LemonDuck, a cross-system cryptocurrency mining botnet, is focusing on Docker to mine cryptocurrency on Linux methods as portion of an lively malware campaign.
“It runs an nameless mining procedure by the use of proxy pools, which hide the wallet addresses,” CrowdStrike stated in a new report. “It evades detection by concentrating on Alibaba Cloud’s checking service and disabling it.”
Acknowledged to strike both Windows and Linux environments, LemonDuck is generally engineered for abusing the method sources to mine Monero. But it really is also capable of credential theft, lateral movement, and facilitating the deployment of supplemental payloads for comply with-on routines.
“It works by using a wide vary of spreading mechanisms — phishing email messages, exploits, USB units, brute pressure, between other individuals — and it has revealed that it can speedily just take advantage of news, occasions, or the launch of new exploits to run successful campaigns,” Microsoft detailed in a technical generate-up of the malware last July.
In early 2021, attack chains involving LemonDuck leveraged the then recently patched Exchange Server vulnerabilities to acquire access to out-of-date Windows devices, prior to downloading backdoors and facts stealers, including Ramnit.
The most recent campaign spotted by CrowdStrike can take advantage of exposed Docker APIs as an initial obtain vector, using it to run a rogue container to retrieve a Bash shell script file that’s disguised as a harmless PNG picture file from a distant server.
An investigation of historic facts displays that related graphic file droppers hosted on LemonDuck-linked domains have been set to use by the threat actor because at minimum January 2021, the cybersecurity organization famous.
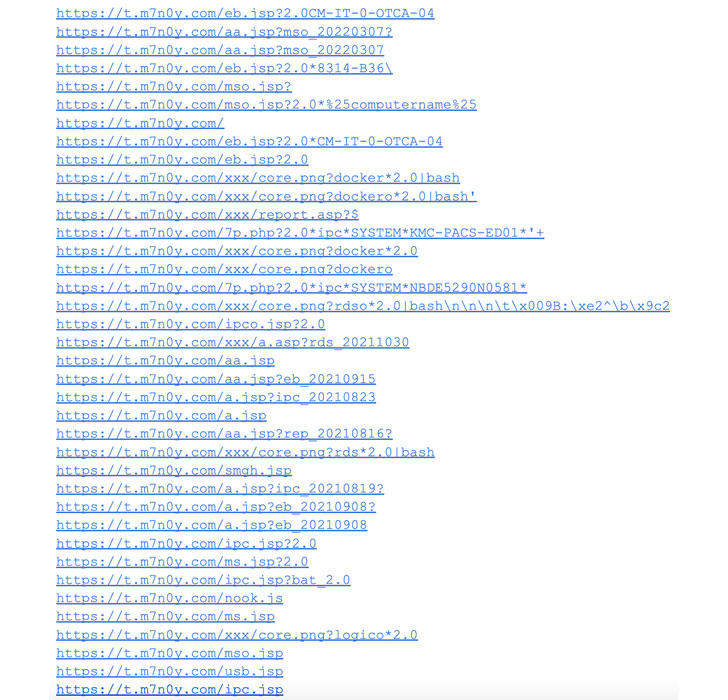
The dropper files are important to launching the attack, with the shell script downloading the genuine payload that then kills competing procedures, disables Alibaba Cloud’s checking companies, and finally downloads and runs the XMRig coin miner.
With compromised cloud instances starting to be a hotbed for illicit cryptocurrency mining pursuits, the findings underscore the need to safe containers from prospective challenges in the course of the software program supply chain.
TeamTNT targets AWS, Alibaba Cloud
The disclosure will come as Cisco Talos uncovered the toolset of a cybercrime group named TeamTNT, which has a record of focusing on cloud infrastructure for cryptojacking and putting backdoors.
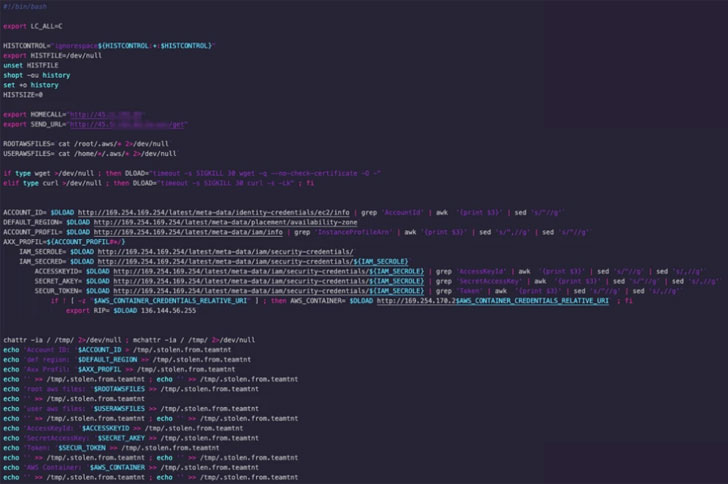
The malware payloads, which are stated to have been modified in response to earlier public disclosures, are generally developed to focus on Amazon Web Companies (AWS) even though simultaneously concentrated on cryptocurrency mining, persistence, lateral movement, and disabling cloud security options.
“Cybercriminals who are outed by security scientists have to update their applications in purchase to proceed to run efficiently,” Talos researcher Darin Smith stated.
“The tools made use of by TeamTNT exhibit that cybercriminals are more and more comfy attacking modern day environments these as Docker, Kubernetes, and public cloud providers, which have historically been avoided by other cybercriminals who have as an alternative focused on on-premise or mobile environments.”
Spring4Shell exploited for cryptocurrency mining
That’s not all. In yet one more occasion of how menace actors immediately co-choose recently disclosed flaws into their attacks, the critical distant code execution bug in Spring Framework (CVE-2022-22965) has been weaponized to deploy cryptocurrency miners.
The exploitation tries make use of a tailor made web shell to deploy the cryptocurrency miners, but not just before turning off the firewall and terminating other virtual currency miner processes.
“These cryptocurrency miners have the opportunity to have an impact on a big selection of users, primarily considering that Spring is the most extensively utilised framework for producing enterprise-stage programs in Java,” Craze Micro scientists Nitesh Surana and Ashish Verma explained.
Found this posting intriguing? Stick to THN on Fb, Twitter and LinkedIn to browse additional exceptional articles we put up.
Some parts of this article are sourced from:
thehackernews.com

 Sonos is reportedly releasing a $250 soundbar in June
Sonos is reportedly releasing a $250 soundbar in June