Google has tackled yet a further actively exploited zero-working day in Chrome browser, marking the 2nd these kinds of repair introduced by the corporation inside of a month.
The browser maker on Friday delivered 89..4389.90 for Windows, Mac, and Linux, which is anticipated to be rolling out above the coming times/weeks to all customers.
Though the update incorporates a whole of five security fixes, the most critical flaw rectified by Google considerations a use soon after free of charge vulnerability in its Blink rendering motor. The bug is tracked as CVE-2021-21193.
Particulars about the flaw are scarce other than that it was documented to Google by an anonymous researcher on March 9.
As is commonly the situation with actively exploited flaws, Google issued a terse statement acknowledging that an exploit for CVE-2021-21193 but refrained from sharing supplemental information until finally a majority of end users are up-to-date with the fixes and stop other risk actors from making exploits concentrating on this zero-working day.
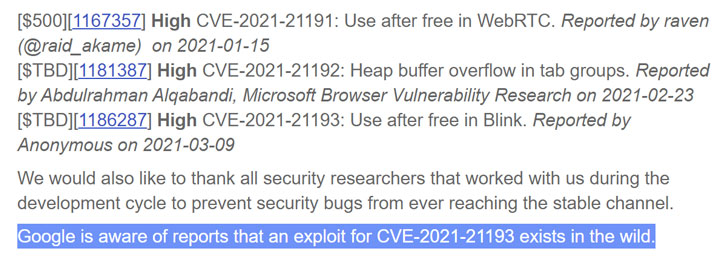
“Google is aware of studies that an exploit for CVE-2021-21193 exists in the wild,” Chrome Specialized Application Manager Prudhvikumar Bommana pointed out in a web site submit.
With this update, Google has mounted a few zero-working day flaws in Chrome given that the commence of the year.
Before this thirty day period, the business issued a deal with for an “item lifecycle issue in audio” (CVE-2021-21166) which it explained was becoming actively exploited. Then on February 4, the corporation fixed yet another actively-exploited heap buffer overflow flaw (CVE-2021-21148) in its V8 JavaScript rendering motor.
Chrome customers can update to the most recent variation by heading to Options > Aid > About Google Chrome to mitigate the risk associated with the flaw.
Located this report interesting? Comply with THN on Facebook, Twitter and LinkedIn to study more unique content material we write-up.
Some parts of this article are sourced from:
thehackernews.com


 Apple gives up on its original HomePod in favor of the $99 mini
Apple gives up on its original HomePod in favor of the $99 mini