In what is actually a continuing assault on the open source ecosystem, above 15,000 spam offers have flooded the npm repository in an attempt to distribute phishing inbound links.
“The offers had been made applying automated processes, with venture descriptions and automobile-created names that carefully resembled just one an additional,” Checkmarx researcher Yehuda Gelb claimed in a Tuesday report.
“The attackers referred to retail internet websites applying referral IDs, so profiting from the referral rewards they acquired.”
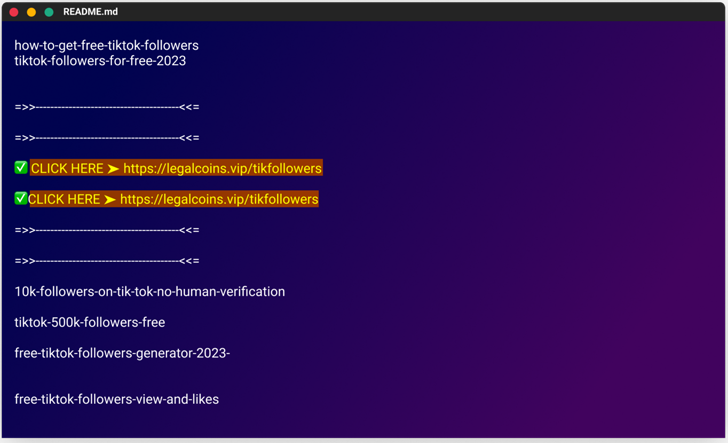
The modus operandi involves poisoning the registry with rogue packages that incorporate links to phishing campaigns in their README.md data files, evocative of a comparable campaign the software package supply chain security agency exposed in December 2022.
The faux modules masqueraded as cheats and free methods, with some deals named as “cost-free-tiktok-followers,” “absolutely free-xbox-codes,” and “instagram-followers-totally free.”
The best aim of the procedure is to entice end users into downloading the deals and clicking on the hyperlinks to the phishing internet sites with bogus claims of elevated followers on social media platforms.
“The deceptive web internet pages are well-designed and, in some conditions, even contain phony interactive chats that show up to display buyers receiving the activity cheats or followers they have been promised,” Gelb described.
The internet websites urge victims to fill out surveys, which then pave the way for added surveys or, alternatively, redirect them to legit e-commerce portals like AliExpress.
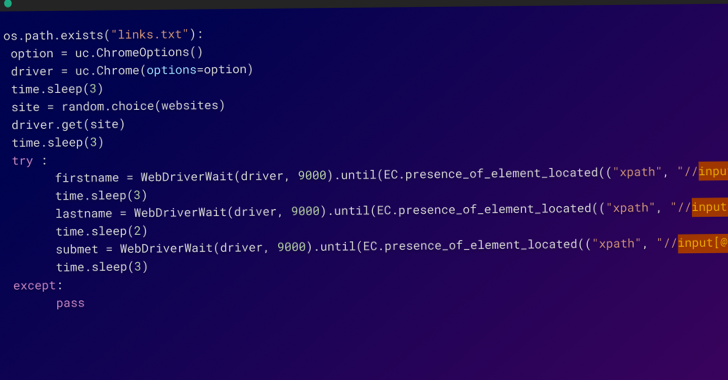
The packages are mentioned to have been uploaded to npm from a number of user accounts inside of hours among February 20 and 21, 2023, using a Python script that automates the whole method.
What is actually extra, the Python script is also engineered to append backlinks to the posted npm offers on WordPress web sites operated by the menace actor that claim to provide Family Island cheats.
This is realized by applying the selenium Python package deal to interact with the internet sites and make the necessary modifications.
In all, the use of automation allowed the adversary to publish a big variety of deals in a quick span of time, not to point out generate many person accounts to conceal the scale of the attack.
“This displays the sophistication and willpower of these attackers, who ended up keen to invest sizeable resources in order to have out this marketing campaign,” Gelb mentioned.
The results when yet again reveal the worries in securing the software program offer chain, as menace actors continue on to adapt with “new and surprising tactics.”
Located this post exciting? Comply with us on Twitter and LinkedIn to go through a lot more unique information we article.
Some parts of this article are sourced from:
thehackernews.com

 3 Steps to Automate Your Third-Party Risk Management Program
3 Steps to Automate Your Third-Party Risk Management Program