Cybersecurity researchers have found a new malware dropper contained in as many as 9 Android apps distributed by using Google Enjoy Store that deploys a second phase malware able of attaining intrusive accessibility to the money accounts of victims as effectively as full control of their devices.
“This dropper, dubbed Clast82, utilizes a collection of approaches to keep away from detection by Google Participate in Safeguard detection, completes the analysis time period effectively, and adjustments the payload dropped from a non-destructive payload to the AlienBot Banker and MRAT,” Examine Place scientists Aviran Hazum, Bohdan Melnykov, and Israel Wernik said in a publish-up printed right now.
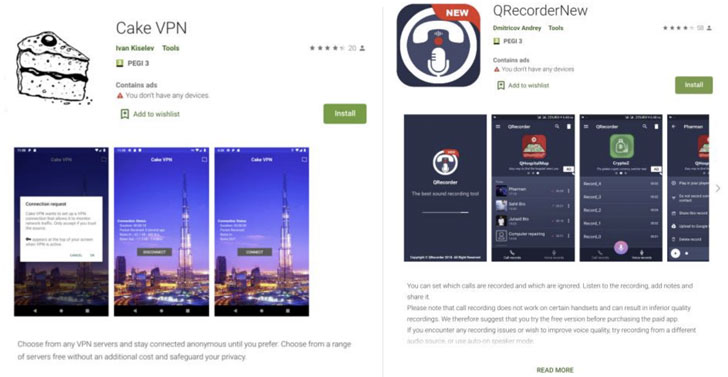
The applications that were being used for the marketing campaign involve Cake VPN, Pacific VPN, eVPN, BeatPlayer, QR/Barcode Scanner MAX, Tunes Player, tooltipnatorlibrary, and QRecorder. Following the results had been documented to Google on January 28, the rogue apps have been taken out from the Play Retail store on February 9.
Malware authors have resorted to a range of methods to bypass application retail outlet vetting mechanisms. Whether or not be it applying encryption to cover strings from investigation engines, making rogue versions of legit applications, or crafting fake testimonials to entice users into downloading the apps, fraudsters have hit back again at Google’s tries to protected the platform by constantly establishing new approaches to slip as a result of the net.
Equally well-liked are other methods like versioning, which refers to uploading a clean variation of the app to the Enjoy Retailer to make have confidence in among consumers and then sneakily introducing unwanted code at a later stage by using application updates, and incorporating time-centered delays to induce the destructive operation in an try to evade detection by Google.
Clast82 is no distinct in that it makes use of Firebase as a platform for command-and-regulate (C2) interaction and can make use of GitHub to download the destructive payloads, in addition to leveraging reputable and identified open up-source Android applications to insert the Dropper features.
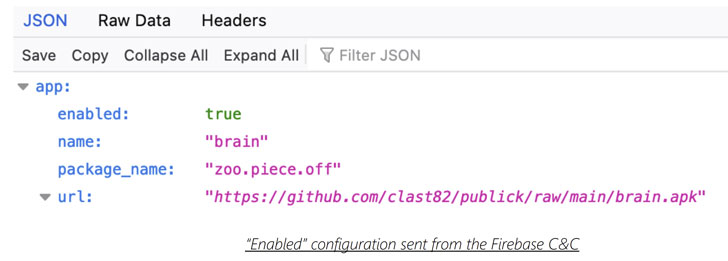
“For each software, the actor made a new developer user for the Google Perform keep, together with a repository on the actor’s GitHub account, as a result letting the actor to distribute distinct payloads to devices that ended up contaminated by each and every malicious software,” the researchers mentioned.
For occasion, the destructive Cake VPN application was observed to be based mostly on an open-sourced variation of its namesake made by a Dhaka-based developer by the name of Syed Ashraf Ullah. But as soon as the application is introduced, it takes benefit of the Firebase authentic-time database to retrieve the payload route from GitHub, which is then put in on the concentrate on gadget.
In the function the possibility to set up applications from mysterious sources has been turned off, Clast82 continuously urges the consumer just about every 5 seconds with a phony “Google Participate in Services” prompt to permit the authorization, in the end working with it to set up AlienBot, an Android banking MaaS (malware-as-a-support) able of stealing qualifications and two-component authentication codes from financial applications.

Previous thirty day period, a popular barcode scanner app with more than 10 million installations turned rogue with a one update immediately after its possession changed fingers. In a very similar development, a Chrome extension by the name of The Great Suspender was deactivated pursuing reports that the incorporate-on stealthily extra options that could be exploited to execute arbitrary code from a remote server.
“The hacker driving Clast82 was in a position to bypass Google Play’s protections employing a artistic, but regarding, methodology,” Hazum mentioned. “With a basic manipulation of conveniently available 3rd party means — like a GitHub account, or a FireBase account — the hacker was in a position to leverage easily accessible methods to bypass Google Enjoy Store’s protections. The victims considered they were being downloading an innocuous utility app from the formal Android market, but what they ended up really finding was a unsafe trojan coming straight for their monetary accounts.”
Observed this report appealing? Stick to THN on Facebook, Twitter and LinkedIn to go through extra special content material we submit.
Some parts of this article are sourced from:
thehackernews.com


 NCSC: Don’t Fall for Mother’s Day Scams This Week
NCSC: Don’t Fall for Mother’s Day Scams This Week