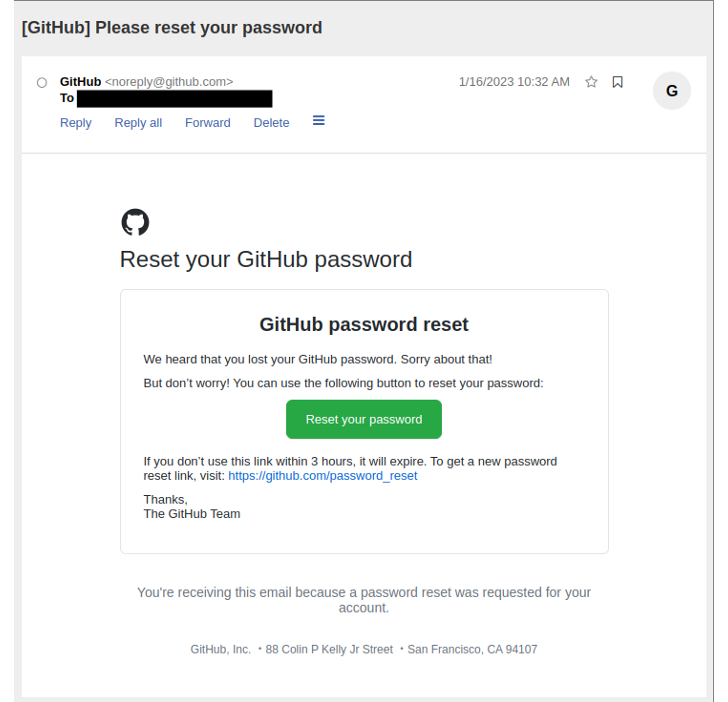
While npm’s security protections restrict consumers to have only 1 active email address for each account, the Israeli company mentioned it was ready to reset the GitHub password applying the recovered domain.
The attack, in a nutshell, grants a danger actor entry to the package’s involved GitHub account, efficiently generating it doable to publish trojanized versions to the npm registry that can be weaponized to perform offer chain attacks at scale.
This is accomplished by having gain of a GitHub Action which is configured in the repository to mechanically publish the offers when new code modifications are pushed.
“Even however the maintainer’s npm user account is correctly configured with [two-factor authentication], this automation token bypasses it,” Bogdan Kortnov, co-founder and CTO of Illustria, reported.
Illustria did not disclose the title of the module, but pointed out that it reached out to its maintainer, who has given that taken steps to secure the account.
This is not the 1st time developer accounts have been identified vulnerable to takeovers in new several years. In May well 2022, a risk actor registered an expired area used by the maintainer associated with the ctx Python package to seize management of the account and distribute a malicious variation.
Discovered this posting intriguing? Observe us on Twitter and LinkedIn to read far more distinctive articles we write-up.
Some parts of this article are sourced from:
thehackernews.com


 Researchers Link SideWinder Group to Dozens of Targeted Attacks in Multiple Countries
Researchers Link SideWinder Group to Dozens of Targeted Attacks in Multiple Countries