Intelligence businesses in the U.K. and the U.S. disclosed aspects of a new botnet malware termed Cyclops Blink that is been attributed to the Russian-backed Sandworm hacking group and deployed in assaults dating back again to 2019.
“Cyclops Blink appears to be a substitute framework for the VPNFilter malware exposed in 2018, which exploited network devices, mostly small workplace/house place of work (SOHO) routers, and network-connected storage (NAS) devices,” the companies said. “In widespread with VPNFilter, Cyclops Blink deployment also appears indiscriminate and prevalent.”
The joint government advisory comes from the U.K. National Cyber Security Centre (NCSC), the Cybersecurity and Infrastructure Security Company (CISA), the Countrywide Security Company (NSA), and the Federal Bureau of Investigation (FBI) in the U.S.

Sandworm, aka Voodoo Bear, is the identify assigned to a remarkably state-of-the-art adversary running out of Russia that is acknowledged to be lively considering the fact that at the very least 2008. The hacking group has shown a distinct focus on targeting entities in Ukraine and is alleged to be behind the Ukrainian power sector assaults that induced prevalent electricity outages in late 2015.
The risk actor, in October 2020, was formally connected to Russia’s Common Workers Principal Intelligence Directorate (GRU) Major Centre for Unique Systems (GTsST) armed service device 74455.
VPNFilter was initial documented by Cisco Talos in May well 2018, describing it as a “complex modular malware method” that shares overlaps with the Sandworm’s BlackEnergy malware and attributes capabilities to support intelligence-assortment and damaging cyber attack functions.
The IoT botnet malware was located to have compromised a lot more than 500,000 routers in at minimum 54 international locations, focusing on devices from Linksys, MikroTik, NETGEAR, and TP-Link, ASUS, D-Backlink, Huawei, Ubiquiti, QNAP, UPVEL, and ZTE.
That exact month, the U.S. govt announced the seizure and takedown of a vital internet area employed for the assaults, urging homeowners of SOHO and NAS appliances that may be contaminated to reboot their units to temporarily disrupt the malware.
As of January 2021, an investigation from Craze Micro identified “residual bacterial infections” continue to remaining on 1000’s of networks several years following sinkholing VPNFilter, even as the Sandworm actor simultaneously opted to retool the malware in reaction to community disclosures.
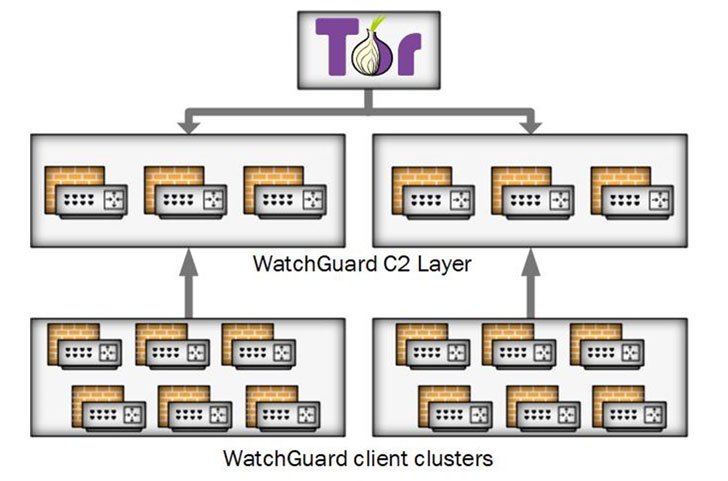
Cyclops Blink, as the substitute is called, is thought to have been in action due to the fact at least June 2019 generally placing its eyes on WatchGuard firewall gadgets, whilst the businesses claimed that the malware could be repurposed to strike other architectures and firmware.

Even a lot more concerningly, the botnet malware is deployed as a phony update and is able of surviving reboots and firmware upgrades, with command-and-control (C2) communications facilitated in excess of the Tor anonymity network.
“The malware by itself is subtle and modular with primary core operation to beacon machine information back again to a server and permit documents to be downloaded and executed,” the researchers observed. “There is also performance to insert new modules whilst the malware is running, which enables Sandworm to apply added capability as needed.”
WatchGuard, in an impartial bulletin, named it a point out-sponsored botnet that leveraged a beforehand discovered security vulnerability in the Firebox firmware as the first access vector. The shortcoming was ultimately resolved as of May 2021.
“Based on present-day estimates, Cyclops Blink may possibly have affected approximately 1% of active WatchGuard firewall appliances,” the organization claimed. “Only those appliances that experienced been configured to have management open to the Internet are vulnerable to Cyclops Blink.”
The Seattle-headquartered firm is also recommending clients to right away abide by the methods outlined in the 4-Move Cyclops Blink Prognosis and Remediation Plan to diagnose and eliminate the danger posed by potential destructive action from the botnet.
The findings appear as Russia formally launched a complete scale army procedure to invade Ukraine, just as its IT infrastructure was crippled by a string of facts wiper and distributed denial-of-service (DDoS) assaults.
Located this posting fascinating? Observe THN on Facebook, Twitter and LinkedIn to read far more exceptional material we publish.
Some parts of this article are sourced from:
thehackernews.com