A new trojan identified as Android.Cynos.7.origin, built to gather Android users’ system facts and phone figures, was observed in 190 games mounted on about 9M Android gadgets.
Why would a recreation about a cat’s “cute diary” want permission to make phone phone calls or suss out your location?
It doesn’t: “Cat adorable diary” is just one of 190 trojanized game titles that Health care provider Web malware analysts have observed on AppGallery, the formal application shop for Huawei Android.
They’re littering the Android landscape. In a report released on Tuesday, Medical professional Web approximated that additional than 9,300,000 Android system proprietors have set up the perilous games.
According to researchers, the key intent of the slew of malware-laced apps – which contains hundreds of kid-attractive entries, which include video games, simulators, platformers, arcades, procedures and shooters – is not to satisfy users’ sweet-kitty and shoot-the-negative-fellas lust.
Somewhat, they are rigged with a new Android trojan, tracked by the analysts as Android.Cynos.7.origin, the major function of which is to lap up users’ phone numbers and machine information and to make funds by milking the information to inflict advertisements, in accordance scientists.
Fun and Online games and Details Exfiltration
Medical professional Web furnished a handful of illustrations of the trojan-containing game titles, some of which are targeting Russian-talking end users and which have Russian titles and descriptions, and some of which concentrate on Chinese or international audiences.

“Cat activity room” – 427,000+ installations. Supply: Health practitioner Web.
A single of them – the “快点躲起来” activity – which, according to Google Translator, suggests “Hurry up and hide” in English – has been downloaded around 2,000,000 moments, according to the investigation.
Here’s the total listing of the 190 applications the researchers are pinpointing as destructive.
What the Applications Do With All those Permissions
Health care provider Web stated that the Android.Cynos.7.origin trojan is just one of the modifications of the Cynos malware platform – a module that can be built-in into Android applications so as to squeeze money out of products. Malware analysts have identified about Cynos given that at the very least 2014, the analysts explained.
When the destructive apps are downloaded, they question for permission to make and take care of phone calls, as proven in the monitor capture underneath.
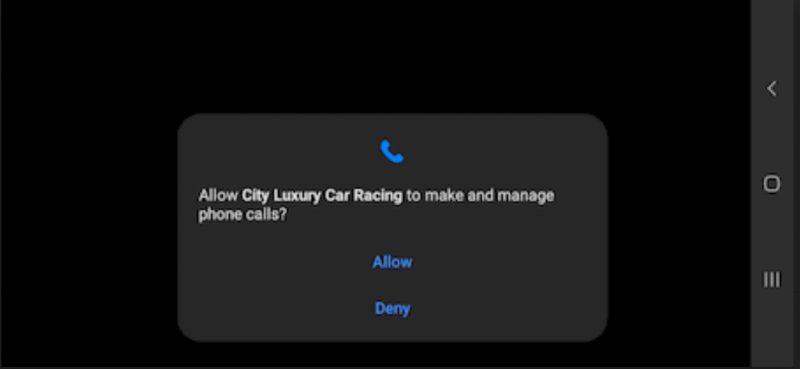
The trojan requests authorization to make and regulate phone phone calls. Supply: Health care provider Web.
“That will allow the trojan to obtain access to particular data,” the analysts defined. Specifically, right after a person grants people permissions, the trojans collects and exfiltrates all of the subsequent details to a remote server:
- User mobile phone amount
- Gadget location primarily based on GPS coordinates or the cellular network and Wi-Fi accessibility point info (when the application has authorization to entry place)
- Several cell network parameters, such as the network code and cell state code also, GSM mobile ID and intercontinental GSM location region code (when the software has permission to entry spot)
- Several complex specs of the product
- Many parameters from the trojanized app’s metadata
- Some of its variations have really aggressive operation: they ship high quality SMS, intercept incoming SMS, download and start extra modules, and obtain and install other applications. The main performance of the edition discovered by our malware analysts is amassing the information and facts about buyers and their gadgets and exhibiting ads.
For what it’s really worth, some of the Cynos versions are even more aggressive that creep into the realm of spy ware or extra, in accordance to Health practitioner Web: “They mail top quality SMS, intercept incoming SMS, obtain and launch more modules, and download and put in other apps.”
Having said that, the 190 apps its analysts found are primarily developed to accumulate the higher than-talked about record of information and facts about customers and their gadgets and to show advertisements.
Nevertheless, son’t shrug these off, Physician Web analysts cautioned. These games are built to be employed by youngsters, which can make them a great deal dangerous: “At 1st look, a mobile phone variety leak may perhaps seem like an insignificant problem. Nonetheless in reality, it can seriously harm people, especially specified the reality that little ones are the games’ major focus on audience.
“Even if the mobile phone range is registered to an adult, downloading a child’s sport might highly most likely show that the baby is the one particular who [is] really applying the cellular phone. It is very uncertain that mom and dad would want the over facts about the phone to be transferred not only to unidentified international servers, but to anyone else in basic.”
Huawei Yanked the Poor Apps
This isn’t the initial time that Huawei’s AppGallery has been infused with malware. In April, Health practitioner Web noted that it experienced uncovered the application retail outlet infested with apps that contained the Joker trojan: apps that were being downloaded by unwitting consumers to more than 538,000 equipment.
Physician Web notified Huawei about the Cynos-infested malicious apps in its Android gallery. Huawei subsequently removed them all. The enterprise hadn’t responded to Threatpost’s ask for for comment by the time this posting was released, but it did mail this assertion to BleepingComputer:
“AppGallery’s constructed-in security procedure swiftly determined the likely risk in these applications. We are now actively working with afflicted developers to troubleshoot their applications. After we can ensure that the applications are all obvious, they will be re-outlined on AppGallery so consumers can obtain their favourite apps yet again and proceed having fun with them.
“Protecting network security and consumer privacy is Huawei’s precedence. We welcome all 3rd-bash oversight and responses to guarantee we supply on this determination. We will continue on to collaborate closely with our partners, and at the exact time, hire the most state-of-the-art and modern systems to safeguard our users’ privacy.”
Image credit score: MaxPixel.
There’s a sea of unstructured information on the internet relating to the latest security threats. Sign-up Now to study key ideas of pure language processing (NLP) and how to use it to navigate the facts ocean and incorporate context to cybersecurity threats (without the need of currently being an pro!). This Dwell, interactive Threatpost Town Hall, sponsored by Fast 7, will feature security researchers Erick Galinkin of Swift7 and Izzy Lazerson of IntSights (a Rapid7 firm), in addition Threatpost journalist and webinar host, Becky Bracken.
Some parts of this article are sourced from:
threatpost.com


 Splice's music creation plans are going on sale for Black Friday
Splice's music creation plans are going on sale for Black Friday