The U.S. Cybersecurity and Infrastructure Security Company (CISA) has warned of active exploitation of two security flaws impacting Zabbix open up-resource business monitoring platform, including them to its Known Exploited Vulnerabilities Catalog.
On leading of that, CISA is also recommending that Federal Civilian Govt Department (FCEB) organizations patch all devices in opposition to the vulnerabilities by March 8, 2022 to lessen their publicity to potential cyberattacks.
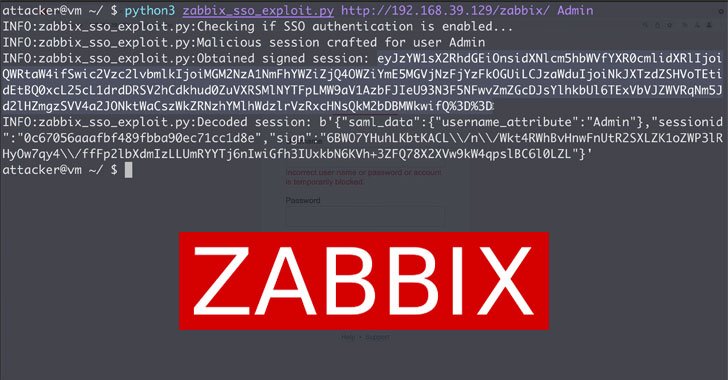
Tracked as CVE-2022-23131 (CVSS score: 9.8) and CVE-2022-23134 (CVSS score: 5.3), the shortcomings could direct to the compromise of entire networks, enabling a malicious unauthenticated actor to escalate privileges and achieve admin obtain to the Zabbix Frontend as very well as make configuration variations.
Thomas Chauchefoin from SonarSource has been credited with identifying and reporting the two flaws, which impact Zabbix Web Frontend versions up to and together with 5.4.8, 5..18 and 4..36. The issues have considering the fact that been tackled in variations 5.4.9, 5..9 and 4..37 transported late December 2021.
Equally the flaws are the end result of what the firm calls “unsafe session storage,” allowing for attackers to bypass authentication and execute arbitrary code. It can be, on the other hand, value pointing out that the flaws only influence scenarios where by Security Assertion Markup Language (SAML) Solitary sign-on (SSO) authentication is enabled.
“Normally deliver access to sensible solutions with extended internal accesses (e.g., orchestration, checking) over VPNs or a restricted established of IP addresses, harden filesystem permissions to avert unintended changes, remove set up scripts, and many others.,” Chauchefoin reported.
Discovered this short article interesting? Follow THN on Facebook, Twitter and LinkedIn to read more special content material we article.
Some parts of this article are sourced from:
thehackernews.com


 US, UK Agencies Warn of New Russian Botnet Built from Hacked Firewall Devices
US, UK Agencies Warn of New Russian Botnet Built from Hacked Firewall Devices