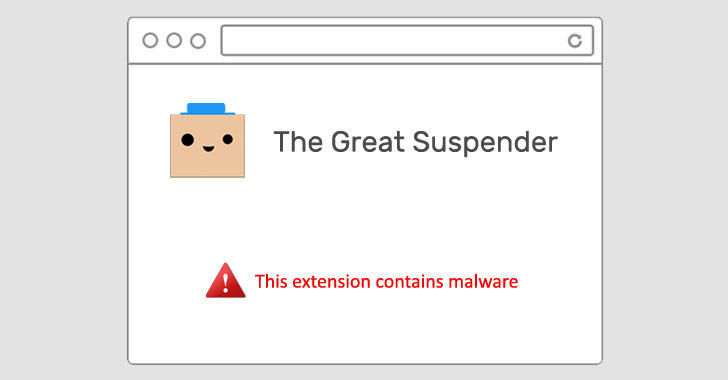
Google on Thursday removed The Good Suspender, a common Chrome extension utilised by thousands and thousands of users, from its Chrome Web Retail store for containing malware. It also took the uncommon move of deactivating it from users’ personal computers.
“This extension contains malware,” read through a terse notification from Google, but it has considering the fact that emerged that the add-on stealthily included attributes that could be exploited to execute arbitrary code from a remote server, such as tracking customers on the web and committing marketing fraud.
“The old maintainer seems to have marketed the extension to get-togethers unknown, who have malicious intent to exploit the customers of this extension in marketing fraud, tracking, and extra,” Calum McConnell explained in a GitHub submit.

The extension, which experienced much more than two million installs just before it was disabled, would suspend tabs that are not in use, changing them with a blank gray display screen till they had been reloaded on returning to the tabs in issue.
Signals of the extension’s shady actions experienced been going the rounds since November, major Microsoft to block the extension (v7.1.8) on Edge browsers past November.
According to The Sign-up, Dean Oemcke, the extension’s unique developer, is reported to have sold the extension in June 2020 to an unfamiliar entity, next which two new variations ended up produced instantly to consumers by means of the Chrome Web Retail store (7.1.8 and 7.1.9).
Customers of the extension can get well the tabs using a workaround listed here, or as an different, can also use the most current version obtainable on GitHub (v7.1.6) by enabling Chrome Developer method.
But turning on the Developer manner can have other penalties, as well, as uncovered by security researcher Bojan Zdrnja, who disclosed a novel approach that lets risk actors abuse the Chrome sync characteristic to bypass firewalls and build connections to attacker-managed servers for facts exfiltration.
Zdrnja mentioned the adversary created a destructive security include-on that masqueraded as Forcepoint Endpoint Chrome Extension for Windows, which was then mounted immediately on the browser soon after enabling Developer method.
“While there are some restrictions on sizing of data and amount of requests, this is essentially great for C&C instructions (which are usually little), or for stealing modest, but sensitive information – these types of as authentication tokens,” Zdrnja said.
But given that this attack needs bodily entry to a concentrate on technique, it is unlikely to be solved by Google.
Uncovered this posting appealing? Stick to THN on Fb, Twitter and LinkedIn to read far more distinctive content material we post.
Some parts of this article are sourced from:
thehackernews.com

 SpaceX filing reveals Starlink internet service has over 10,000 users
SpaceX filing reveals Starlink internet service has over 10,000 users