The Computer Emergency Response Group of Ukraine (CERT-UA) has warned of phishing assaults that deploy an details-thieving malware known as Jester Stealer on compromised techniques.
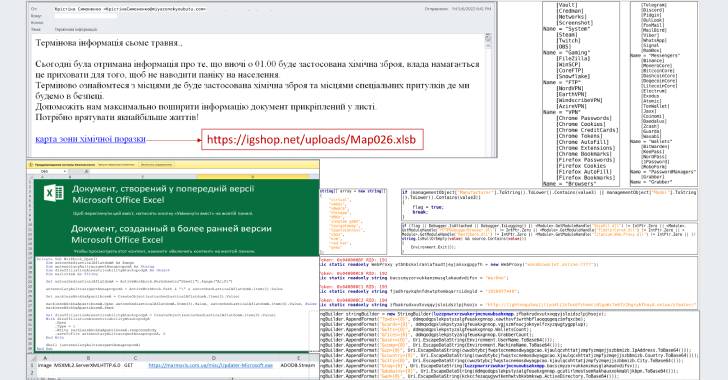
The mass email marketing campaign carries the matter line “chemical attack” and incorporates a connection to a macro-enabled Microsoft Excel file, opening which qualified prospects to computers obtaining infected with Jester Stealer.
The attack, which demands opportunity victims to allow macros just after opening the doc, works by downloading and executing an .EXE file that is retrieved from compromised web assets, CERT-UA detailed.
Jester Stealer, which was first documented by Cyble in February 2022, will come with functions to steal and transmit login credentials, cookies, and credit history card facts alongside with information from passwords supervisors, chat messengers, email clientele, crypto wallets, and gaming applications to the attackers.
“The hackers get the stolen data through Telegram using statically configured proxy addresses (e.g., within TOR),” the company mentioned. “They also use anti-examination procedures (anti-VM/debug/sandbox). The malware has no persistence system — it is deleted as quickly as its procedure is completed.”
The Jester Stealer campaign coincides with yet another phishing attack that CERT-UA has attributed to the Russian nation-condition actor tracked as APT28 (aka Fancy Bear aka Strontium).
The e-mail, titled “Кібератака” (that means cyberattack in Ukrainian), masquerade as a security notification from CERT-UA and come with a RAR archive file “UkrScanner.rar” attachment that, when opened, deploys a malware known as CredoMap_v2.
“Unlike prior versions of this stealer malware, this a person takes advantage of the HTTP protocol for facts exfiltration,” CERT-UA pointed out. “Stolen authentication info will be despatched to a web resource, deployed on the Pipedream system, via the HTTP Publish requests.”
The disclosures follow equivalent conclusions from Microsoft’s Electronic Security Device (DSU) and Google’s Danger Investigation Team (TAG) about Russian condition-sponsored hacking crews carrying out credential and info theft operations in Ukraine.
Discovered this posting interesting? Follow THN on Facebook, Twitter and LinkedIn to read additional exclusive content we post.
Some parts of this article are sourced from:
thehackernews.com

 U.S. Offering $10 Million Reward for Information on Conti Ransomware Hackers
U.S. Offering $10 Million Reward for Information on Conti Ransomware Hackers