Business communications program maker 3CX on Thursday confirmed that numerous variations of its desktop application for Windows and macOS are impacted by a supply chain attack.
The variation numbers contain 18.12.407 and 18.12.416 for Windows and 18.11.1213, 18.12.402, 18.12.407, and 18.12.416 for macOS.
The firm said it is engaging the products and services of Google-owned Mandiant to assessment the incident. In the interim, it truly is urging its consumers of self-hosted and on-premise versions of the application to update to edition 18.12.422.
“3CX Hosted and StartUP end users do not require to update their servers as we will be updating them around the night routinely,” 3CX CEO Nick Galea explained in a post on Thursday. “Servers will be restarted and the new Electron App MSI/DMG will be set up on the server.”
Proof readily available so considerably factors to either a compromise of 3CX’s software make pipeline to distribute Windows and macOS versions of the app offer, or alternatively, the poisoning of an upstream dependency. The scale of the attack is now unidentified.
The earliest period of possibly malicious exercise is said to have been detected on or all over March 22, 2023, according to a submit on the 3CX forum, while preparations for the marketing campaign are reported to have commenced no afterwards than February 2022.
3CX claimed the preliminary notify flagging a likely security challenge in its app past week was addressed as a “wrong optimistic” owing to the fact that none of the antivirus engines on VirusTotal labeled it as suspicious or malware.
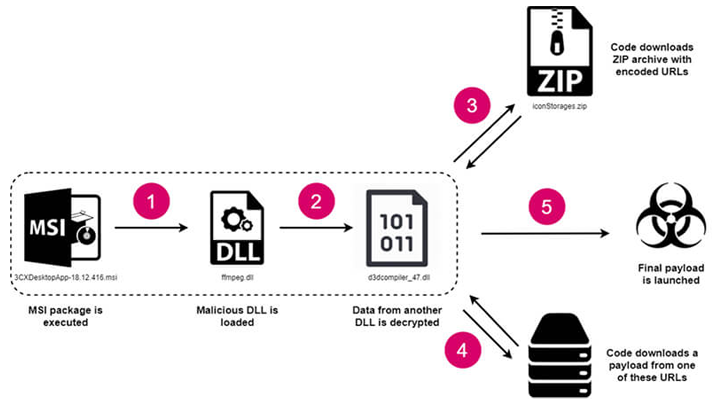
The Windows model of the attack leveraged a method referred to as DLL facet-loading to load a rogue library referred to as “ffmpeg.dll” which is made to go through encrypted shellcode from one more DLL known as “d3dcompiler_47.dll.”
This included accessing a GitHub repository to retrieve an ICO file containing URLs hosting the last-phase payload, an information stealer (dubbed Iconic Stealer or SUDDENICON) able of harvesting system info and sensitive knowledge saved in web browsers.
“The decision of these two DLLs – ffmpeg and d3dcompiler_47 – by the danger actors guiding this attack was no incident,” ReversingLabs security researcher Karlo Zanki claimed.
“The target in dilemma, 3CXDesktopApp, is built on the Electron open up source framework. Equally of the libraries in concern usually ship with the Electron runtime and, for that reason, are not likely to elevate suspicion inside shopper environments.”
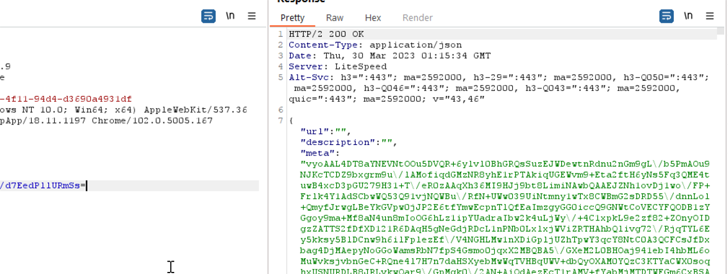
 SUDDENICON downloading a new executable
SUDDENICON downloading a new executable
The macOS attack chain, in the very same vein, bypassed Apple’s notarization checks to down load an unknown payload from a command-and-management (C2) server which is presently unresponsive.
“The macOS variation does not use GitHub to retrieve its C2 server,” Volexity stated, which is monitoring the action underneath the cluster UTA0040. “In its place, a record of C2 servers is saved in the file encoded with a one byte XOR essential, 0x7A.”
THN WEBINARBecome an Incident Reaction Pro!
Unlock the insider secrets to bulletproof incident reaction – Learn the 6-Stage process with Asaf Perlman, Cynet’s IR Chief!
Never Overlook Out – Preserve Your Seat!
Cybersecurity business CrowdStrike, in an advisory of its own, has attributed the attack with large self-assurance to Labyrinth Chollima (aka Nickel Academy), a North Korea-aligned point out-sponsored actor.
“The activity, which targets a lot of companies across a wide range of verticals without the need of any apparent patterns, has been attributed to Labyrinth Chollima dependent on observed network infrastructure uniquely associated with that adversary, similar installation approaches, and a reused RC4 essential,” Adam Meyers, senior vice president of intelligence at CrowdStrike, advised The Hacker News.
“The trojanized 3CX purposes invoke a variant of ArcfeedLoader, malware uniquely attributed to Labyrinth Chollima.”
Labyrinth Chollima, per the Texas-centered company, is a subset of the Lazarus Team, which also constitutes Silent Chollima (aka Andariel or Nickel Hyatt) and Stardust Chollima (aka BlueNoroff or Nickel Gladstone).
The team “has been energetic at minimum given that 2009 and typically tries to crank out profits by concentrating on crypto and monetary corporations,” Meyers claimed, incorporating it can be “likely affiliated with Bureau 121 of the DPRK’s Reconnaissance Basic Bureau (RGB) and largely conducts espionage functions and profits generation techniques.”
Uncovered this article fascinating? Follow us on Twitter and LinkedIn to read much more exceptional information we publish.
Some parts of this article are sourced from:
thehackernews.com


 Ukrainian Police Bust Multimillion-Dollar Phishing Gang
Ukrainian Police Bust Multimillion-Dollar Phishing Gang